Ababil a bo ne be
Welcome to Memetic Warfare. My cup runneth over this week with a second post, taking a look at yet another Iranian front group.
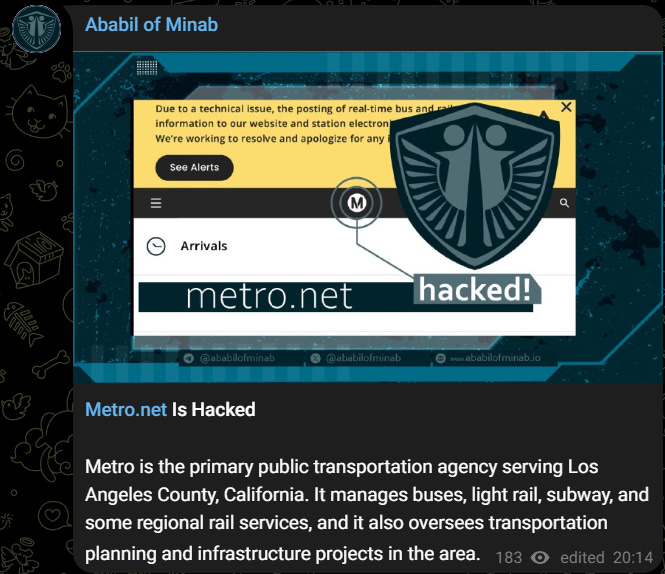
It all began a bit over a week ago when LA’s metro authority confirmed that it was popped.
The intrusion only led to some noncritical systems being taken down, and service wasn’t disrupted meaningfully. An Iranian group took credit for the operation, and Dataminr was the first to report it.
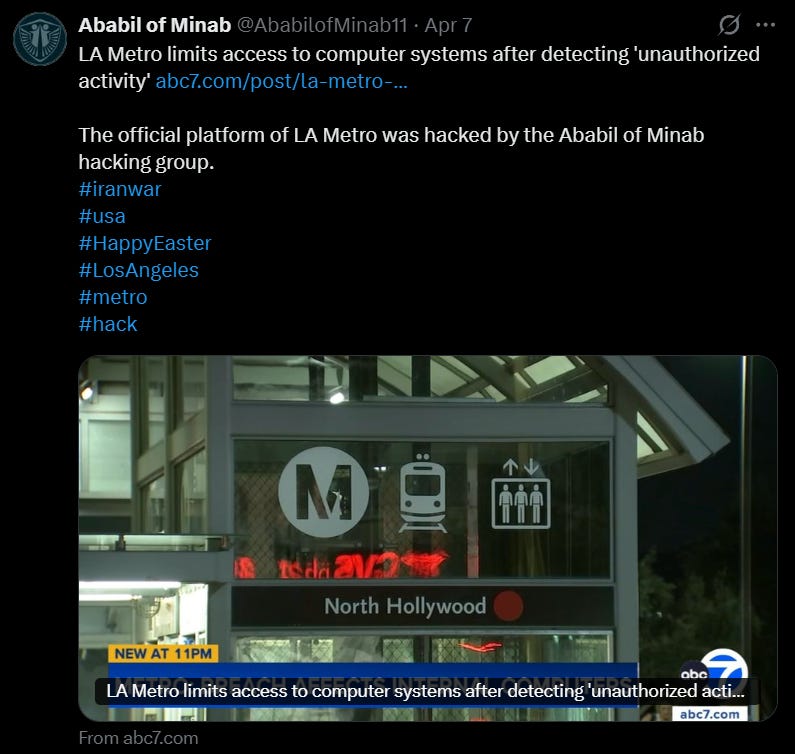
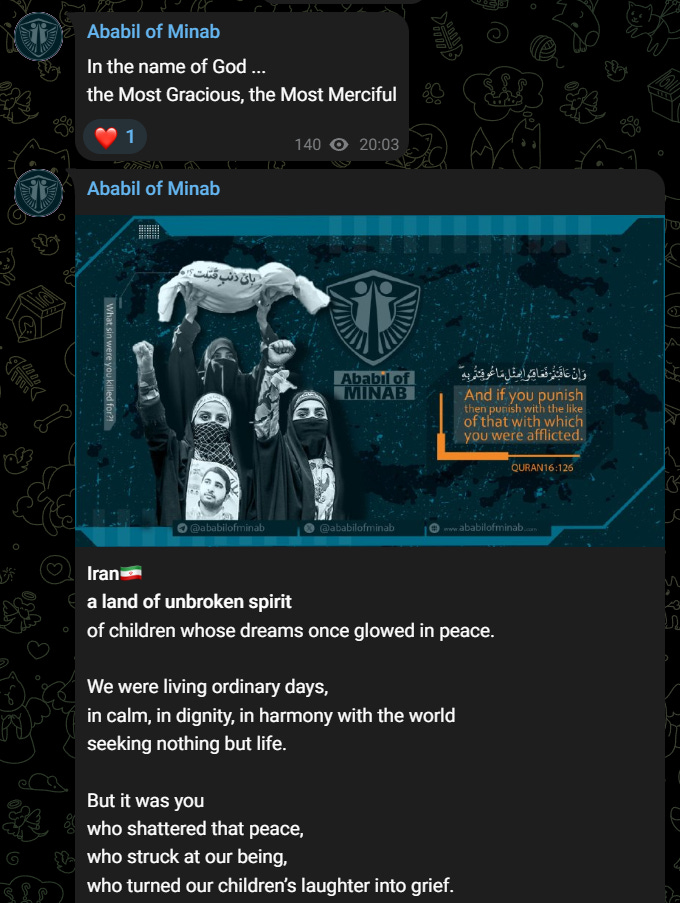
The name itself is a reference to the Quran, with the ababil itself meaning a “flock”. This isn’t just any flock, but a specific one referred to in the Quran as having protected Mecca from an invading army. The reference to Minab is to the school bombed by the US in the Israel/US-Iran war, which has turned into a trope of Iranian propaganda.
Most of the overtly Islamic references I’ve seen in fronts have been related to ASA, but there have been others, as well as other bird-brained Iranian/Hizballah related operations.
You can see the logo and aesthetics clearly here:
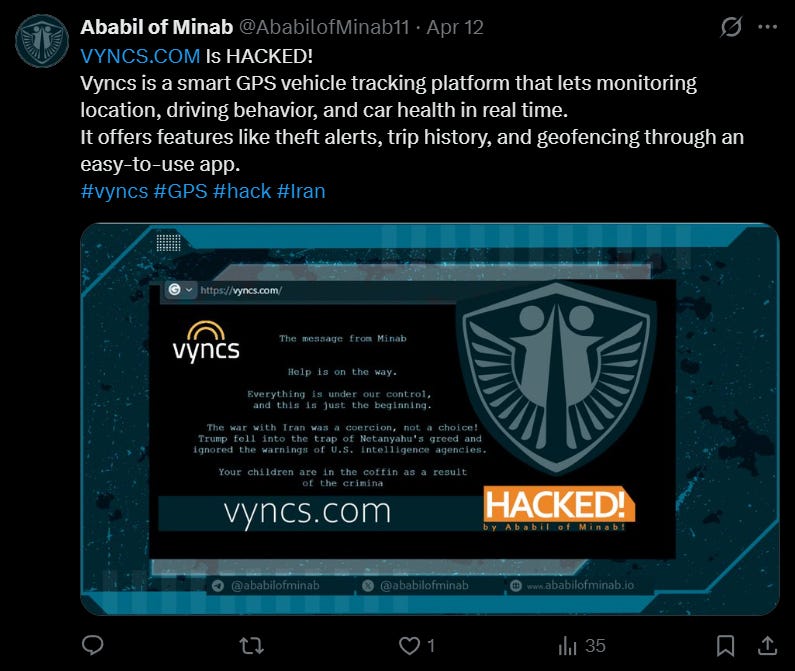
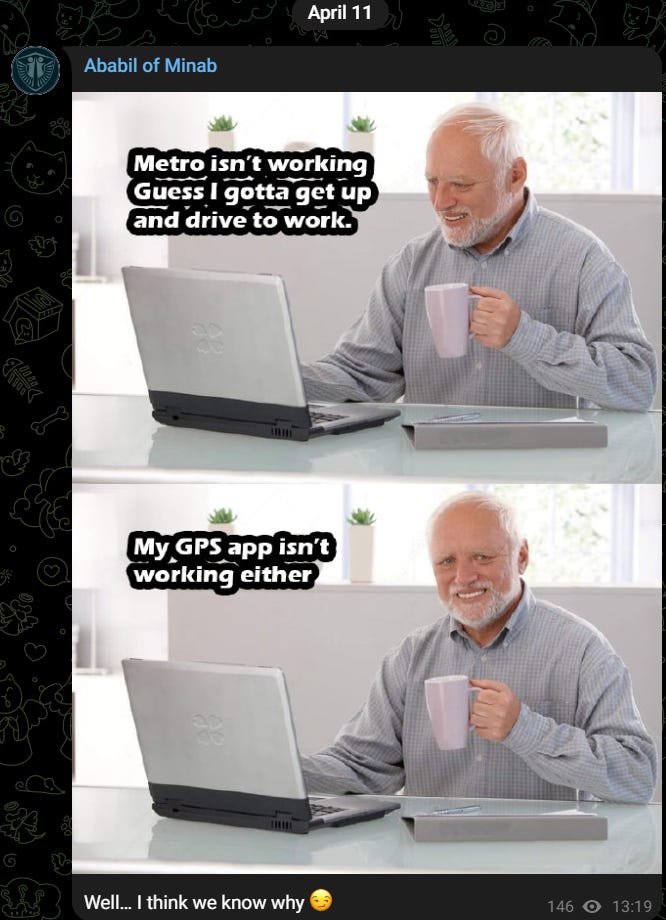
They’ve had two main targets so far. The most recent is Vyncs, a GPS company, which they hit with a defacement on April 11th:
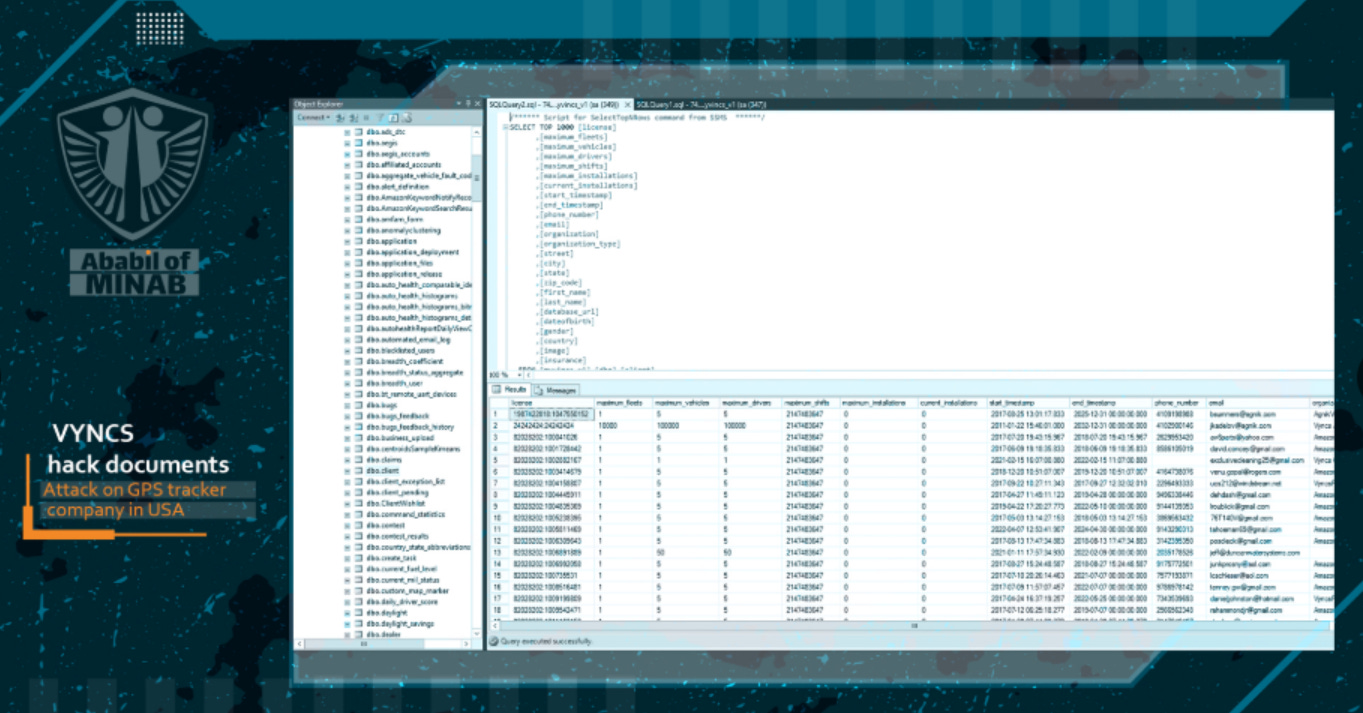
They include screenshots of the company’s SQL database and other internal systems:
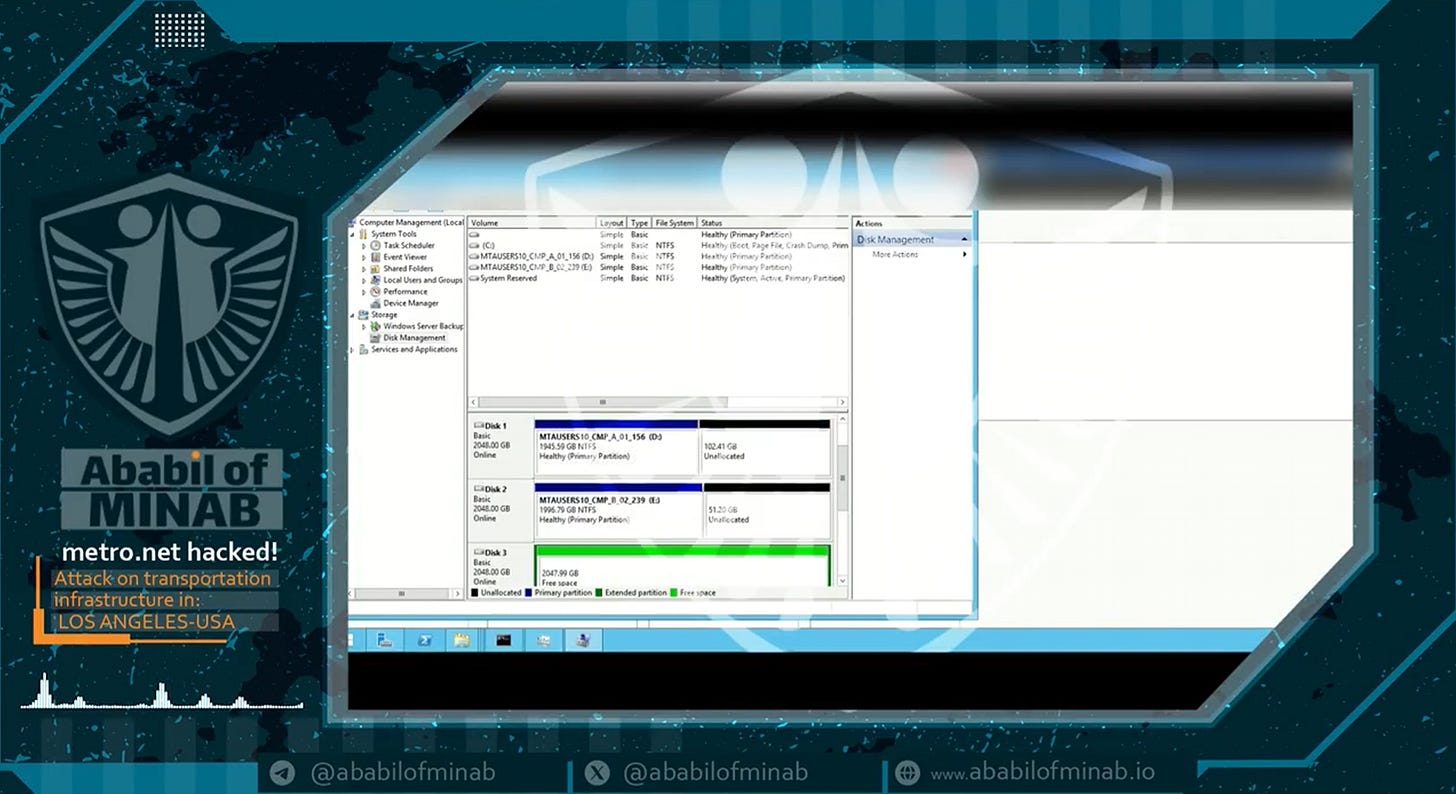
Their first operation, as stated, was against Metro.net, LA county’s transit authority:
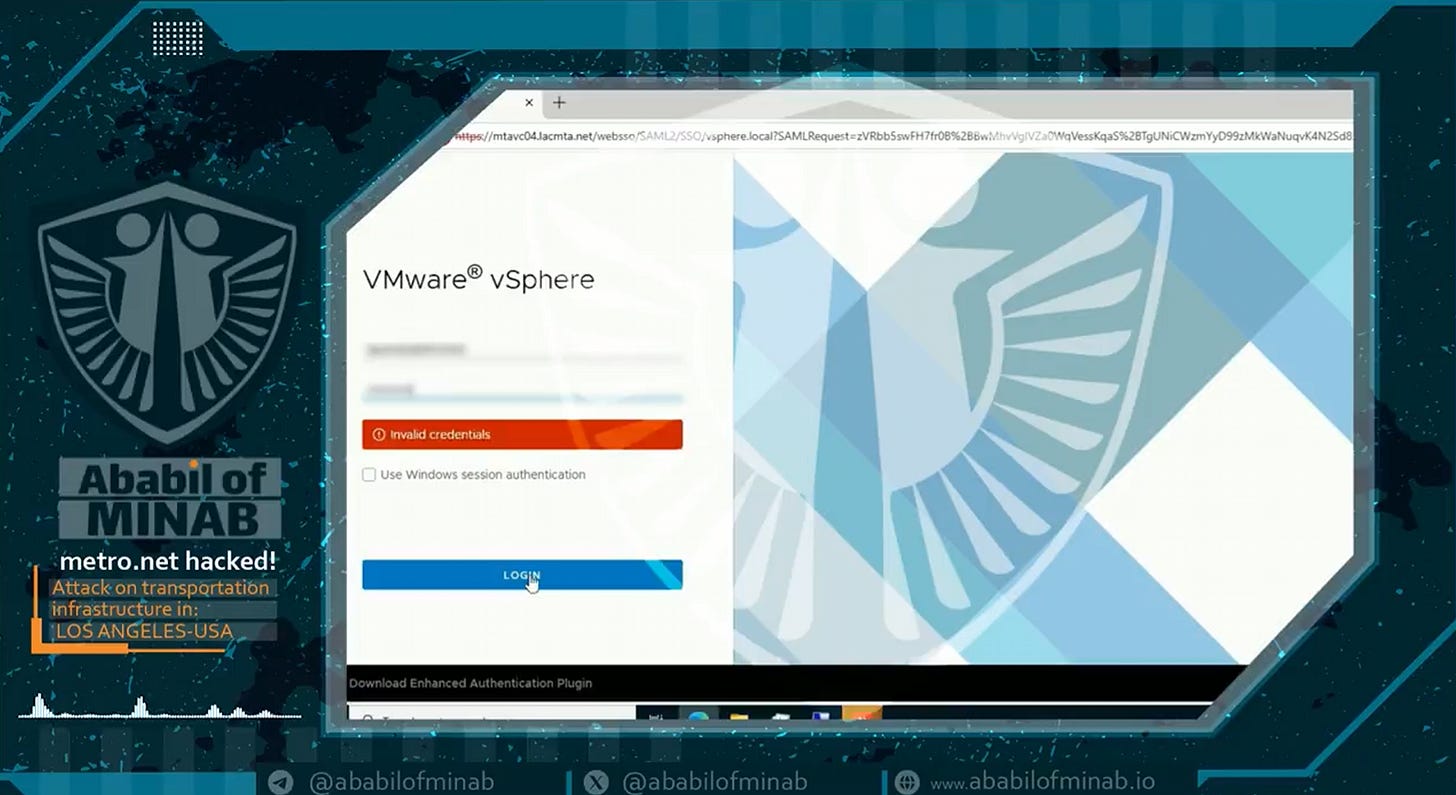
They managed to get in to their VMWare environment:
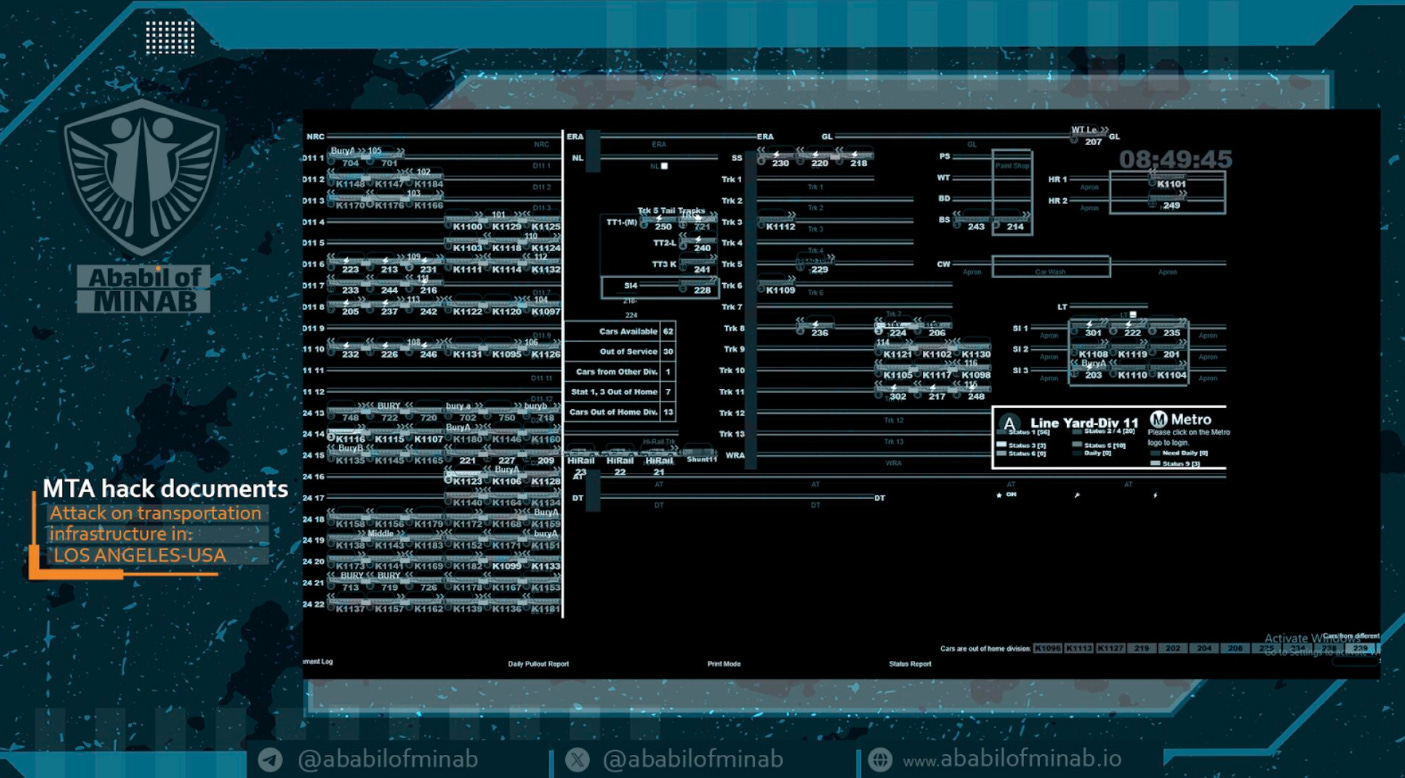
From there, they manually deleted clusters and uploaded some footage from street cameras:
They also gained access to some OT infrastructure, in this case managing a rail yard:
They even engage in real memery, which is something you don’t often see from the front groups themselves, and is more the type of thing I’d expect from Mr. Soul/cyberav3ngers and less from ASA or even the MOIS.
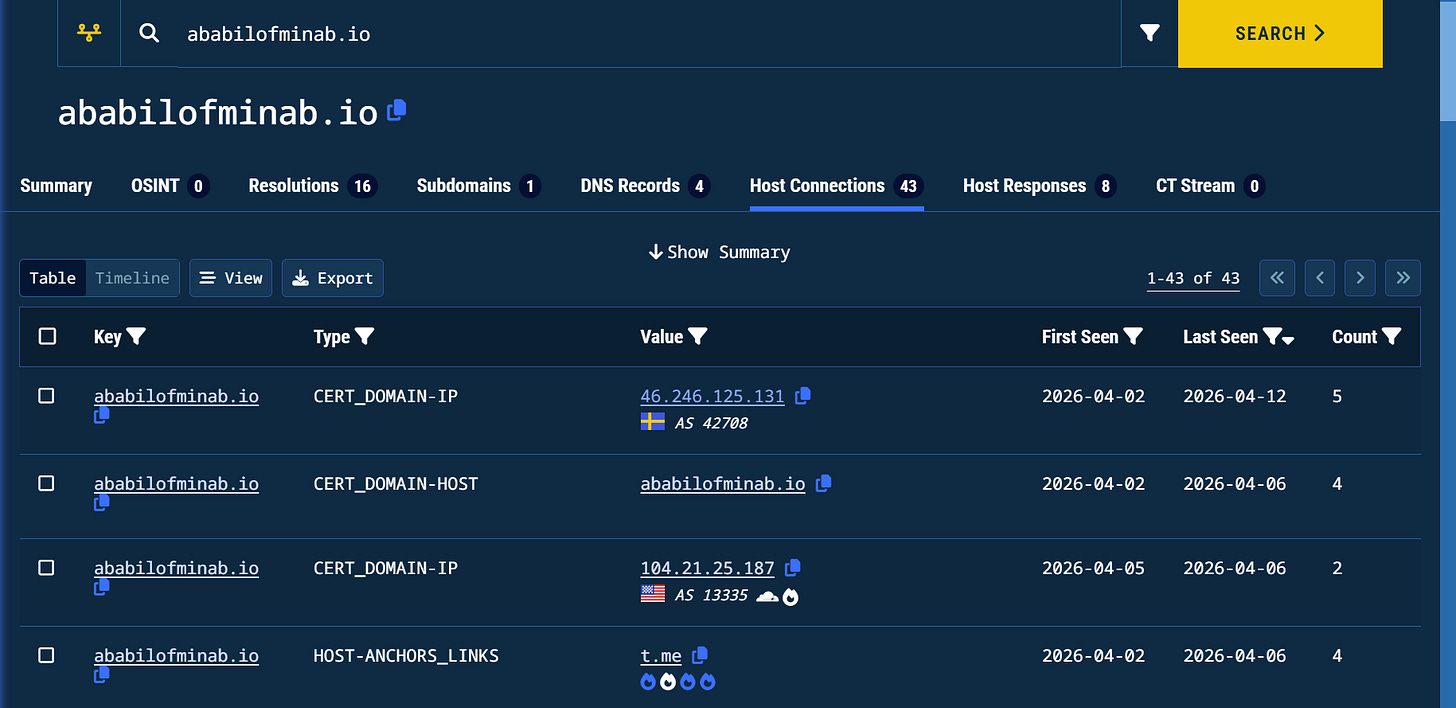
Jokes aside, their opsec isn’t perfect. They expose a TLS certificate for the host that points to the domain, which Validin picks up below, exposing the true host, despite it being behind Cloudflare.
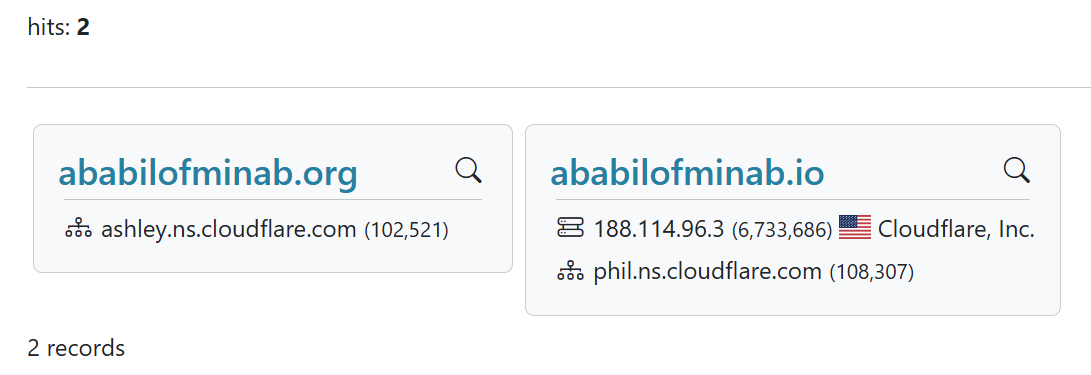
We also see two identical domains registered on different TLDs on Cloudflare - just like the IRGC espionage operation from last week.
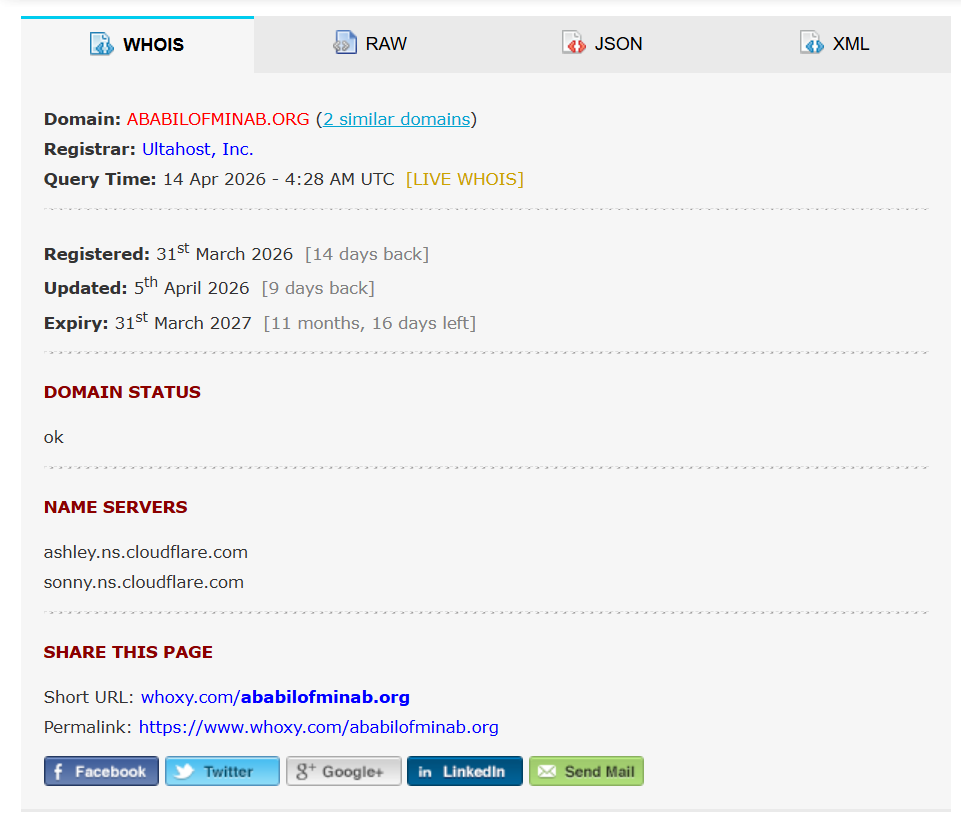
Despite being hosted on Cloudflare, the domain was registered on Ultahost - a registrar and hosting provider we’ve seen used by Iran multiple times in the past weeks:
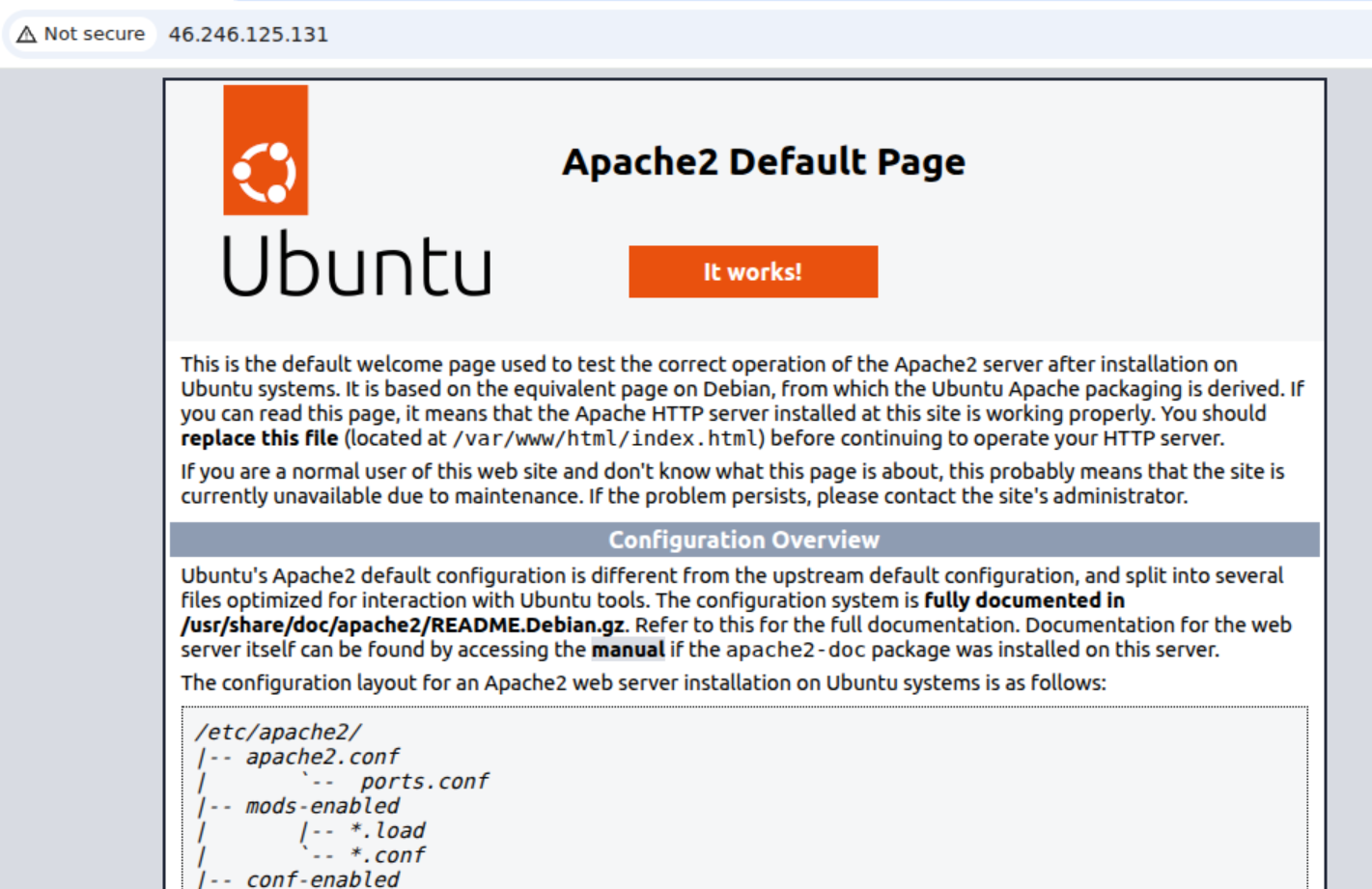
The host just exposes a default Apache (one of the most common web server) homepages.
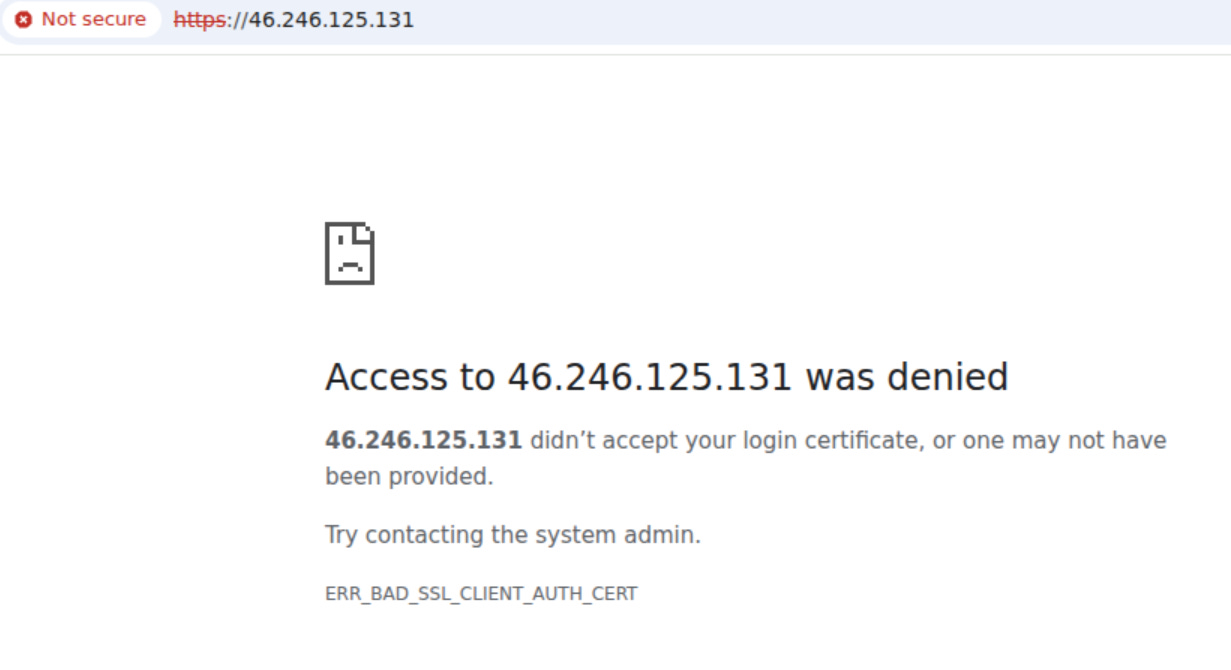
Trying to connect to the host on port 443 for HTTP (to see if the domain is hosted on the site still) gets a refusal as I lack a client certificate.
This means that they’ve locked down the ability to connect to the site hosted on the server directly, which is better operational security than we’re used to seeing, even though they messed up with the host TLS certificate.
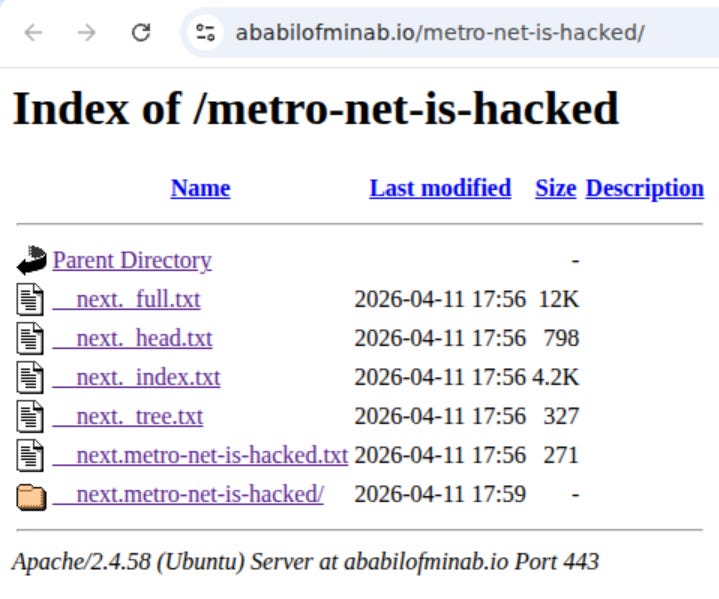
This is especially odd considering that some of their links lead to open directories?
The domain is otherwise uninteresting, no favicon results, interesting SOA or DNS records or otherwise.
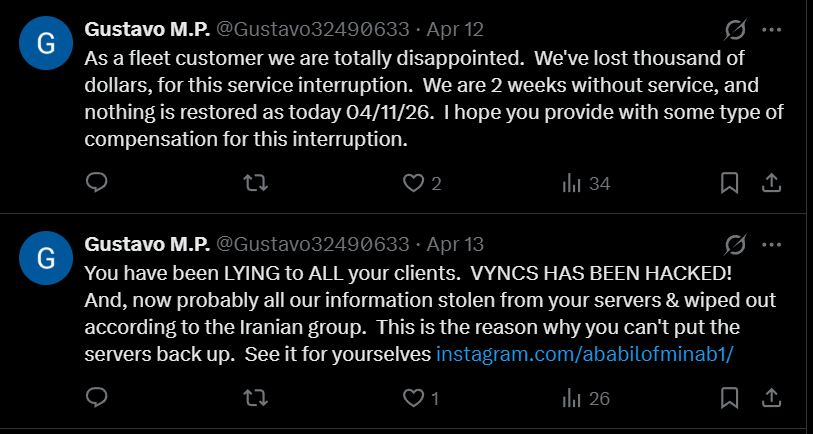
We also have some interesting post op activity. They operators seem to be running a burner, impersonating a customer responding to a tweet from Vyncs and referring to the domain:
This screams ASA to me, as it’s the type of thing they do and less for say cyberav3ngers/APT IRAN.
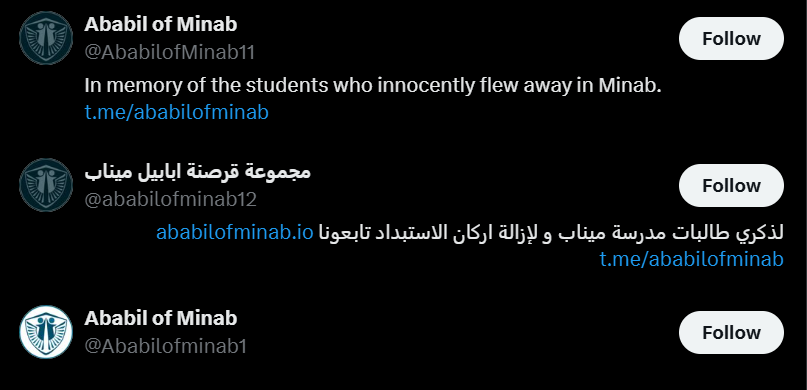
As stated earlier, they started off with a Telegram channel and Twitter account. The Telegram channel is already shadowbanned, and the Twitter account has been taken down.
Like past ASA operations, they do have backups ready to go on Twitter:
We also have an Arabic-language Twitter account which is still active. This is the type of thing that ASA does, they often run fronts in Arabic which we see less of from other groups:
This one is a fun one attribution-wise.
Actual intrusion into critical infrastructure. Leans more towards IRGC (Cyberav3ngers or ASA), though could be MOIS
Prepositioned backups ready to go on Twitter, something ASA has done, though other MOIS orgs have also (Handala in particular)
Use of Cloudflare - past IRGC operations, higher value
Islamic-language and aesthetics, similar to ASA
Running the operation partially in Arabic, points to ASA
Targeting US critical infrastructure, but seemingly for real (at least to some degree) similar to IRGC actors like APT Iran/CyberAv3ngers, ASA
Running additional entities beyond the main accounts - most commonly seen with ASA and IRGC actors but also done occasionally by MOIS actors
Registering two domains on Cloudflare simultaneously like last week’s IRGC spying operation. This means this is a higher-investment operation and I can’t recall many cases when the MOIS used Cloudflare, but I could be wrong.
Tighter OpSec than most MOIS operations
I’m inclined to believe that this is IRGC-related and not MOIS due to the above points.
The question there is, ASA or Cyberav3ngers/APT-Iran?
This one is a bit less clear, but if I absolutely had to guess, I’d lean towards ASA due to the specific TTPs - creating a new, higher-investment front with Islamic branding, but it could just as easily be cyberav3ngers or any other IRGC-related group (memery, timeline etc) or even the MOIS.
That’s it for this week, thanks for reading.