Maybe the real treasure was the IRGC partners we made along the way
Welcome to Memetic Warfare. While browsing Twitter I came across the below tweet.
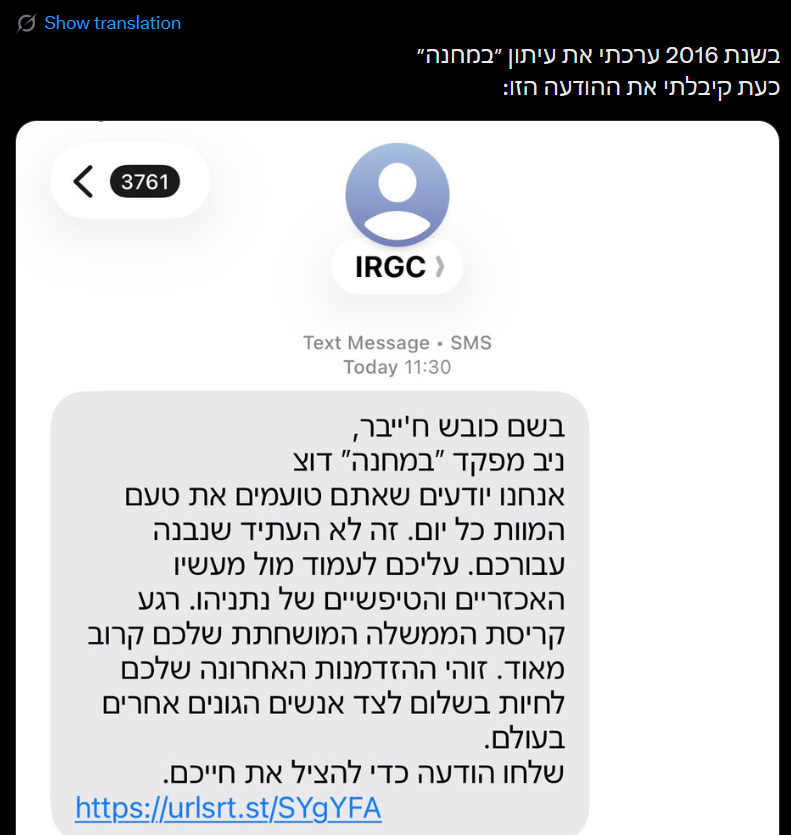
To summarize, the individual, who said they edited the Israeli military newspaper “BaMachane” in 2016, received a message from an SMS sender named “IRGC”. The message says, in stilted Hebrew:
“In the name of the conquer of Khaybar, Niv, the commander of “BaMachane” in “Dotz” [shortened name of Israeli Military Spokesperson’s office]. We know that you [plural] taste the taste of death every day. This isn’t the future built for you. You must stand against the brutal and stupid acts of Netanyahu. The moment of the collapse of your corrupt government is very close. This is your last opportunity to live in peace with other honest people in the world. To save your lives, send a message [url]”.
This caught my eye for a few reasons.
Firstly, most Iranian SMSes sent like this don’t include a link or personal information, whereas this message refers to the target by name and includes information on his past unit, indicating that the sender has at least that personal data on the individual.
Secondly, the information available is accurate, as confirmed by the guy who tweeted it.
Iranian operators could have this from multiple sources, including scraping social media for past unit affiliation, breached data for name and phone numbers or other, bigger data breaches (say, LinkedIn). Regardless, highly targeted SMSes.
So, let’s take a look at the link. The short URL resolves to the below domain:
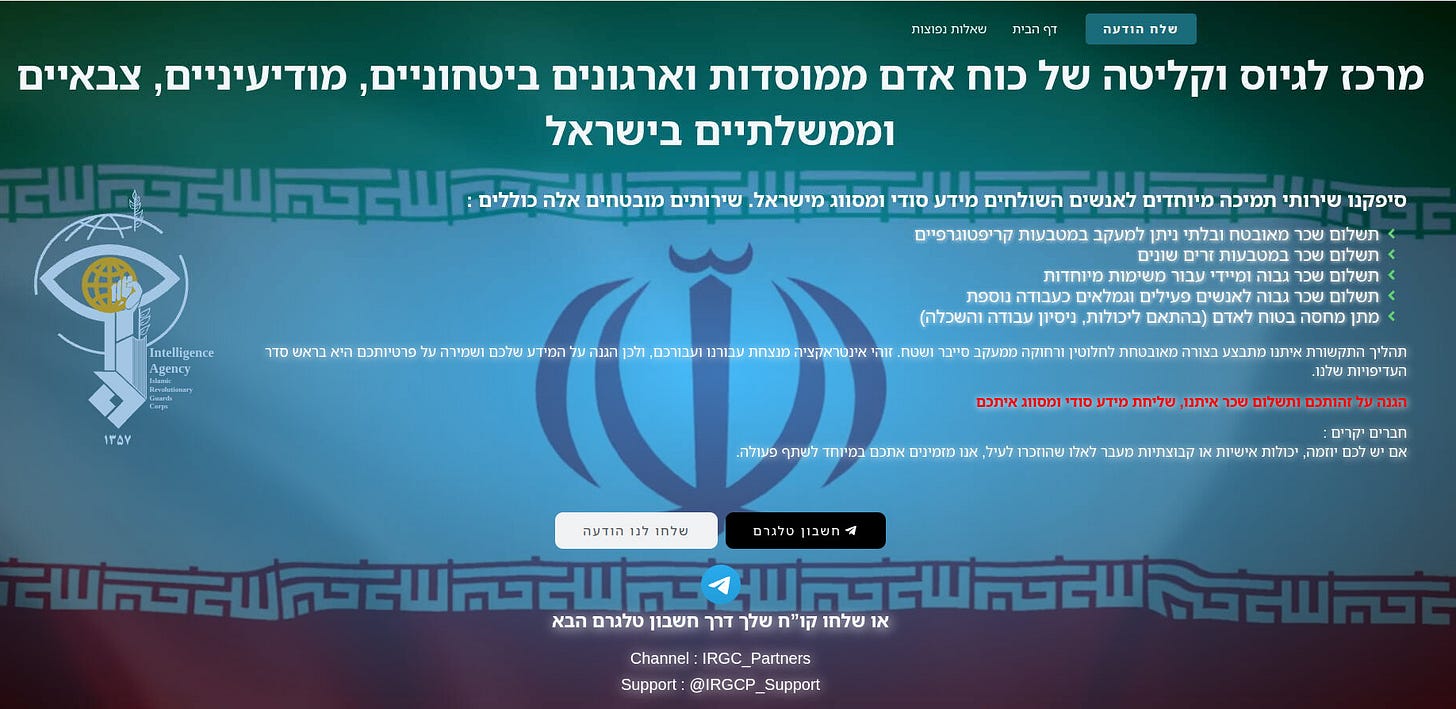
In short, the site is a “center for the recruitment and absorption [possible reference to similar phrasing in the Israeli “Bakum”, the base where all soldiers officially join the military] of personnel from various intelligence, defense, security, military and government organizations and institutions in Israel”.
Most notably, the site is overtly run by the IRGC. This is interesting as this is, to the best of my memory, the first IRGC-branded domain. Others have been organization-agnostic or tied to MOIS-related actors.
The site offers “special support services to people who send us secret and classified information from Israel”, including:
Payment of “secure and untrackable” salary via crypto
Payment via various foreign currencies
Payment of a high salary immediately for those who carry out “special operations”
Payment of a high salary those in active service and retirees as “an additional job”
Provision of asylum or shelter to those recruited
The site also states that all communication is handled in a “completely secure” fashion, “far from any cyber or field surveillance”, and that the “interaction” for them is their top priority in terms of safety and anonymity.
The site then invites those that have “initiative”, or special “personality or group” skills to contact them via Telegram or via the site directly. Funnily enough, they ask also for a resume via Telegram, and run a Telegram bot to make communication easier.
They were kind enough to include a FAQ:
They’re apparently gunning for leaders of “organized groups”:
Marxists would be happy to see that the IRGC doesn’t buy into the concept of unskilled labor, saying that “in our opinion no one lacks expertise, everyone has skills”:
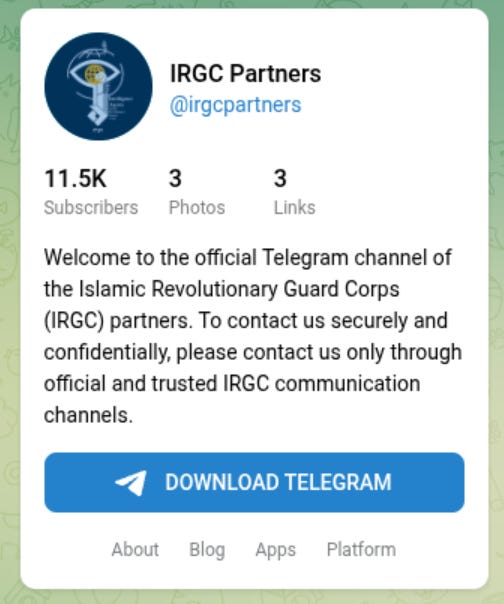
Let’s take a look at their entities. The Telegram channel was created on March 21st but only became active on April 2nd:
It already has 11,500+ subscribers, many of which I assume are fake to give it an air of legitimacy.
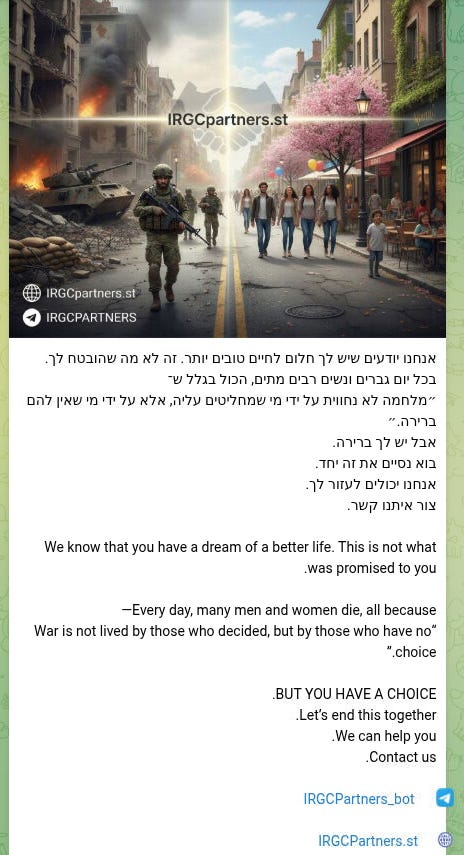
The posts themselves are obviously very much AI-generated and posted in English and Hebrew:
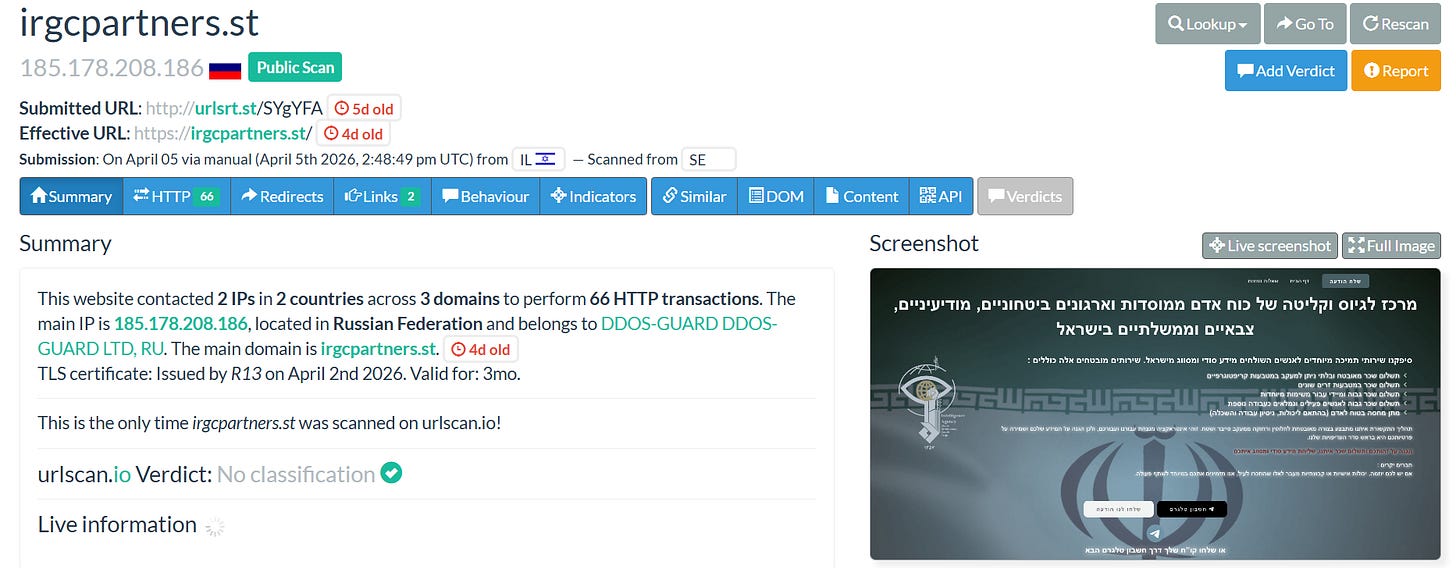
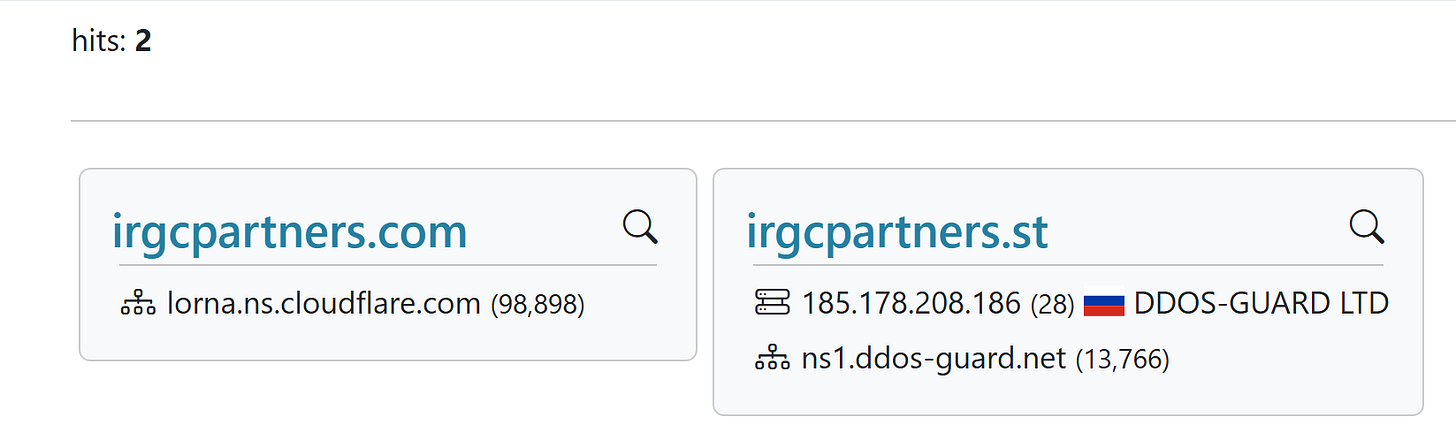
The domain infra isn’t super interesting.
They’re using the Russian DDoSGuard service, as Handala and other Iranian groups have many times in the past.
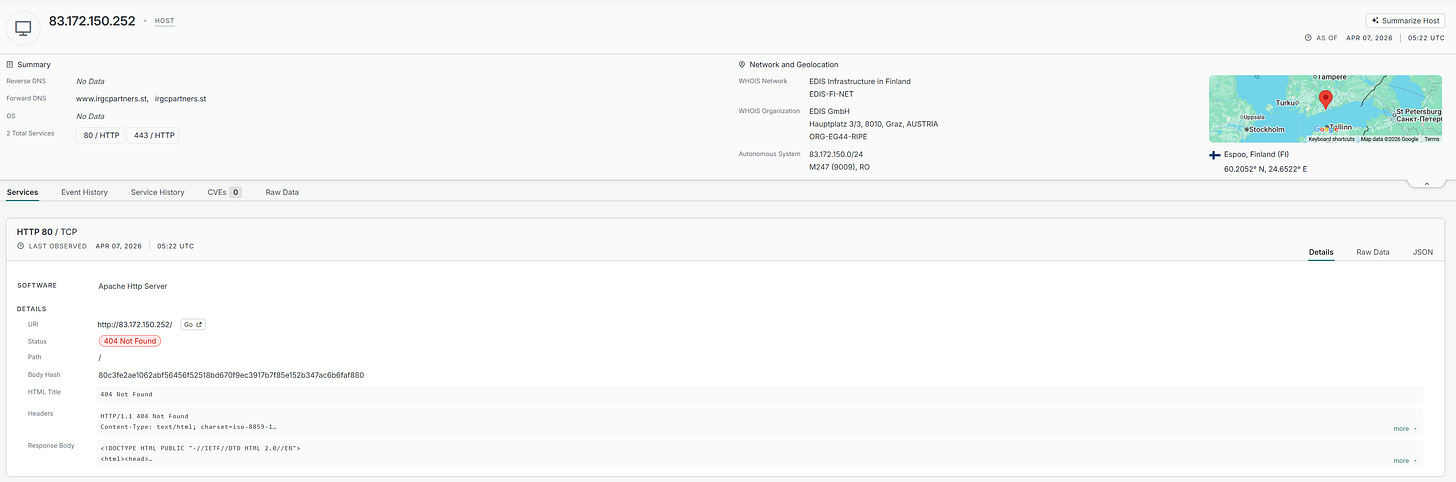
They have one past host on M247, which Iranian IRGC and MOIS actors have used many times in the past, but not much of interest is available there now. It’s now off of the M247 host, which only had HTTP/S ports open anyway, and fully on DDoSGuard.
Doing a quick search for similarly named domains finds one .com domain which previously was on CloudFlare, but was taken down presumably quickly.
Back to the domain itself. In contrast to past recruitment operations, which went as wide as possible in terms of targeting and had a strong IO component to them, this operation is focused and stealthy, comparatively at least.
This campaign clearly targets exclusively military/government personnel, which makes sense based on the person who first flagged it and the probable sourcing they’re using, not people off of the street.
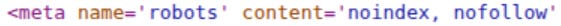
We can also see this focus reflected in the source code for the domain. The robots.txt file is set as “noindex, nofollow” to prevent all indexing by search engines. They don’t want it to be found or exposed too early, but rather just seen by those sent links.
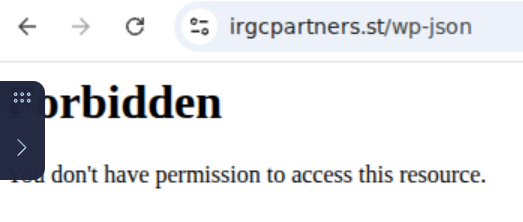
They’ve tightened up the exposed WordPress endpoints that are so often left exposed:
They’ve even obfuscated the admin login panel, though not in a way that would impact anyone really interested in popping the site from finding it:
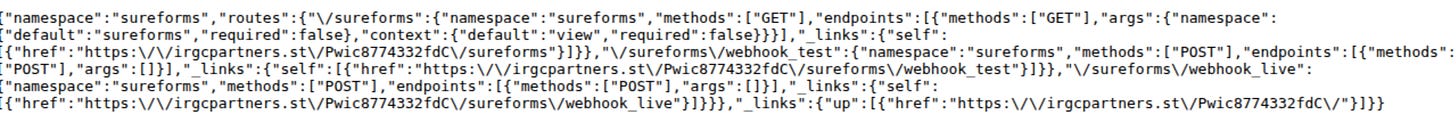
By diving into the source code we can find the line where they call WordPress APIs and the obfuscated URL to find it:
They’re using the forms tool SureForms to receive incoming messages with a webhook integration:
Overall, a very interesting development here. To summarize, we have an IRGC espionage recruitment operation specifically targeting military/government personnel, and presumably using breached data and/or other open source data to target people individually.
In contrast to MOIS or other recruitment operations, this operation tries to keep a low profile and has minimal to no IO components to it. The operation is also less exposed than other MOIS operations, which casually throw OpSec to the wind.
Quite interesting IMO and definitely a space to keep watching.
That’s it for this week, thanks for reading.