Memetic Warfare Reading Corner
Welcome to Memetic Warfare.
I haven’t had the personal time to dedicate to a truly killer post like you’re all used to by now due to the ongoing regional war, and for that, you have my sincerest apologies. We should be back to normal soon hopefully.
I rarely do this, but this week I have no choice. Instead of a short, somewhat timely, often practical and most importantly, edgy, blog post, you’ll get a curated reading list of multiple things that I personally have on my to-read list in their entirety which I am now dubbing the Memetic Warfare Reading Corner.
The first is a report from Georgetown’s CSET from a month or two ago on Chinese military use of AI and their “wishlist”, available here.
While interesting, this isn’t the type of thing we’d normally discuss at Memetic Warfare, but there are a few cool things about it.
The first is that it relies heavily on RFP (request for proposal) documents - thousands of them - publicly available in China. These are the few types of public documents one can actually work with in China (alongside some customs documents) as well as patents, tenders and so on. Other corporate data is often unavailable via most methods, if at all, to obscure ownership.
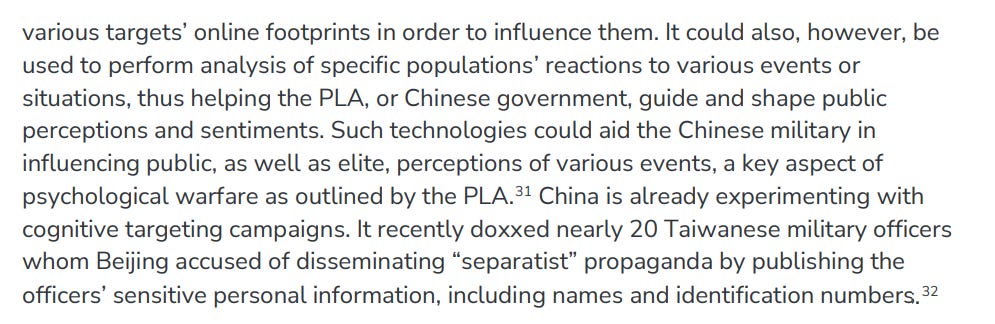
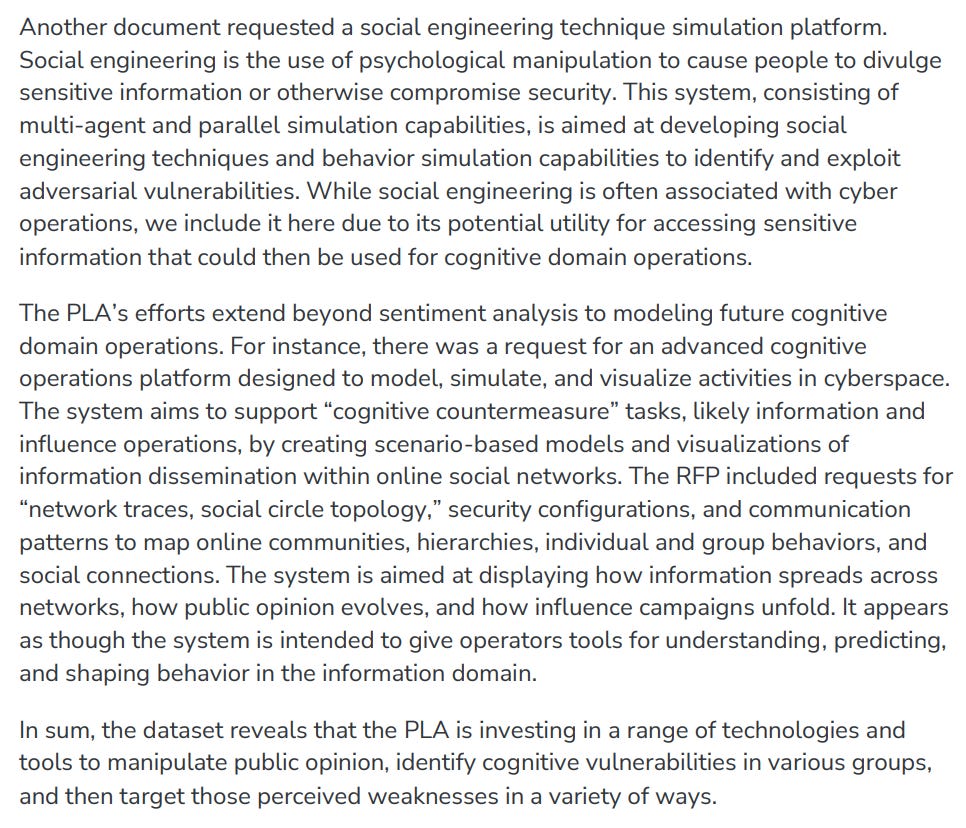
There also is a short “cognitive warfare” section, focusing on requests for t hings like “deepfake” systems, which I find to be a bit overplayed. The request for a library is an interesting one:
Detection also came up:
They also had requests for broader, “LLM-powered” intelligence platforms for cognitive targeting:
Lastly, we get some information on social engineering:
Overall, a super interesting paper with a lot of utility, one of the better usecases for OSINT available.
The next Memetic Warfare Reading Corner recommendation is an academic article from Antonia-Laura Pup on the Romanian elections, foreign interference and the role of intelligence agencies:
Check out the abstract here. This one is more for those interested in policy and governance and so on, but still interesting IMO to see academic treatment of IO and intelligence in a specific event, especially one so recent.
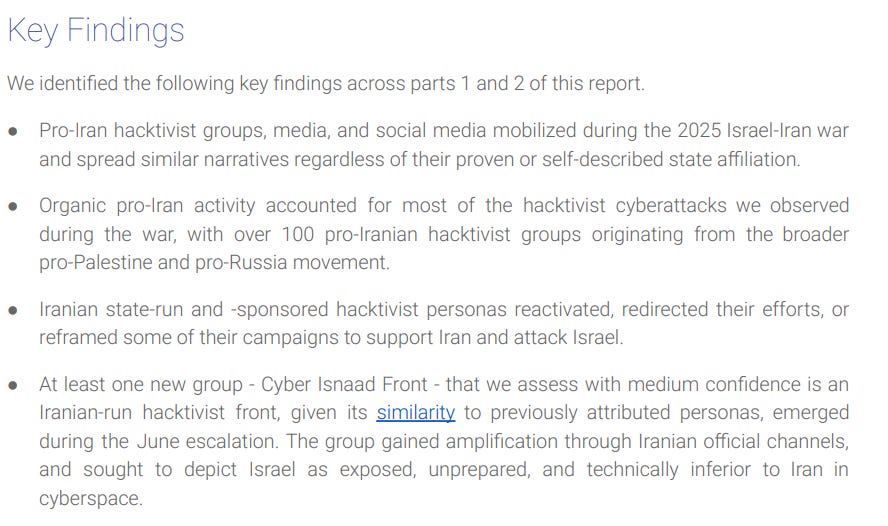
The next piece we’ll look at is Graphika’s latest look at Iranian hacktivist fronts, a topic near and dear to my heart, available here. This is a follow up to their previous report on the topic, link available in the report. Key findings below:
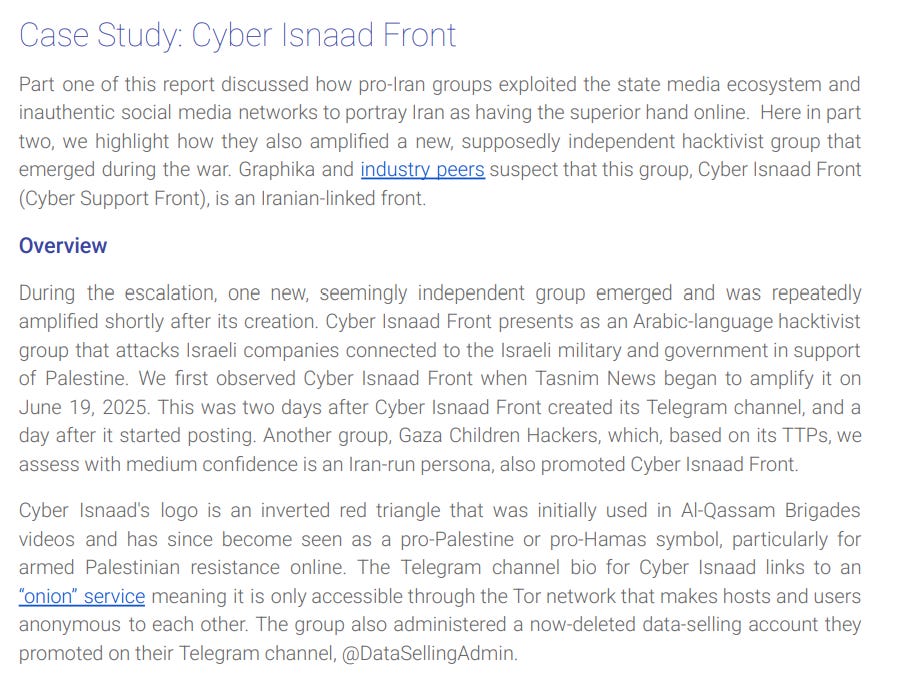
There’s a lot of great stuff so give it a read if you’re interested in the space, but we’ll skip right to the Cyber Isnaad Front section:
If you were wondering, the “industry peer” is an article quoting the FDD and Memetic Warfare on this, though we disagree on attribution - I’d use higher confidence.
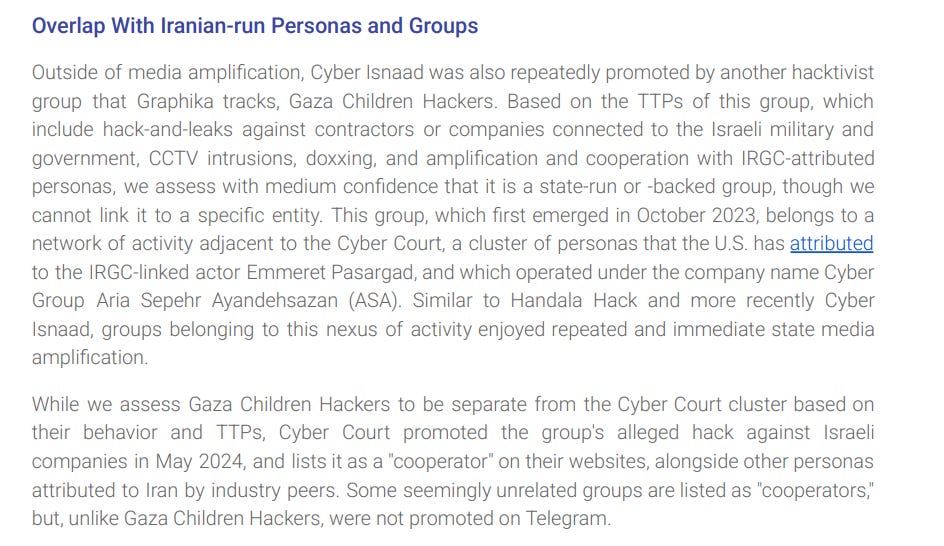
One of the great things about the report is the focus we get on lesser-discussed groups, such as Gaza Children Hackers:
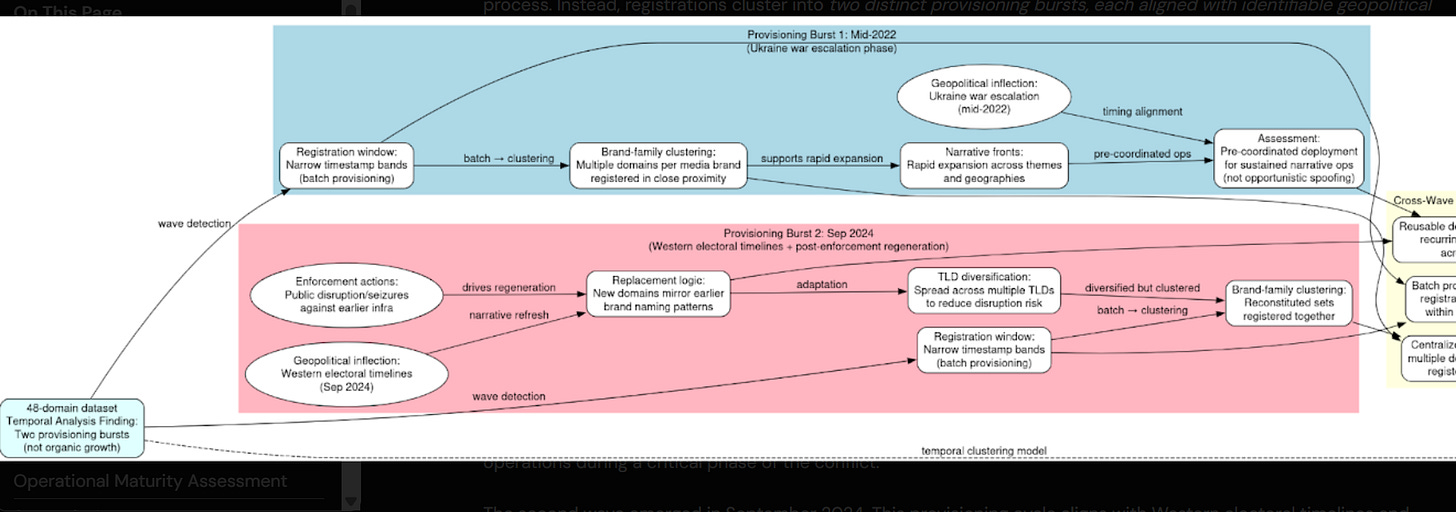
We’ll conclude with one report from a great team to follow, Domaintools Threat Intelligence, available here on RRN/Doppelganger.
I’ll share the summary and breakdown below, focusing of course heavily on domain registration:
It’s very cool to see Domaintools really dive in to what they’re best at: domains.
Check it out, it’s fascinating and super high quality. Great stuff.
That’s it for this week, thanks for reading.