Down To Investigate
Welcome to Memetic Warfare.
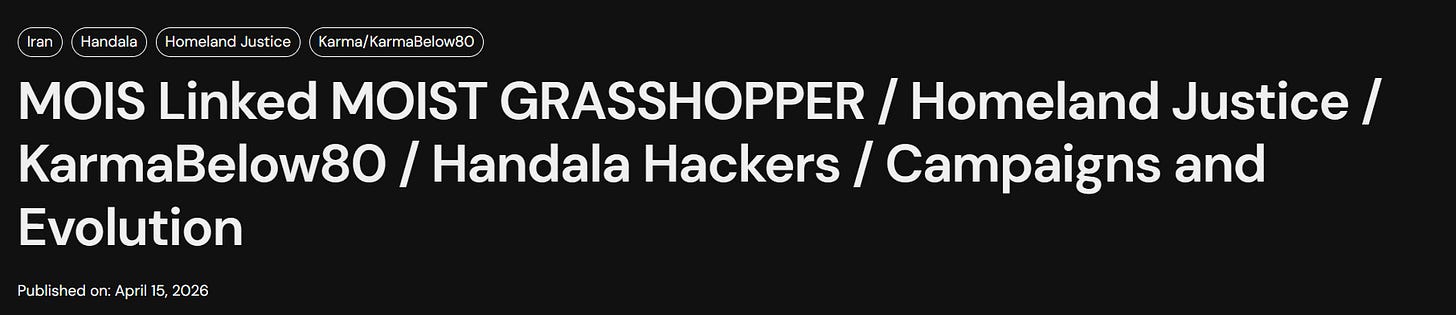
We’ll start off with a fantastic report from Domaintools Investigations on MOIS cyber and IO operations, with one of the better threat actor names - Moist Grasshopper.
Domaintools Investigations (DTI) consistently puts out some of the best reporting out there. If you’re a reader of Memetic Warfare, you should be a reader of their stuff.
I’d also like to shoutout Domaintools separately from this as well. When I first got started in investigations, I learned a ton from Domaintools’ blog, which would publish detailed investigations and guides. Much of it was an inspiration for what I try to do here.
Back to the report - see below:
The report is way too long for me to cover here and do it justice, but it hits every main point. It gets the structure of the MOIS and their threat actors, and more importantly lays out how they think and work very articulately. Check it out.
From here, we’ll cover more Iran.
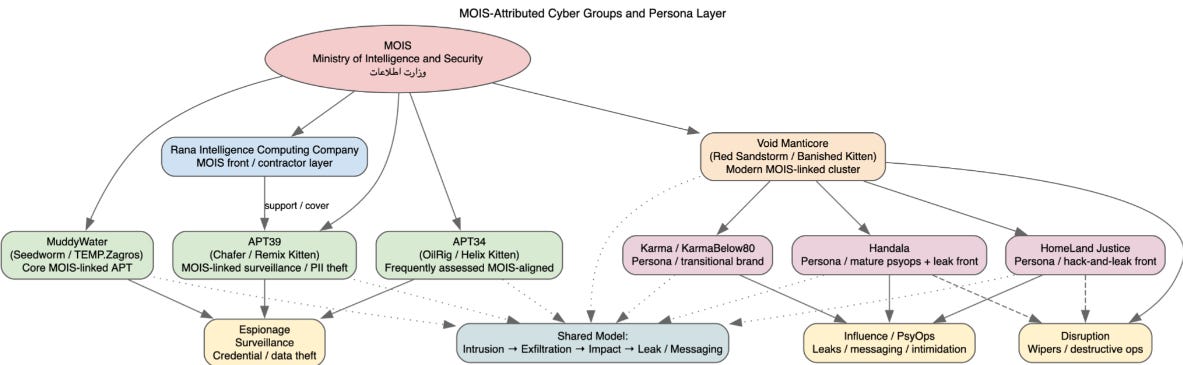
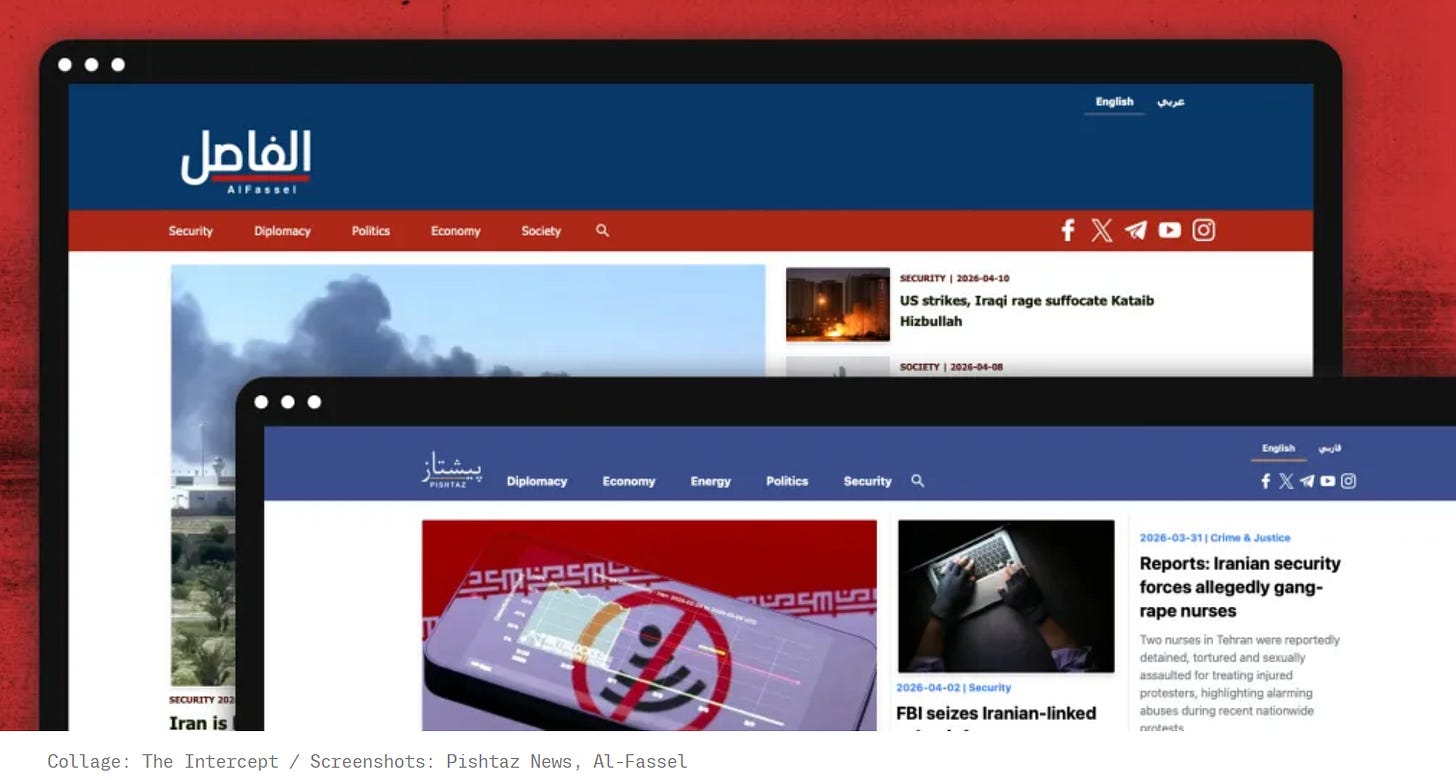
I’m not one to usually link to content from the Intercept, but they do occasionally leave me no choice. One of their reporters exposed two covert CENTCOM news domains targeting Iran and Iraq, Pishtaz News and al-Fassel:
The two domains of course promote pro-US and anti-regime narratives, but like previous CENTCOM/contractor IO, they exhibit basic operational security mistakes, like having the sole account they follow be CENTCOM:
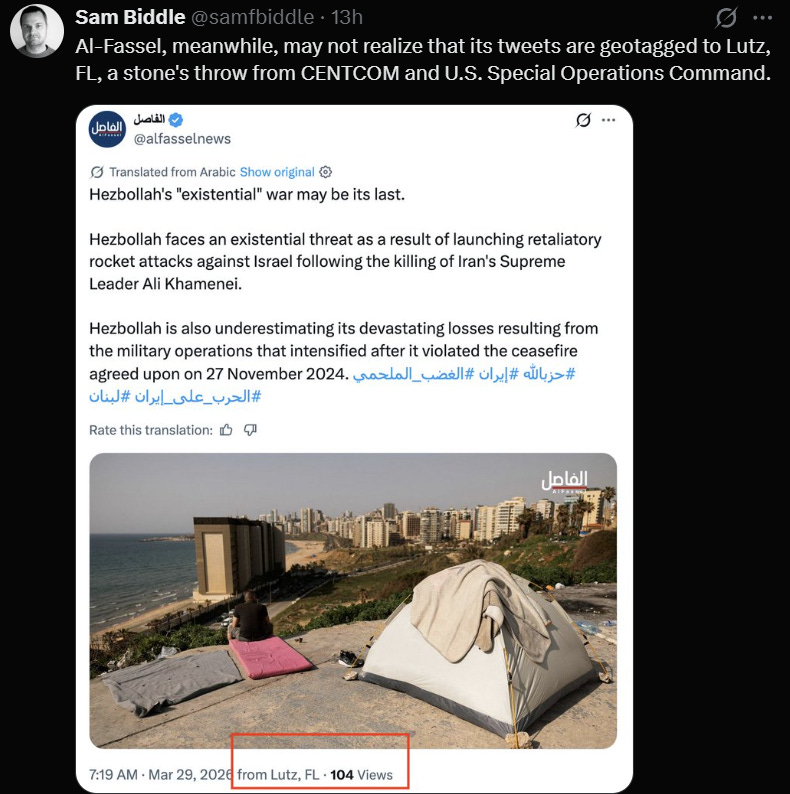
Or, even worse, not using a proxy or VPN:
Or, in perhaps the most egregious error yet, hosting a CENTCOM emblem on their domain for some reason:
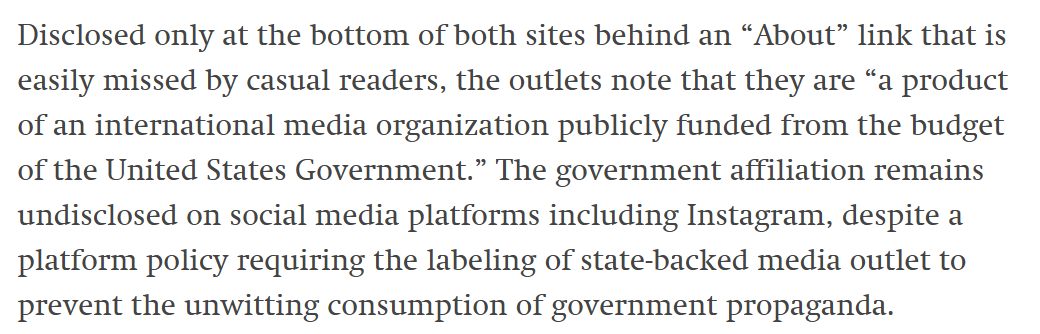
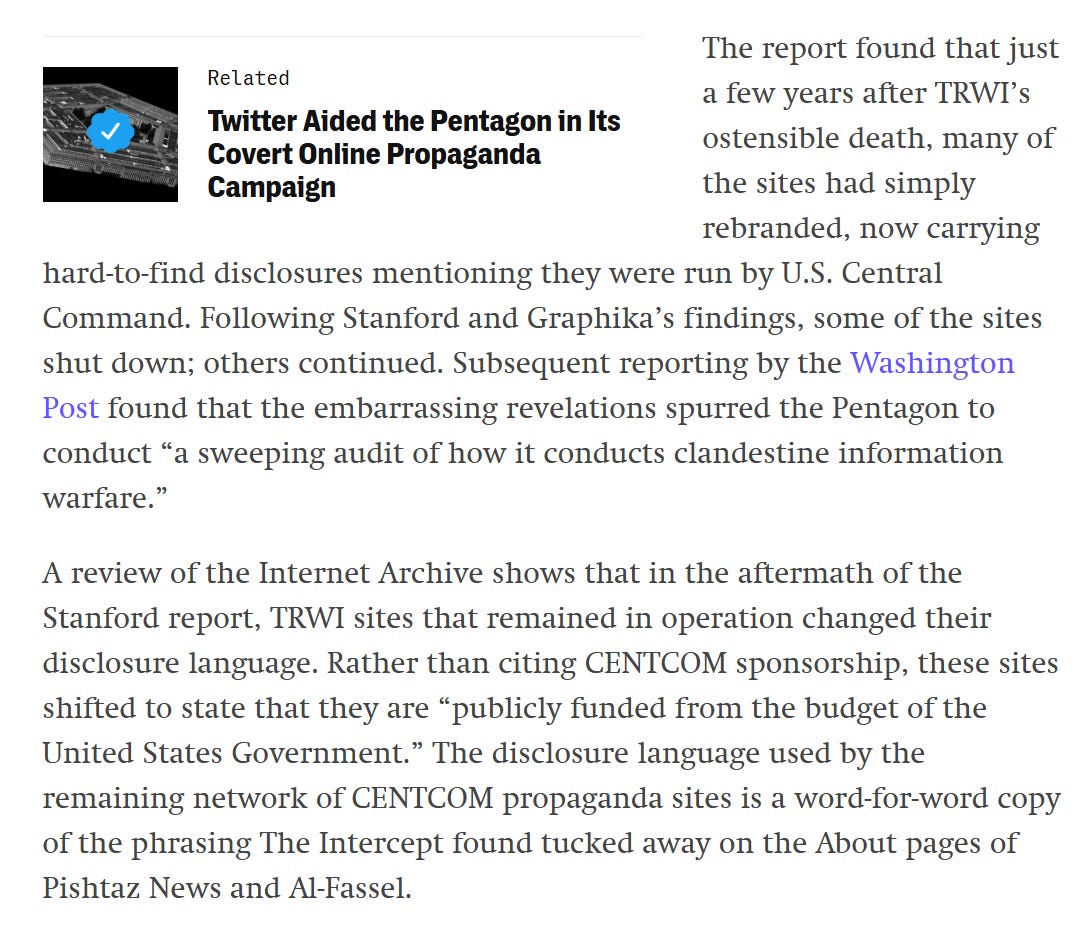
Weirdly enough, these domains - like previously exposed CENTCOM domains in “Unheard Voices” provide some type of odd disclaimer on the domain itself, which they don’t have on their social media accounts. I honestly can’t think of why CENTCOM feels the need to do this? I can’t imagine the type of regulation requiring them to somehow disclose this.
This is described later in depth, with CENTCOM having changed its disclosures. Time to just drop it guys!
The article notes that the YouTube channel has some overtly AI-generated content:
Despite the effort, the domains’ accounts have essentially no traction:
Moving on, we’ll stay on Iran and take a look at the latest joint US government advisory on Iranian actors targeting critical infrastructure in the US, available here.
They don’t attribute it to Shahid Kaveh/cyb3rav3ngers or the IRGC but do mention how funnily enough that same group was doing the same thing back in the before times of 2023, and we also learn that they apparently hit 75 different devices, an interesting update showing the scale of the activity:
We also see that some of the activity hit government services, water and energy stations and so on, with some experiencing “operational disruption and financial loss”. We also probably had some defacement based on the first paragraph.
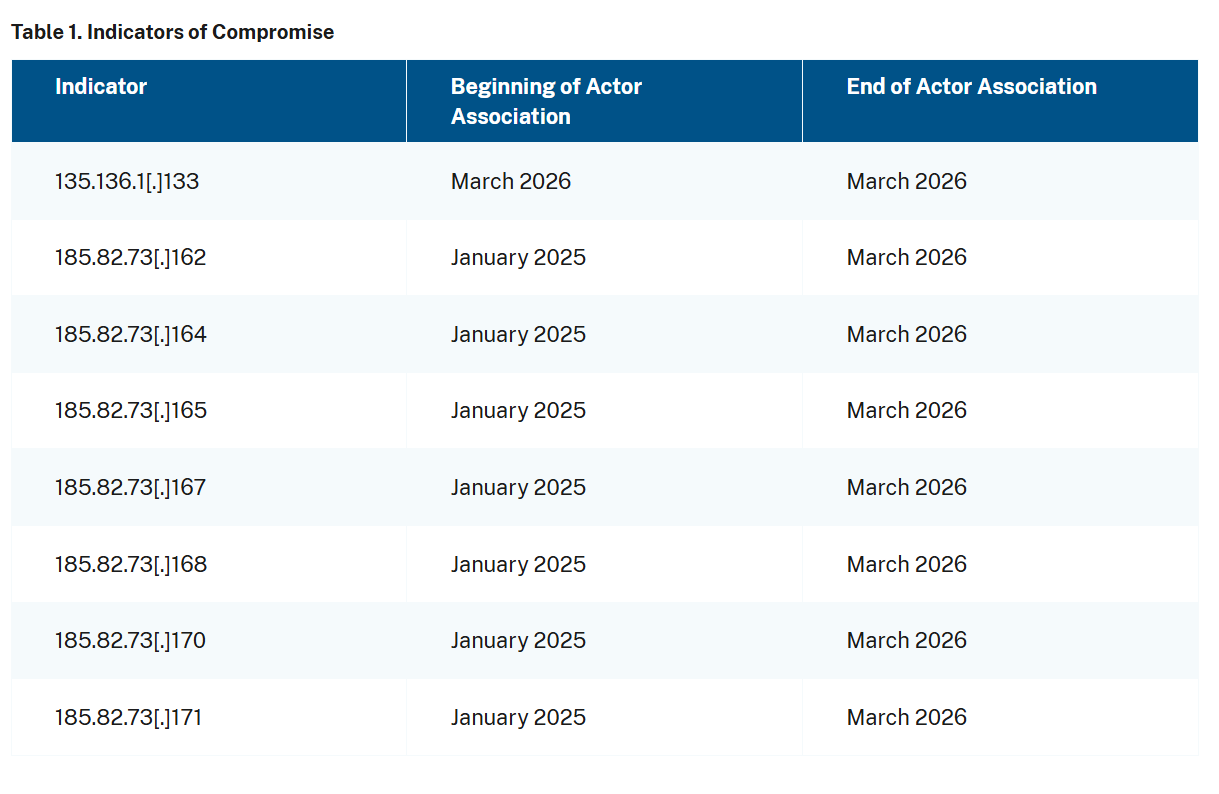
The IoC section is more interesting:
What’s interesting about the IP range is it occurs mainly via one AS, and specifically in one CIDR range even. It’s always useful to check sequential IPs, as shown here.
Most of the IP addresses are run by Ultahost, with the one beginning with 135 belonging to M247, a hosting service that we’ve seen exploited by Iran many, many times.
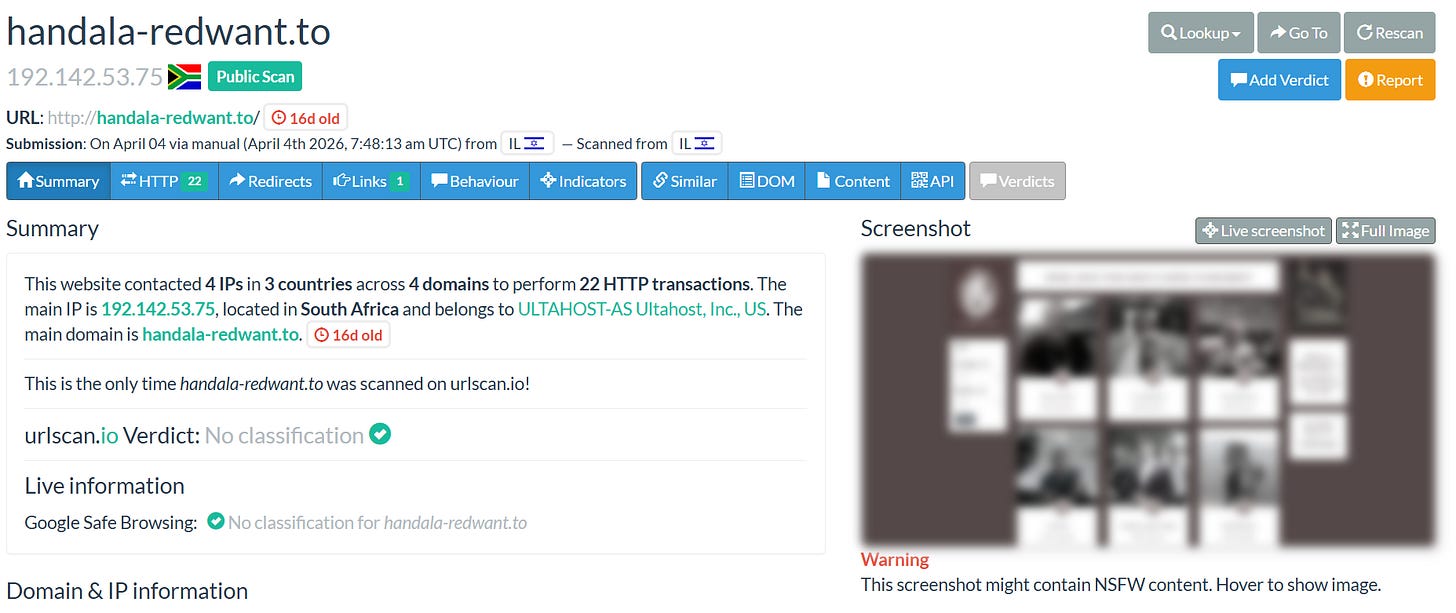
Ultahost has also has been exploited in the past for cyber and influence operations, ranging from Doppelganger to MOIS fronts such as Handala.
Just goes to show you the importance of monitoring problematic ASes.
That’s enough Iran for this week, thanks for reading.