Do I look like I know what a PDF is?
Welcome to Memetic Warfare.
It’s a bit of a quiet week, so we’ll just cover a few topics in brief.
We’ll start off with one super-prominent topic: MAPP.
I’m not one to comment here on things covered well in mainstream media for the most part, but I will make an exception this week. Microsoft announced that it is, to use a technical political term, giving the stanky boot to two Chinese firms in its threat intelligence sharing group MAPP.
This has been covered to death (appropriately so) in mainstream media, Natto Thoughts and by multitudes of people much smarter than I am. I will, however, bring up one thing not often discussed: possible Chinese IO targeting Microsoft yet again after this.
Microsoft has been targeted by China for repercussions for its activity in the past on multiple occasions, including the Volt Typhoon reports that we’ve covered here. Shortly after this thing broke, as we’ve also discussed here, the Global Times put out an article accusing the US of in fact doing a highly similar thing:
Point being, this story may not be over. Is it possible that we’ll see Global Times articles or a full blown anti-Microsoft campaign? Quite possibly.
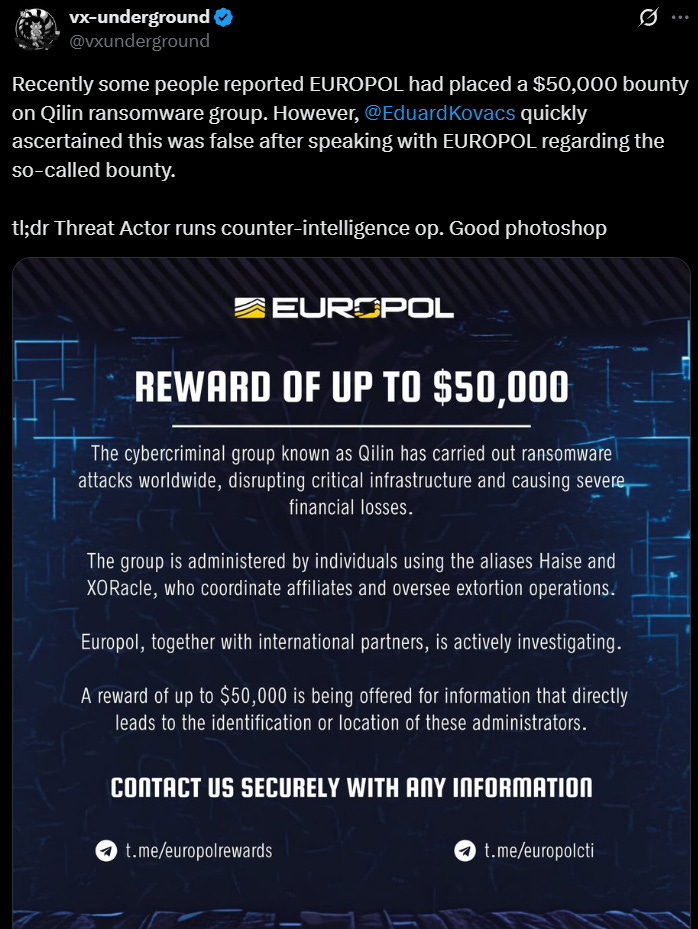
VX Underground (a great account to follow in general), posted something worth noticing. Apparently, or so it seems, Qilin, a ransomware group, put out a fake Europol bounty for reward poster.
Despite some obviously fake things here, such as the use of a dollar sign instead of a Euro sign as well as some awkward phrasing and the use of Telegram as the main reward channel, this is still a very interesting and arguably initially convincing case.
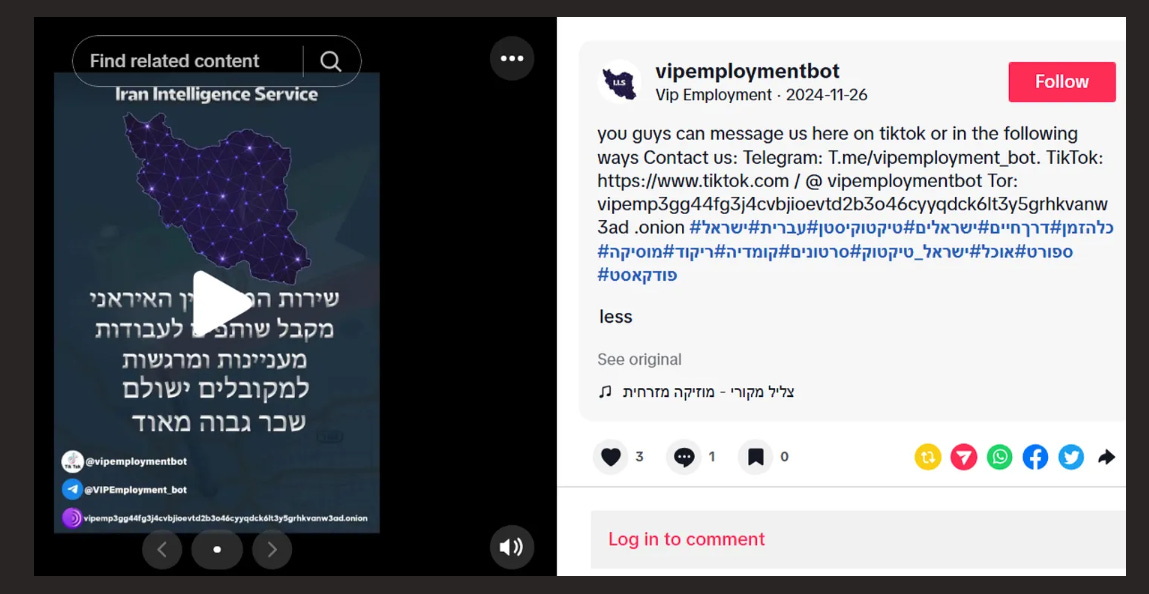
Is Qilin or whoever ran this just trolling, or were they actually trying to run a counterintelligence operation to figure out what others may know about them? Regardless, it’s worth noticing. The impact for IO purposes is also noteworthy, as recruitment and even counter-intelligence operations can be run as IO or as complimentary to IO as seen by Iran:
On another note, a new hacktivist group has popped up, calling itself both the Cyber al-Quds team in English and Arabic, while also branding itself in a video as “Lashkar al-Tharallah” of the al-Hosseini resistance.
Firstly, this naming is super derivative, come on guys. Give me something interesting! They're not really trying here to hide ties to Iran, with the name itself using Persian words such as Lashkar despite also naming their group in Arabic.
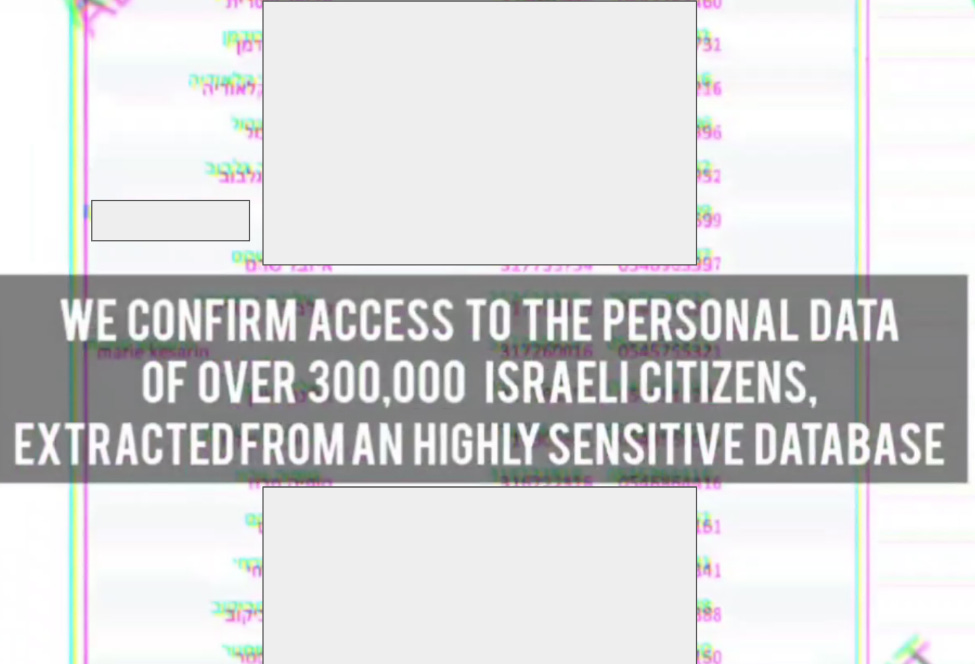
They’ve only been active a few days, and have put out two PDFs from an alleged compromise of some larger Israeli database. What’s more interesting is the minute-long video they put out, which is the kind of thing that ASA often does, but they usually do a better job than this so who knows.
The “leaks” themselves are unsubstantiated and super boring, but are put out as provenance of the alleged hack. The data is clearly not raw, with weird phrasing and structure - see the video to see an overlay of their text over it:
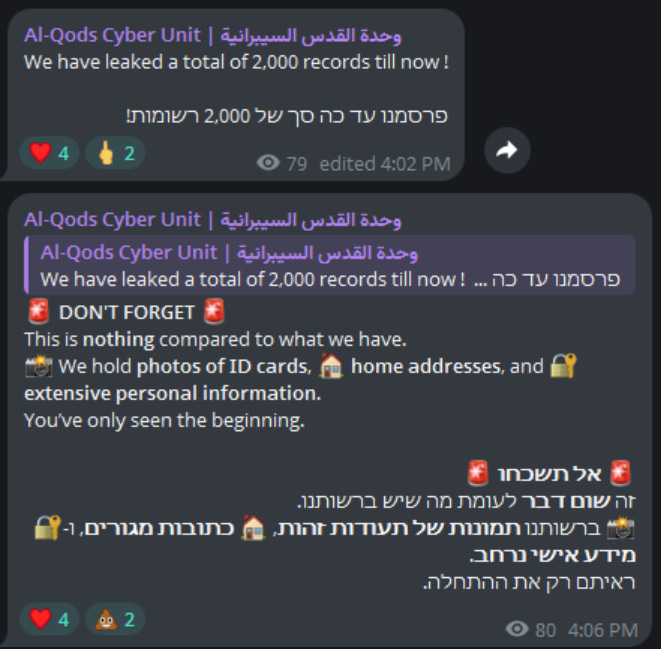
Despite the data leaked being unironically smol, they are super proud of it:
They don’t have any other online entities yet but were shared by some pro-Iran assets, so that’s always suspicious. Let’s keep an eye on them and see what comes up.
That’s it for this week! Leave any jokes, complaints or comments in the comment section.