You're recruiting me at a very Chinese time in my life
Yet Another Suspected Chinese Virtual Espionage Operation
Welcome to Memetic Warfare. This week, we’ll be taking a look at a new, suspected Chinese espionage operation going beyond typical targets of similar operations.
This week’s post is sponsored by Falkor AI. Falkor is an AI-driven investigation hub with a ton of external data integrations, analytics features and more. Check them out at falkor.ai.
We’ll begin with a quick look at the New York Times’ coverage of a Chinese espionage operation targeting the House China Committee.
The article has a lot of interesting points to it, and you should read it. The operation used the guise of Nimbus Hub Consulting, a domain first exposed here on Memetic Warfare:
Nimbus Hub is but one of dozens of domains exposed, so if you’re interested, check out the post above for additional context on the scope of that Chinese operation not covered in the article.
And now for something very similar.
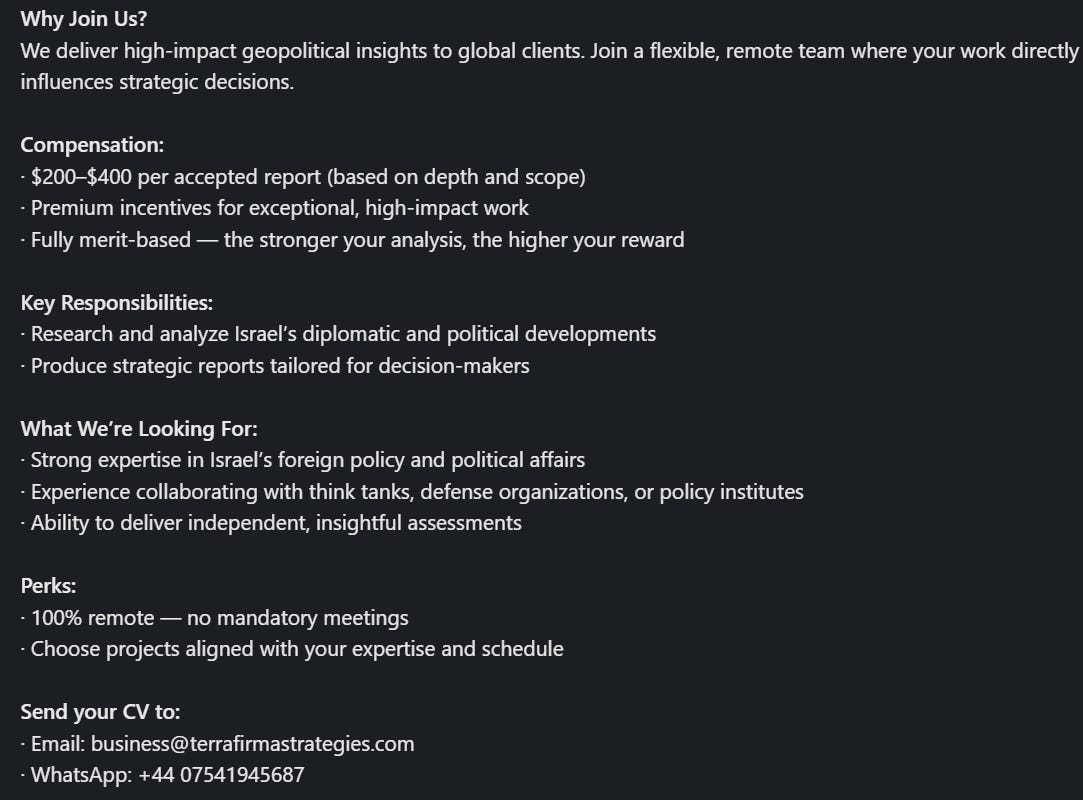
This week’s investigation began with me receiving a job posting sent to me by a friend of the blog. The posting, looking for an awkwardly-phrased “Diplomacy Researcher”, focuses on Israel.
The post offers payment per report on geopolitical affairs, looking for people with experience in Israeli foreign policy and with ties to defense and policy organizations. The contact information includes a UK phone number and a domain, Terra Firma Strategies.
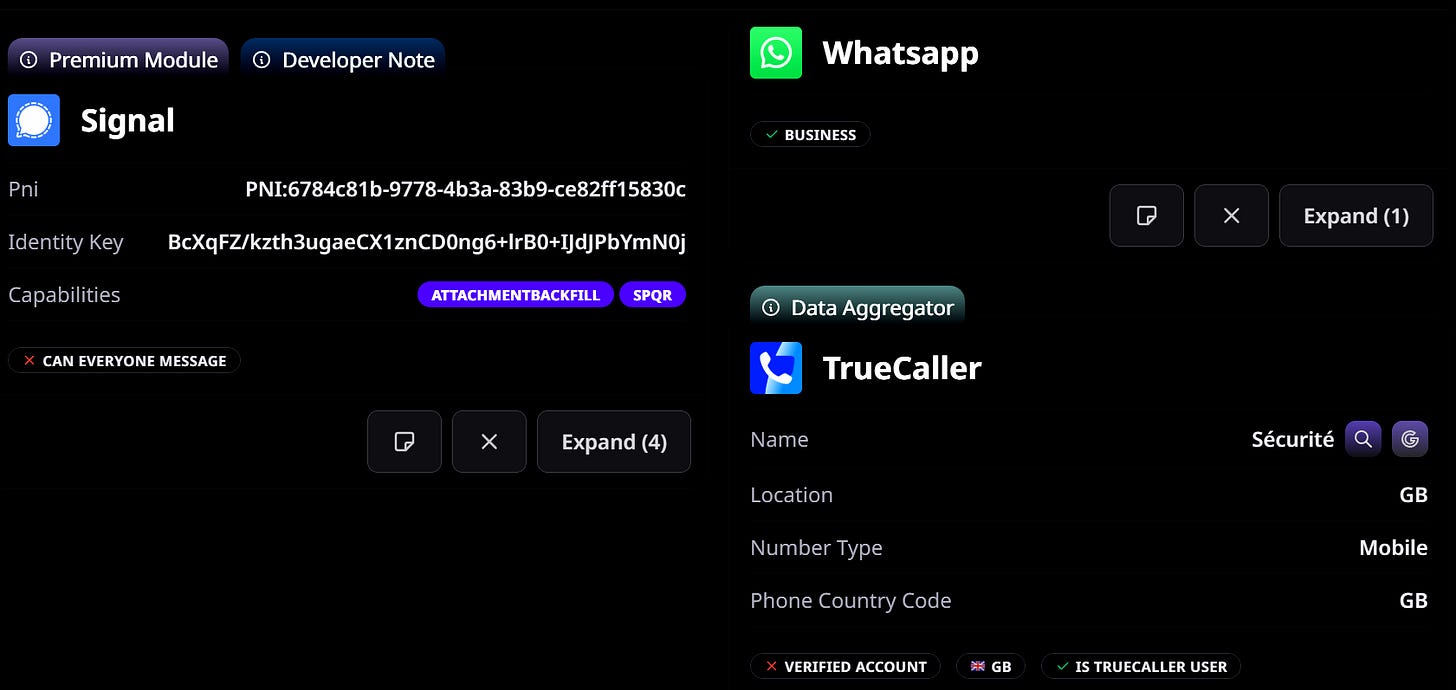
The number itself only has a Signal and WhatsApp account tied to it. Signal is an interesting choice for a company, and the TrueCaller listing is listed as “Securite”, in French, meaning, of course, security in English.
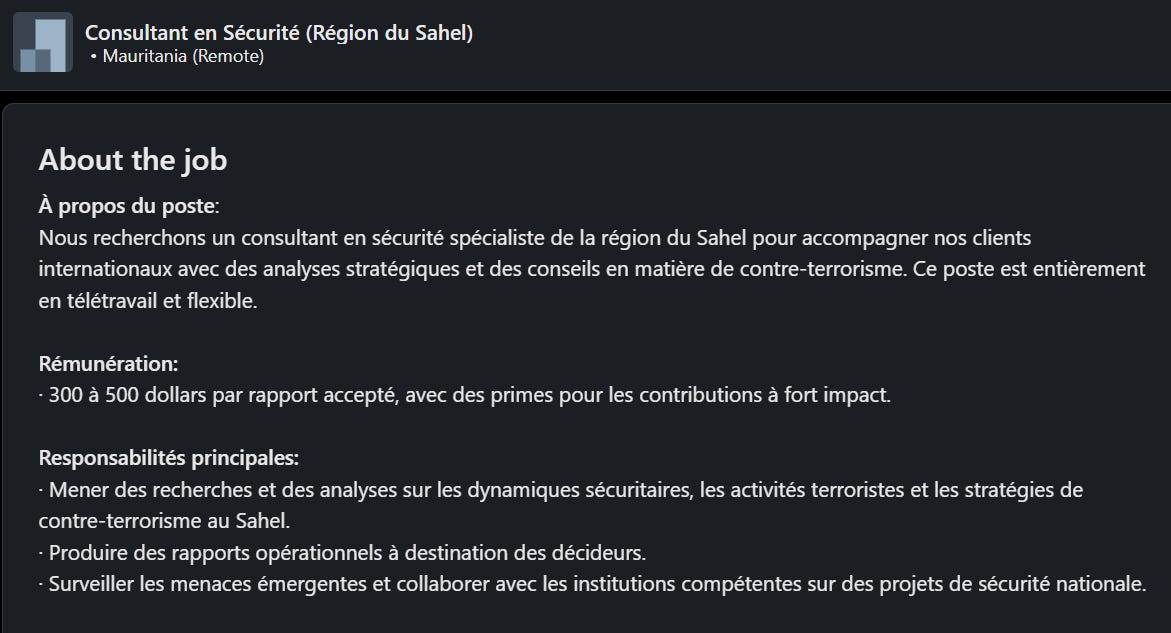
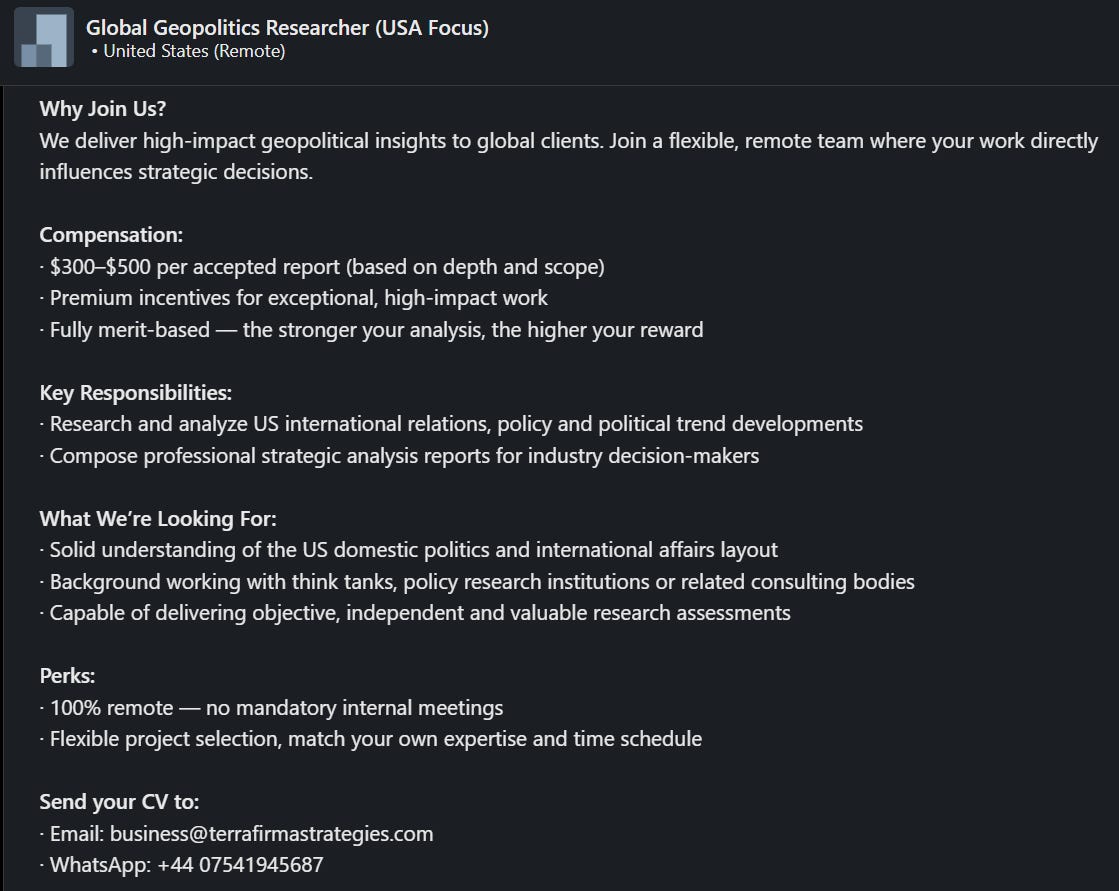
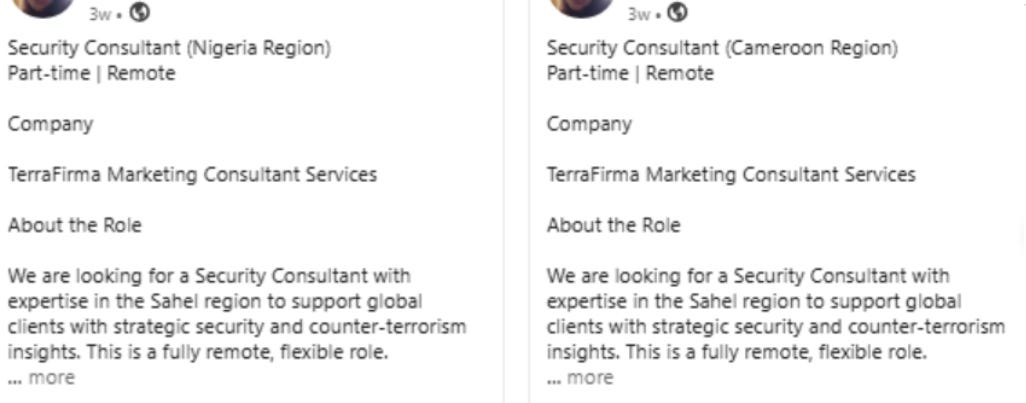
Just by searching the number, email or domain we can find other listings, including the Sahel region, Syria, India and the US, all opened in the past few weeks. They’ve been busy worldwide it seems!
Let’s now check out the domain. They put out geopolitical content, though not a lot of it:
They offer multiple services, but the most relevant is “geopolitical and policy intelligence”:
The about section is sparse, claiming that they were founded in 2025 in the Philippines, but with no information as to personnel.
The site itself has a different number listed on its site and an additional email, with nothing tied to them.:
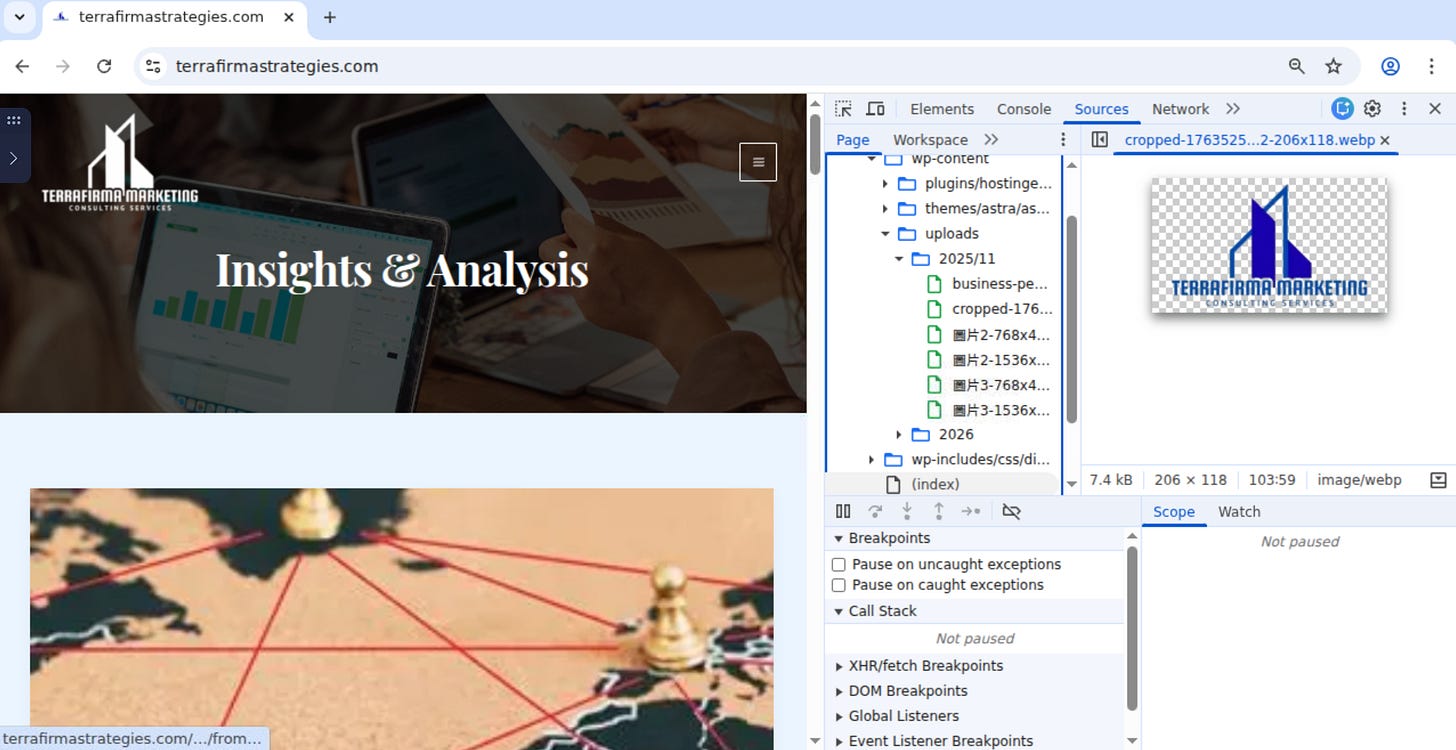
While ostensibly Phillipines-based, the domain itself has indicators tying it to China. The first is the use of Chinese filenames on uploaded images:
The domain, which runs WordPress, also has a Chinese language pack installed.
Not doing a great job of hiding it here:
Comments should be left in Chinese:
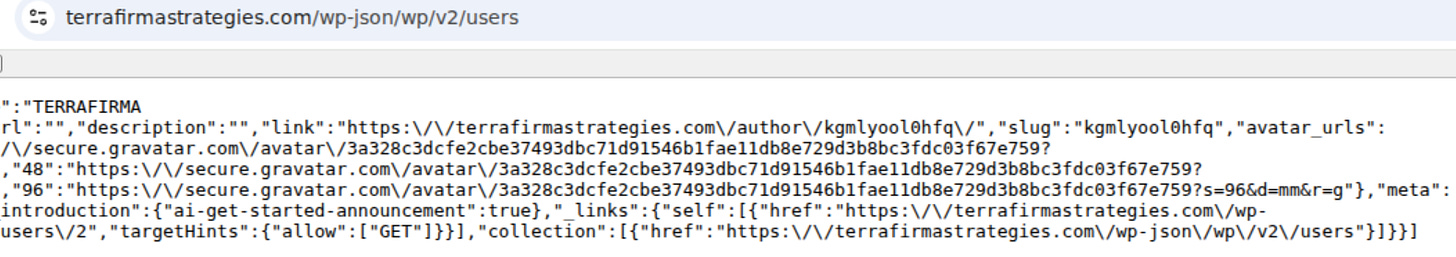
They didn’t shut down the WordPress APIs on the domain also, so we can see that the user account is a burner username:
The domain is a dead end beyond this despite a few other checks. However, they do have a Facebook page which has a ton of additional information:
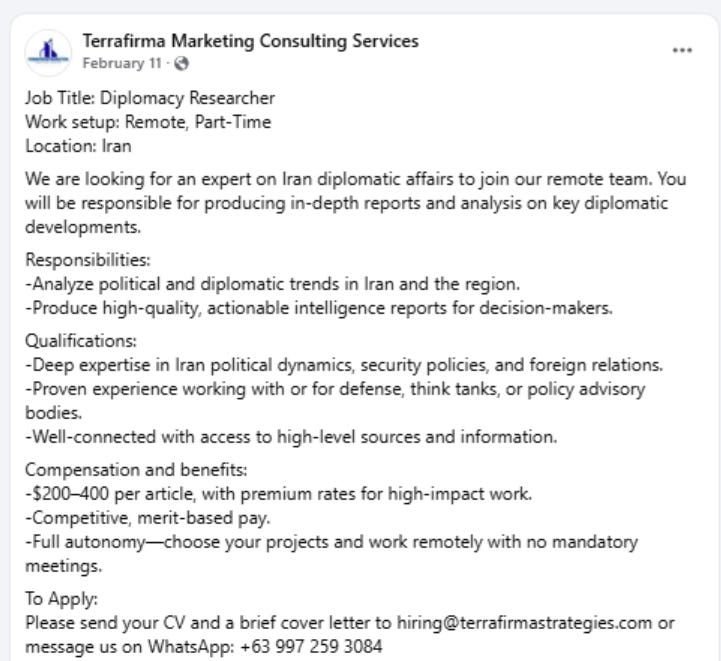
We can already see that they have other postings on here, including Qatar, as shown above. Iran is also listed:
As are Bangladesh and the Maldives:
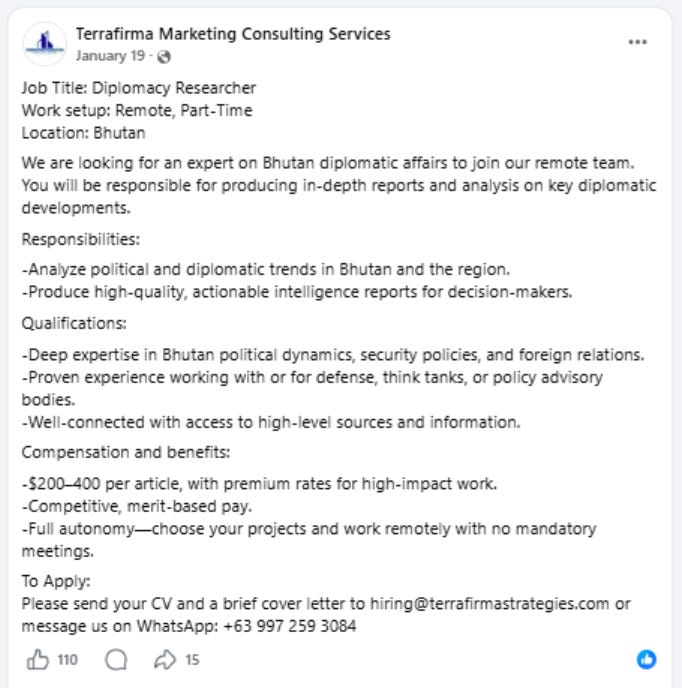
Bhutan even gets a shoutout:
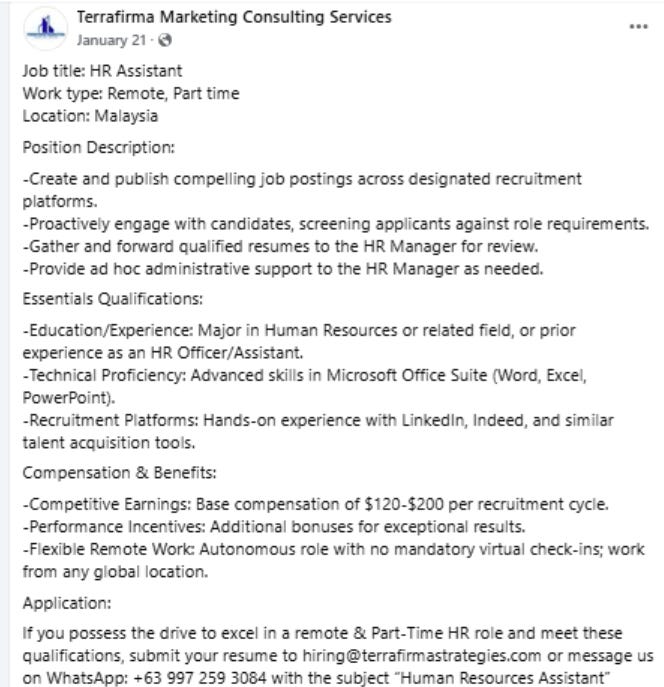
The page has also tried to hire an HR assistant in Malaysia with bonuses based on successful recruitment:
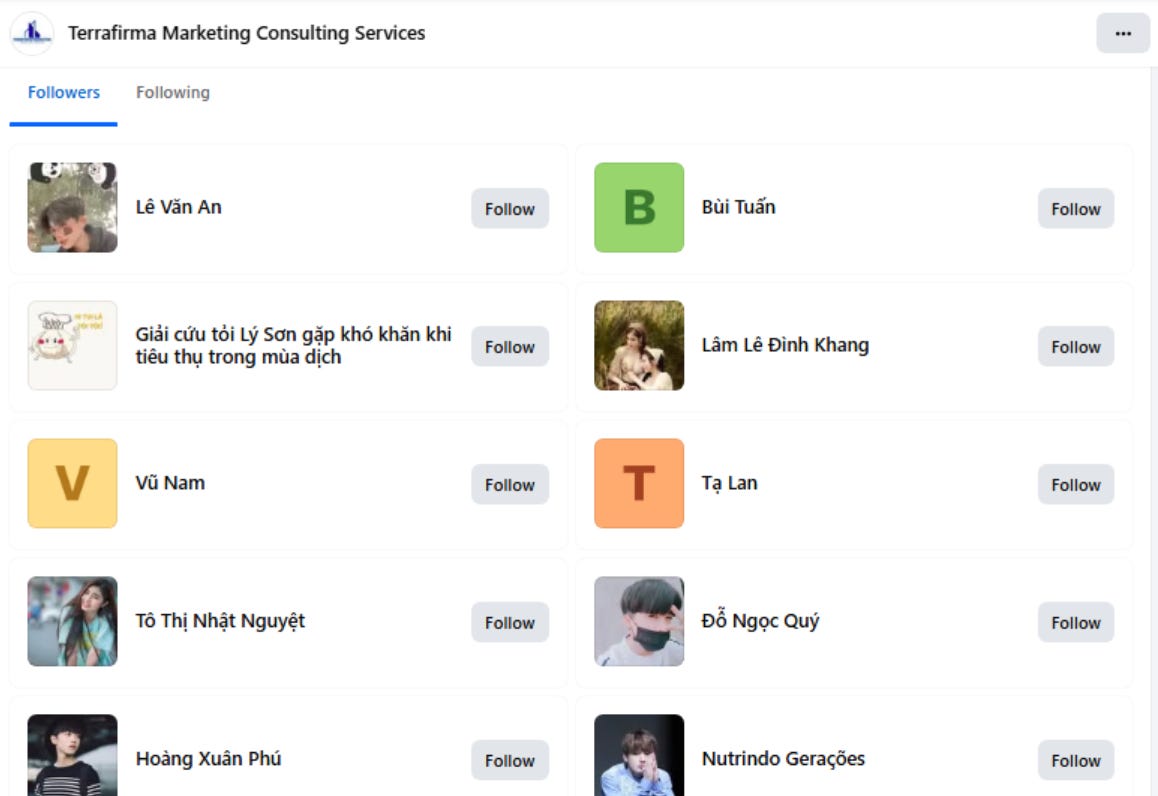
The page also tries to juice its engagement numbers, with early posts receiving dozens or 100+ likes or comments. Later posts dropped the fake engagement stats, but the followers - almost all of which are fake Vietnamese or Bangladeshi accounts - show that they paid for a few hundred at least.
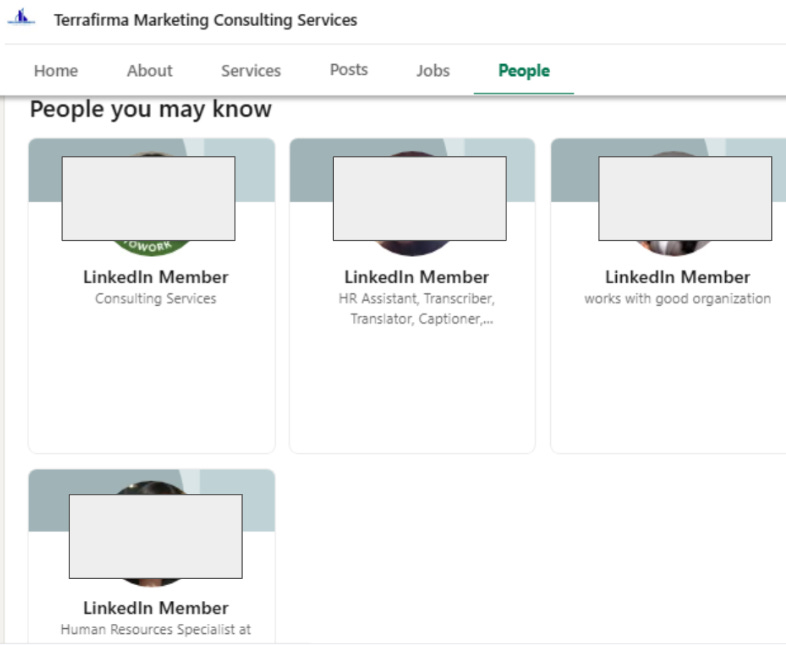
The LinkedIn page has a few employees, all of whom seem real. A few appear to be based in the Philippines, and based on the slightly different name, they probably were hired legitimately by whoever is running this operation.
The employees also share postings, including for other regions previously not seen:
Not a ton there, but it is interesting to see that some people were actually roped into this to work on it. That’s a level of investment not usually seen.
So, that aside, why is this interesting? Well, beyond my own personal and abiding interest in the topic, it’s a unique operation.
Firstly, the seemingly Chinese domain is interesting because it targets areas not often seen that are of strategic interest to China.
Secondly, the US and Taiwan have been leading targets, though this domain targets India, Syria, Israel, Iran, Qatar, Bhutan, the Maldives, the Sahel, and other regions, many of which I believe are firsts for China, at least Israel is.
The choices align with an increased Chinese interest in the Middle East due to the ongoing war (check out a blog post from Checkpoint on Chinese cyber espionage targeting Qatar around the same time period) and the need to understand what exactly those pesky Middle-Easterners are up to.
Lastly, the domain uses the Philippines as its listed location. This is in contrast to past domains, which were often based in Hong Kong, Taiwan, Singapore or the US.
The choice of Manila could be due to a few reasons. It’s feasible that Manila seems to be a neutral choice for global recruitment, and it’s also possbile that the domain seeks to avoid detection by adopting a different visage.
A few final words. These domains often seem comical or unserious to outside observers. The NYT article shows that these operations do actively reach out and can even perhaps enjoy some success, though in this case it was quickly foiled. Softer targets than House committees may easily fall for this type of operation, which - not dissimilarly to China’s approach to influence operations - throws some caution to the wind to scale up.
That’s it for this week, thanks for reading.