So long, and thanks for all the defish
Welcome to Memetic Warfare.
We have a few things to look at this week.
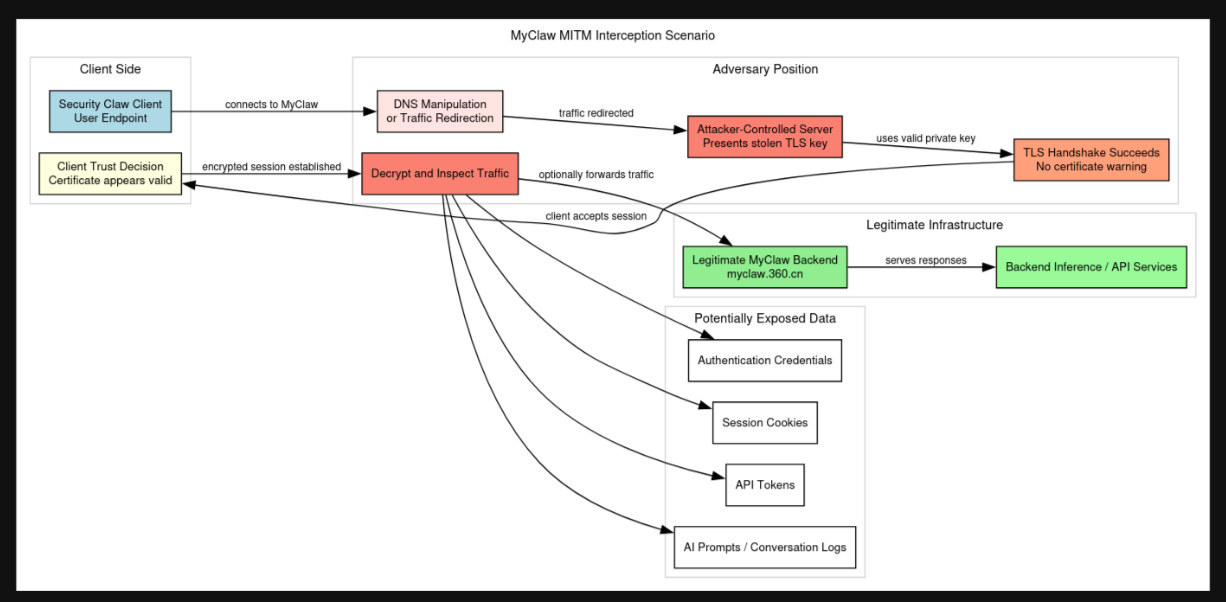
Firstly, we’ll start off with Domaintools Threat Intelligence’s latest look at the accidental exposure of a TLS certificate private key in Qihoo 360’s latest security automation product. Very interesting to get a look at how China’s premier information security company operates.
In addition to always being highly detailed and high quality, DTI also often puts out useful visuals and explains in-depth what’s going on. As someone whose learning journey has relied very much on blogs and technical writeups, I’m always appreciative of companies that take the time to do this:
From there, we’ll check out the FBI’s latest advisory on Iran, specifically the use of Telegram as C2 infra from the MOIS for cyber-enabled IO.
On a separate note, we’re really living in the golden age of MOIS activity, the IRGC used to be the only player in town worth mentioning, not so much anymore.
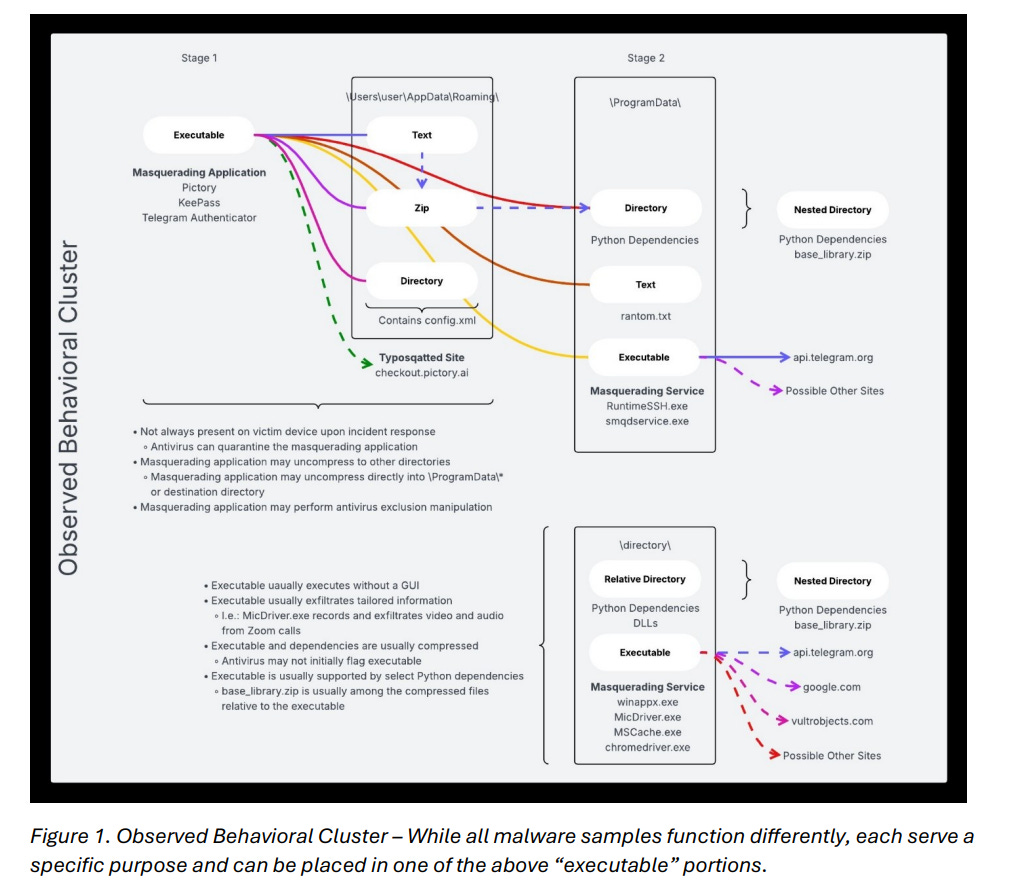
We get some detail here. Nothing super advanced - relies on social engineering to get the malware onto the device by making it appear to be Telegram or some other app (after having presumably messaged the target a malicious link to download it), and then interestingly connected to Telegram bots to exfiltrate the data. We see this confirmed in the “initial access” section:
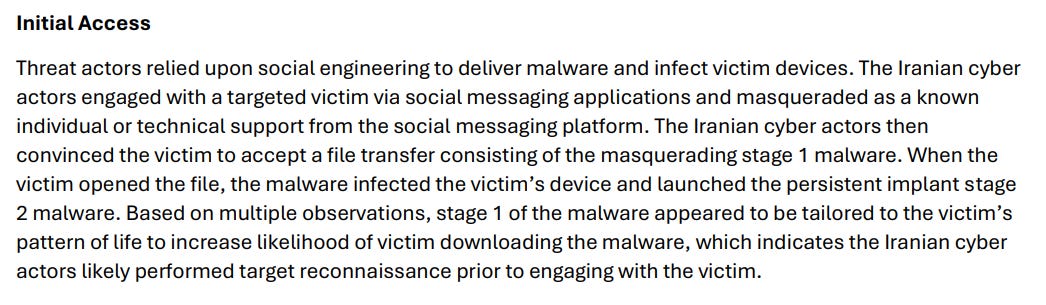
Based on past Iranian operations, it seems that they could only effectively export data from installed apps such as Telegram or perhaps WhatsApp, as most of what I recall we saw came from there, but I could be wrong. This is in fact confirmed in the file names of the malware, showing Telegram, WhatsApp and even KeePass being impersonated:
There’s a specific reference to Handala:
And a broader explanation of how Iranian actors just love doing cyber-enabled IO:
We’ll conclude with what I assume is an AI-generated visual describing the flow:
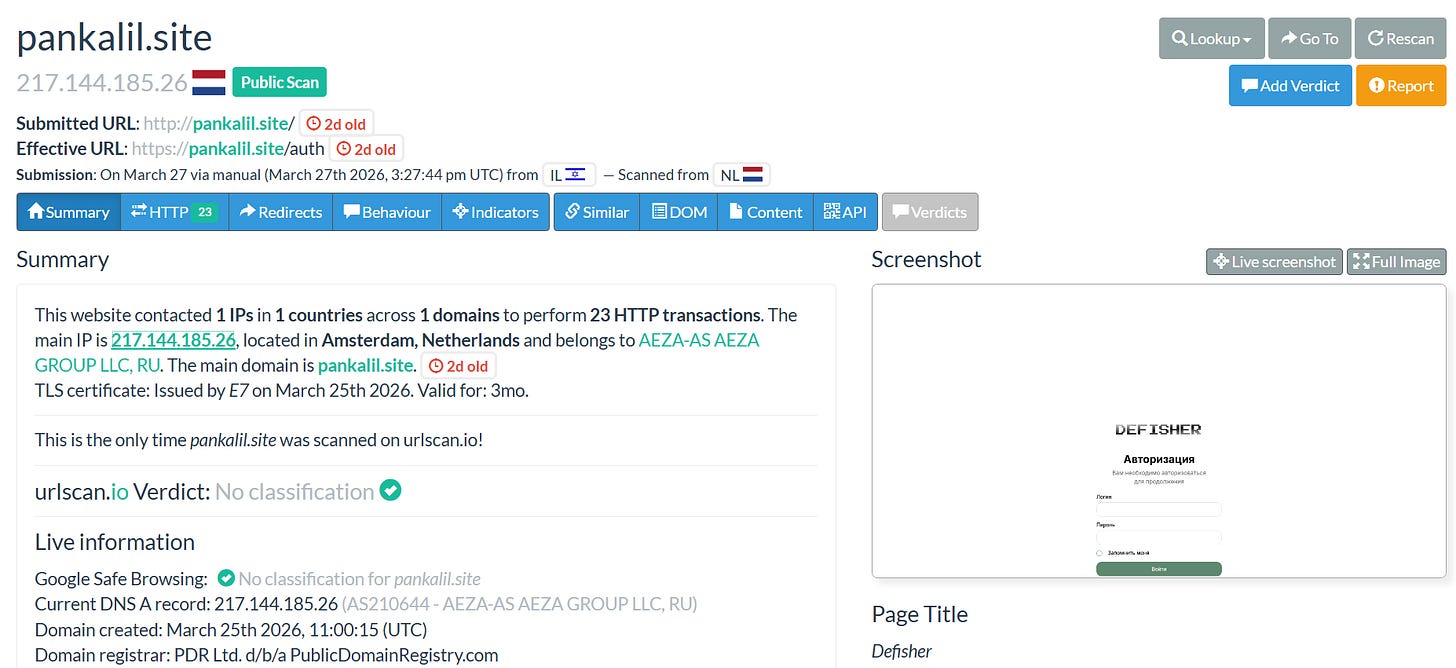
From here, we’ll take a look at a great look from Max Bernhard on a phishing campaign hosted by Aeza targeting European officials over Signal and other applications:
I’ll put the summary below:
Defisher is a commercial tool, and it may be used by other actors beyond whoever was using it before. This is also a stellar example showingthe value of fingerprinting and searches on Censys.
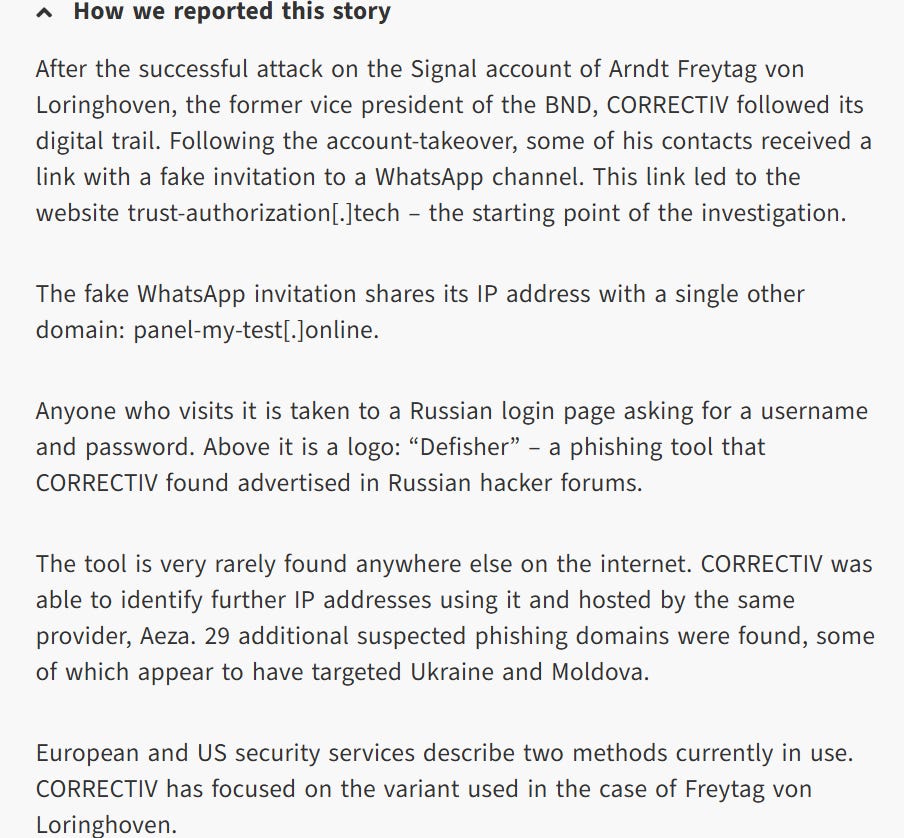
It starts with the Defisher login panel, which may seem mundane. However, like anything unique (ish, in this case), we can find a way to write a unique query for it on Censys to find HTTP responses that match the page content.
The simplest way is to just look up Defisher as it’s the unique component of the panel on Censys, but if this panel were more unique, we could try to write an even more specific query to find exact pages that this panel appear on.
We can easily check that out by trying to fingerprint the panel, in this case just looking up “defisher” in Censys, giving us a domain running HTTP, in this case even having the title be “Defisher”:
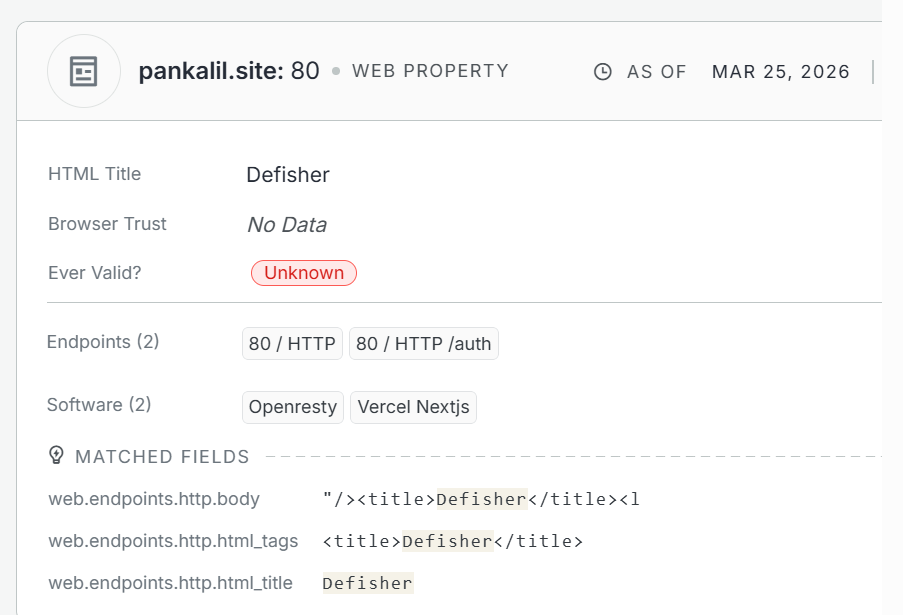
We can easily check this bad boy out and see that it’s another instance of the same panel:
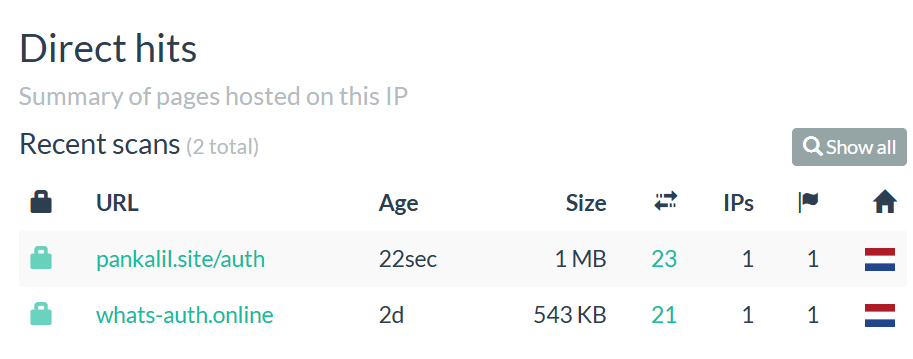
The host server it’s on hosts this site and one other which glaringly imitates WhatsApp authentication:
Now, there’s more that one could do with this, but the point here is that by just doing this quick pivoting we found additional instances of defisher being run.
It appears that they’re part of the same campaign,based exclusively on the similarity here of the WhatsApp auth domain and the aforementioned article, but we would have to find other points to line up first before confirming.
That’s it for this week, thanks for reading.