Shingeki no KyOpenAI
Welcome to Memetic Warfare.
What a week, huh?
Let’s get started with some non-Iran related content, as it’s pretty early on and I’ll have more to say I’m sure going forward.
We’ll start off with Open AI’s latest threat report, available here.
We’ll skip the romance scams section and get right to the Silver Lining Playbook section:
Those of you who read MW regularly may be able to guess what I’m referring to here. I, of course, am referring to the fact that Memetic Warfare is the number one place to read about cool online operations before they get referred to in threat reports. Case in point here.
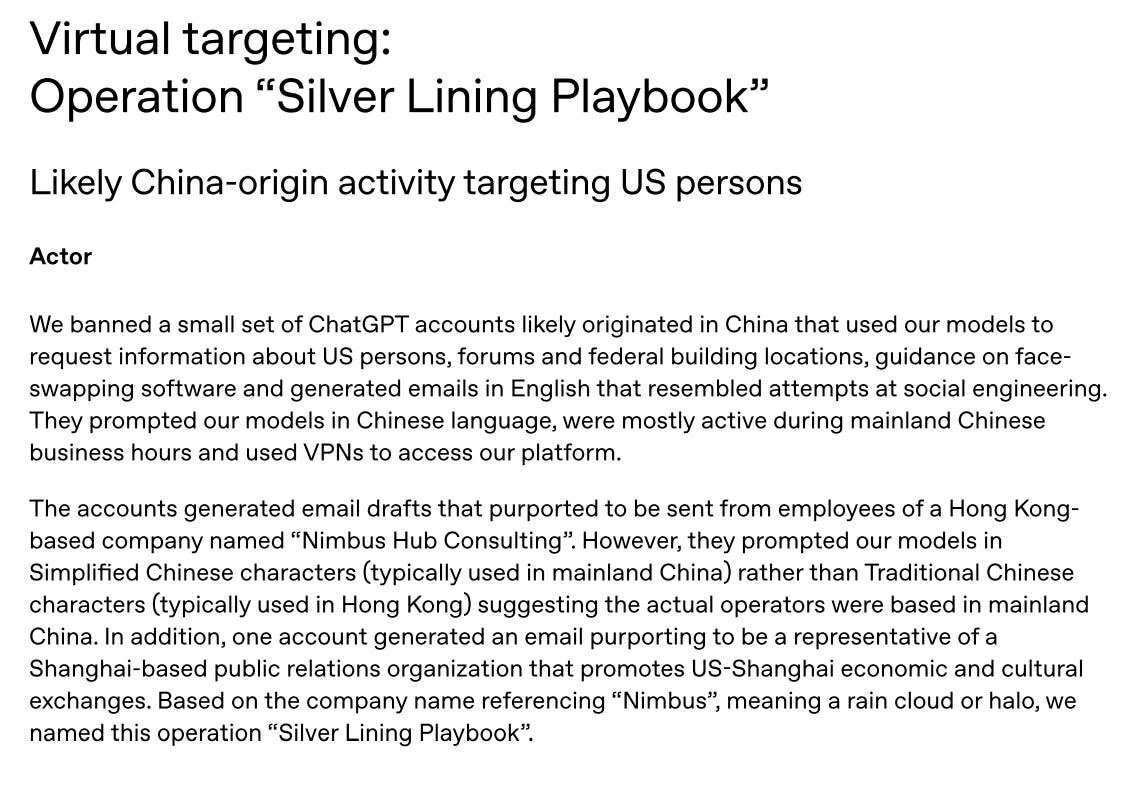
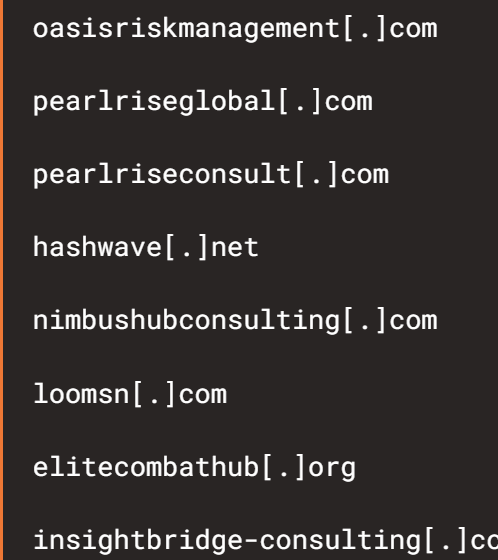
This operation, originating in China (probably, but let’s be real), focuses on actors using ChatGPT to look up people, forums and federal buildings, generate emails, look into face-swapping software and so on - all to serve a front company named “Nimbus Hub Consulting”.
Those of you with a sharp memory may recall this post:
In this guest post by Max Lesser, Nimbus Hub (alongside dozens of other domains) are exposed to be Chinese espionage domains. Give it a read.
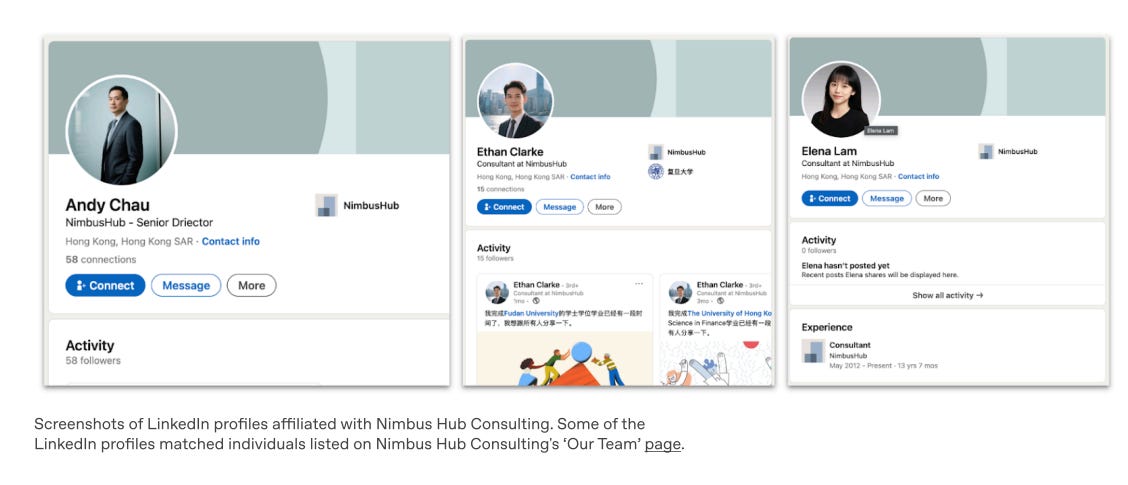
Back to Open AI’s section. They add relevant information from LinkedIn activity (useful as well because they have access to telemetry by virtue of all being under Microsoft)
We also get insight into what they were querying - mainly using ChatGPT to write emails for recruitment, but also carrying out reconaissance on federal employees, their locations, job seekers and more. The face-swapping part is also interesting and presumably to be used in any face to face interaction.
That becomes clearer as we see the type of emails they’d write:
While great from Open AI, this is only a very small part of the puzzle, and it would’ve been nice of them to include a reference to MW or the FDD piece on it for further context as well as credit.
We’ll skip the other influence operations which are pretty par for the course, if still interesting geographically,and go to the most unique section - China’s “Cyber Special Operations”.
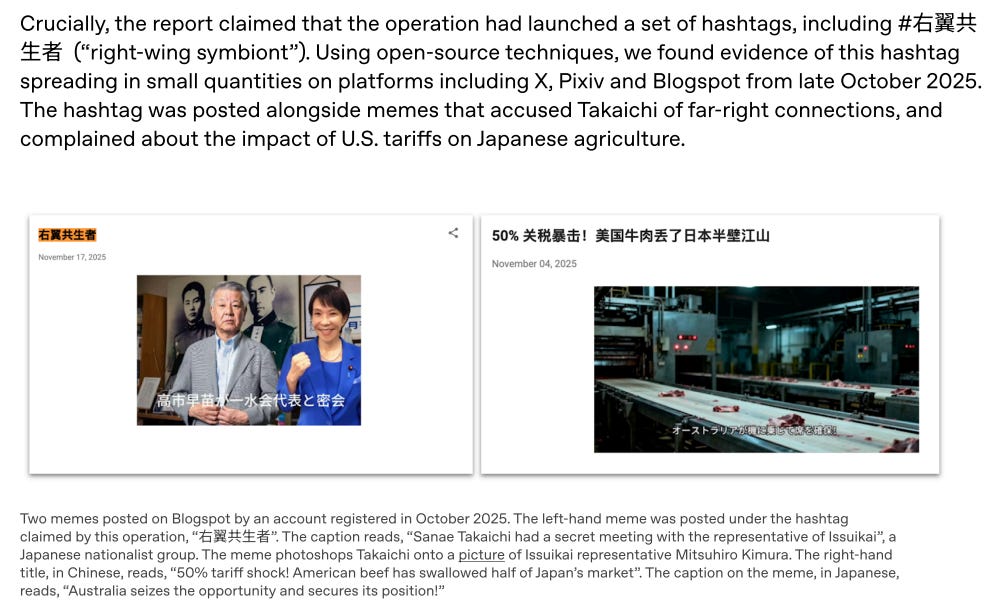
Because the Chinese simply do not care about exposure or OpSec, a Chinese official affiliated with a law enforcement body (probably the MPS) used ChatGPT to plan an influence operation targeting Japan:
We see that the user used ChatGPT to generate periodic reports on “cyber special operations” against global targets, showing that apparently Chinese operators use Chinese open-source models and have hundreds of operators (no surprise there). We also see that it’s probably tied to Spamouflage, so further strengthening ties to the MPS:
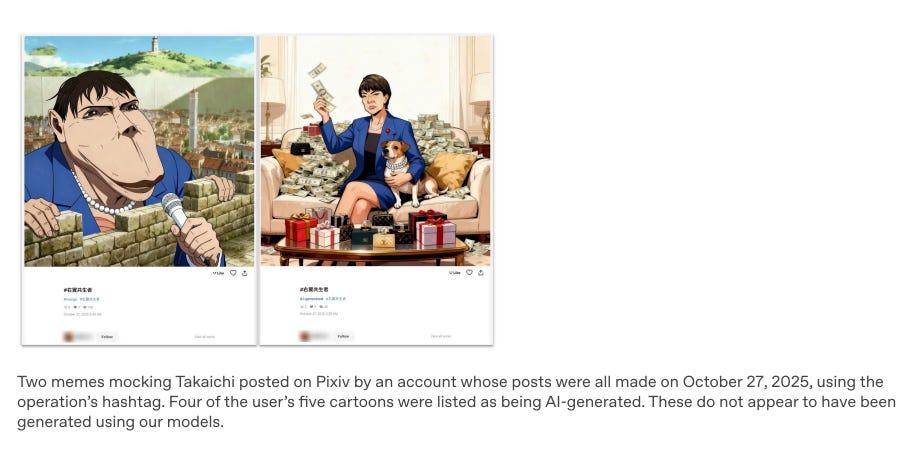
The operators use Qwen and Deepseek apparently, and began planning an operation against Japan’s Iron Lady following her statements re inner Mongolia, the best-named Chinese province. We also get insight into the operation itself, which focused not just on mean tweets but also setting up inauthentic email addresses to email Japanese politicians, “coopting local internet users” and running counter-operations online:
We also get exposure of used hashtags:
I especially like the use of anime to run IO:
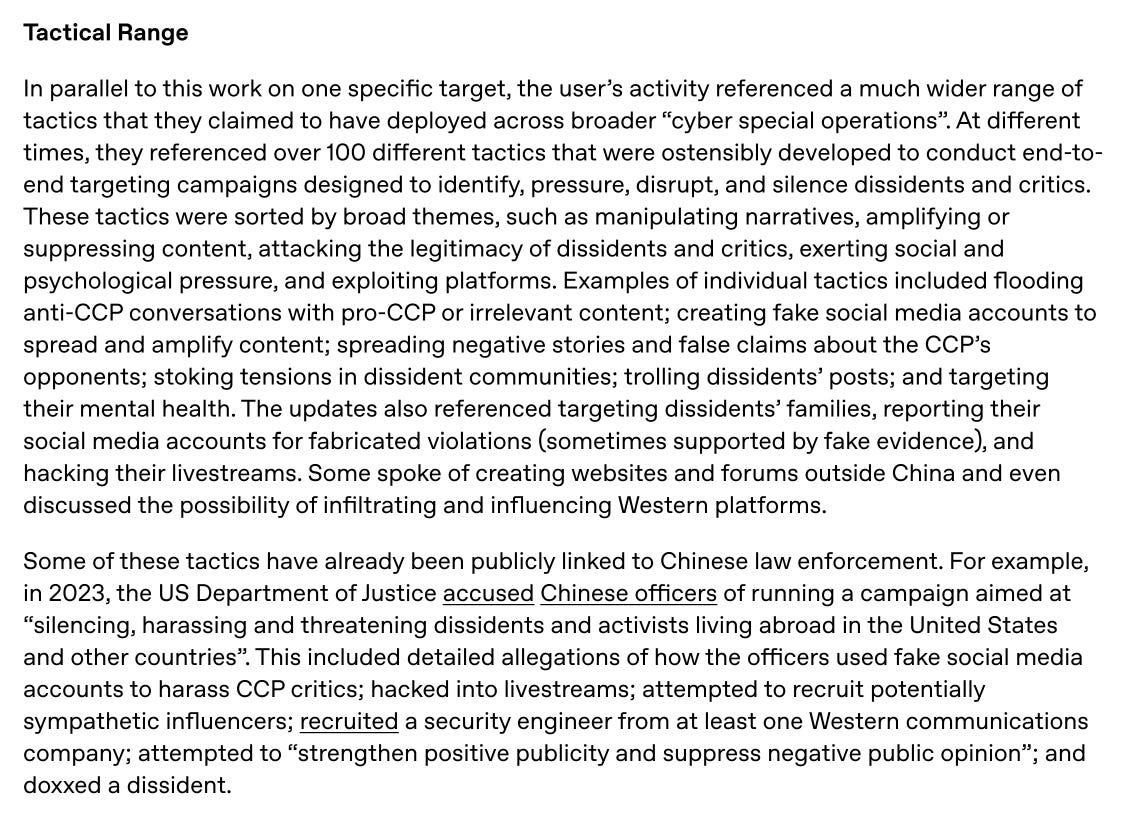
We get even more information re TTPs towards the end, showing how the operator is probably tied to the MPS Working Group 912.
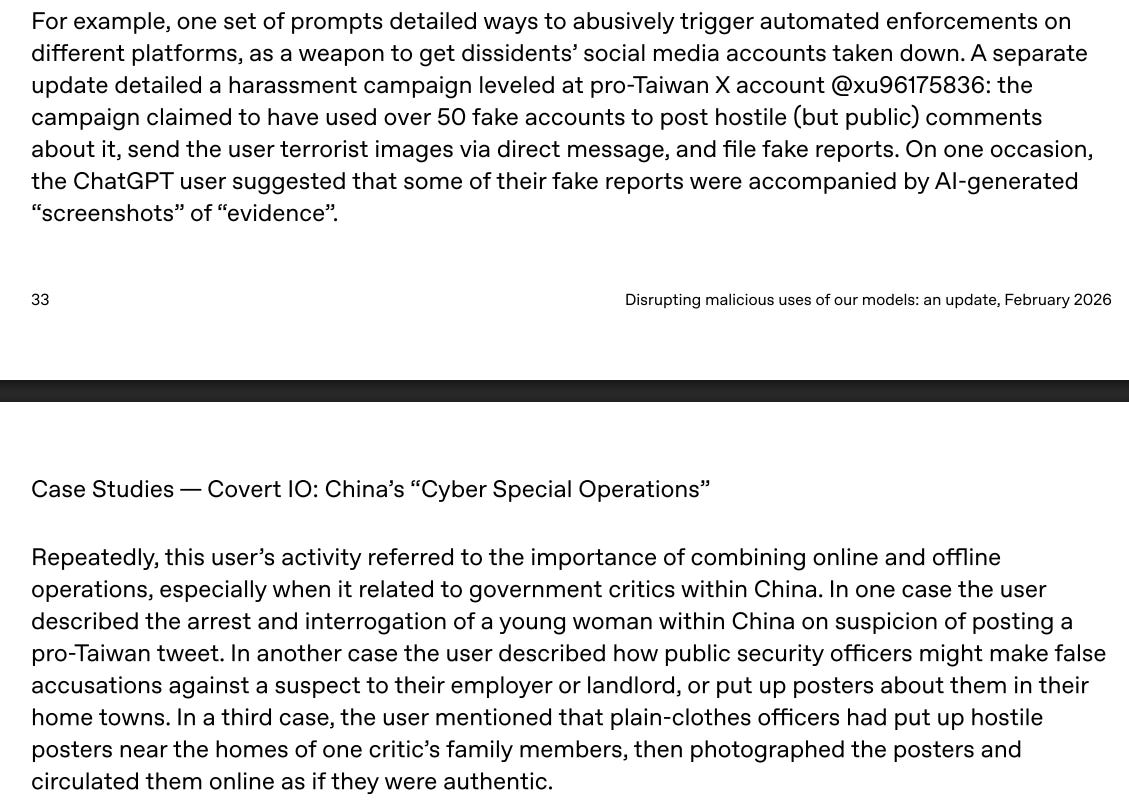
Really interesting information showing domestic and foreign activity:
We get great insight into how China actually runs these operations: hundreds of operators, active on over 300 social media platforms, using AI for monitoring, translation, content generation and more.
That’s it for this week, thanks for reading.