Requiem for a Semiannual Adversarial Threat Report
Welcome to Memetic Warfare.
I’m opening this week’s post with a sad development: the time of death of Meta’s now semiannual threat report, available here.
See the executive summary below and you’ll begin to see why. Firstly, there’s a huge focus on things that are important, sure, like fraud and scams and so on, but these come at the expense of cyber and influence operations, which get short shrift. One could argue that fraud and scams and nudify apps and so on are on the whole worse for society, and that may be true, but it’s still disappointing to see what was once the core of the threat report be relegated to a few pages at the end.
I’m also going to take a moment here to digress. I’ve often been pro-Meta in the industry as they were one of the few companies to actually publish, as well as provide account and page transparency as well as an accessible ad library.
One thing they haven’t been good at is sharing credit or cooperating with the community. I’ve shared impactful things with Meta multiple times, only to never hear anything back or see any action take place. I’ve seen Meta report on things covered on my blog or others months before only to see no reference to them. If you aren’t Open AI, Microsoft or one or two other companies, then you aren’t really an industry peer or part of the “research community” as far as Meta goes.
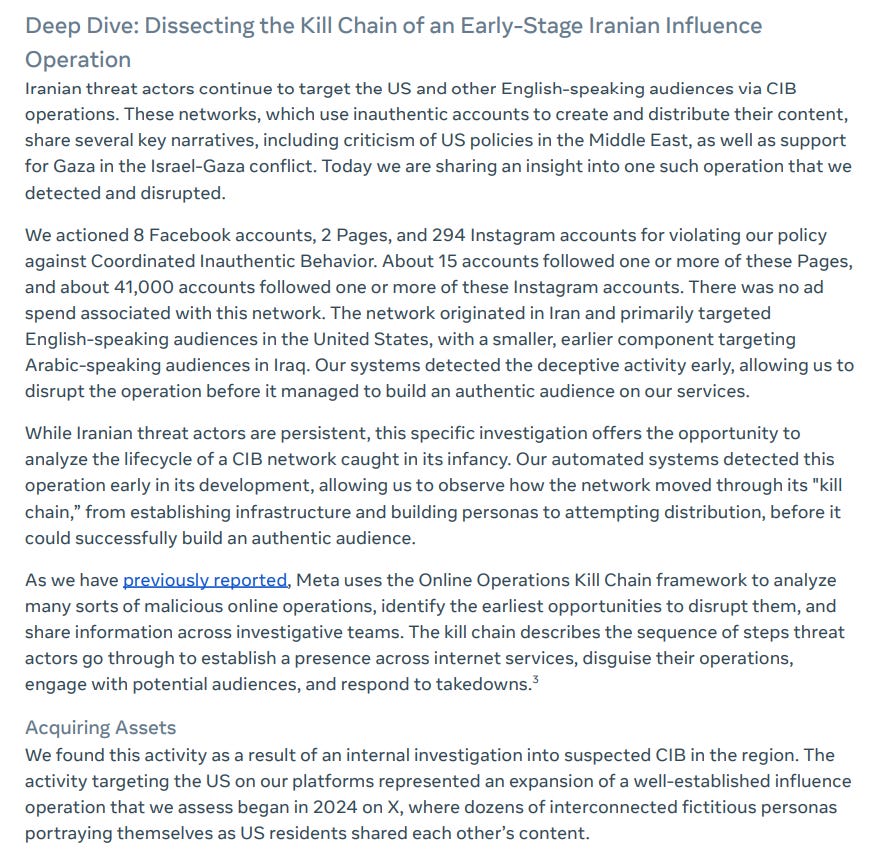
Now that that’s over, let’s move on to what we do have: an Iranian influence operation with some success across Facebook and Instagram. This operation targeted the US with a smaller component targeting Iraq.
We get some information on the background use of infrastructure, for example “clean devices” and “proxy IP usage” - not that that’s so technically-sophisticated per se, though perhaps I’m just biased here and think that’s par for the course. Despite the use of proxy infra, Meta still found “signals” that tied it together, so they clearly weren’t so professional about it.
The information on the identities is interesting - we get political American figures, sure, but also an Albanian satirist, despite Albania not being mentioned in the rest of the report. I assume that the Albanian persona was meant to swing public opinion in Albania (a known thing that Iran focuses on due to the MeK being based there), so odd that Meta didn’t further expand on that.
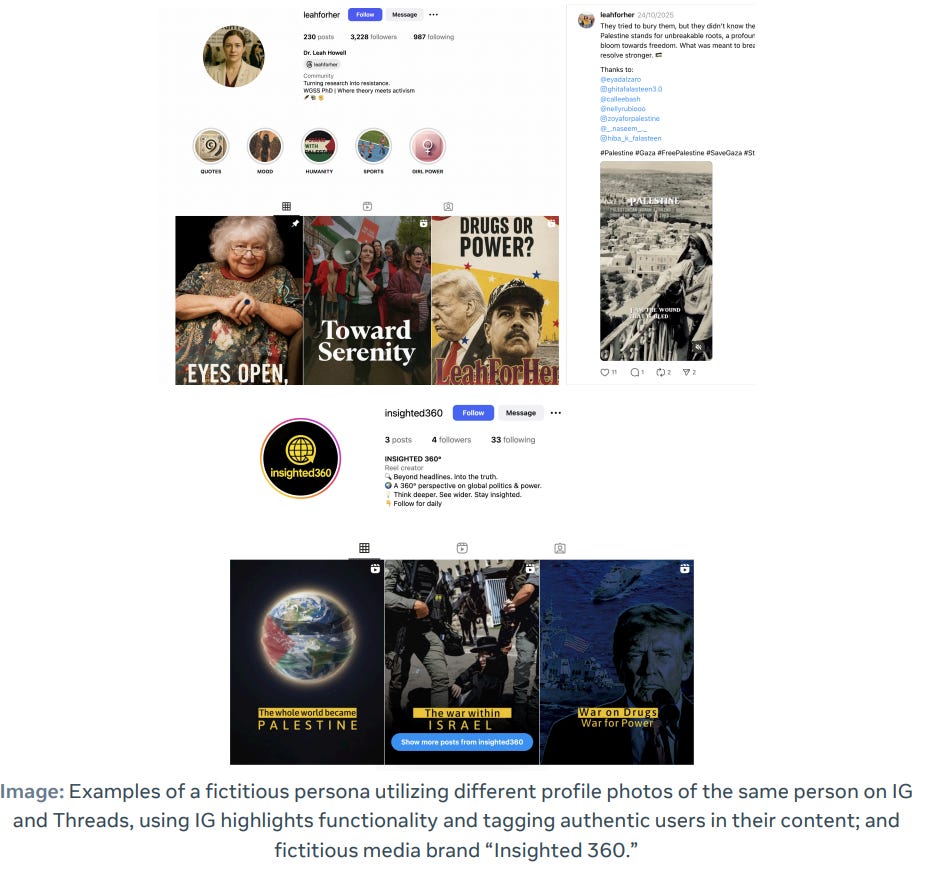
We see the actual accounts below:
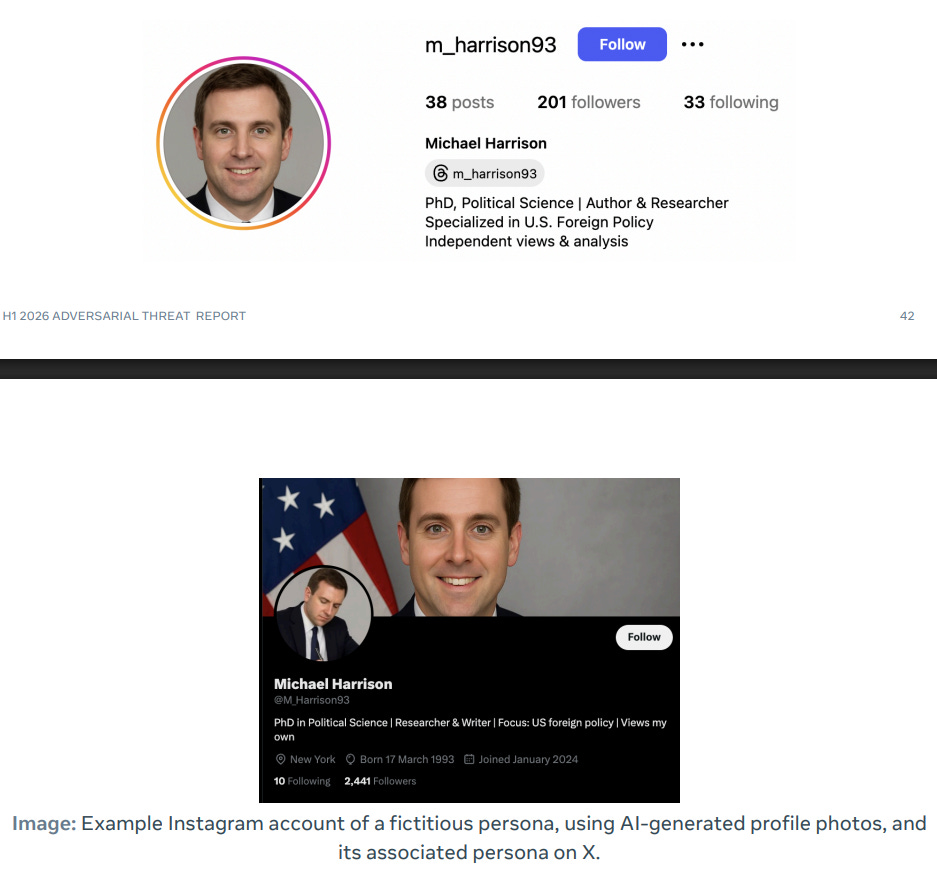
And another, pretty clearly using a GAN image background:
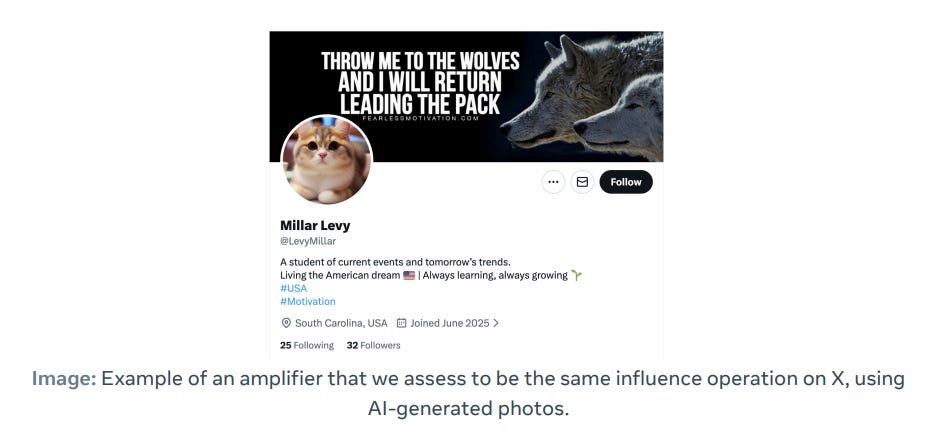
And a last one named “Millar Levy”, a very odd name that I truly can’t pin on any one ethnic group, and certainly not a Jew as Levy would imply.
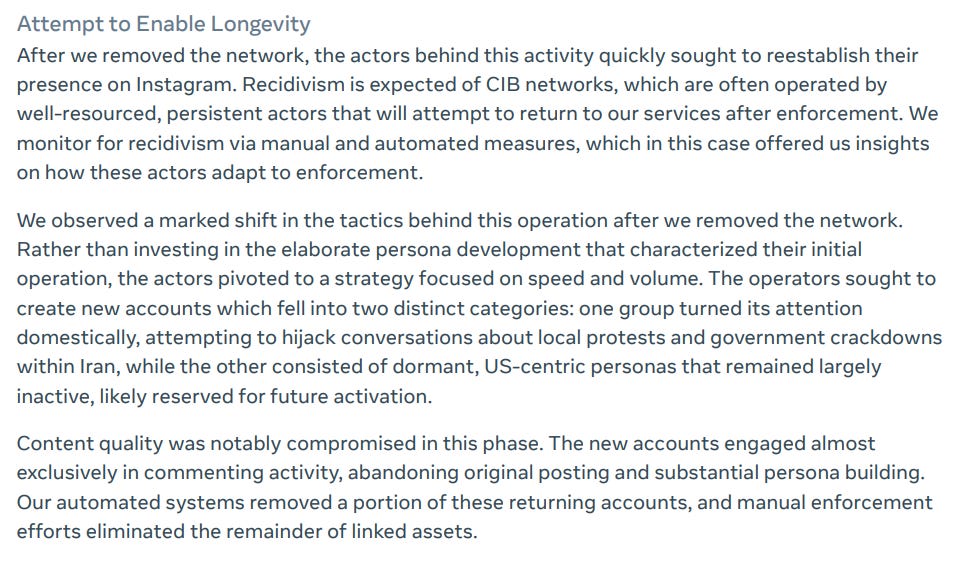
The final interesting note is that once caught, the network “pivoted to a strategy focused on speed and volume”, throwing content quality and abandon to the wind.
We also get some interesting insight into Pakistani domestic activity using AI. The use of AI meme cracks me up, as if it’s at all difficult to use AI nowadays.
Can only imagine which “industry peer” tipped them off to this, and no, I am not hinting that it was me.
We also get some content samples, which is nice because we don’t always get those from Meta:
The AI used is as follows: essentially, at every stage, which makes sense.
We of course have the requisite Russian operations also, showing some success:
The reliance on proxy IP providers is something that, while it’s great that it’s stated by Meta, should be taken for granted at this point.
We also have a Chinese operation with nothing particularly interesting about it.
We also have one final Iranian operation targeting Azerbaijan. This one is interesting in that Meta found that it was run by two Azeris based in both Iran an Germany, as well as the long-running span of the operation and the “high-quality persona building” there.
So, that’s it I guess. The Meta threat report went quarterly, now semiannual, and each time includes significantly less information. That’s life I guess.
Thanks for reading.




CIB dropping as a priority is unfortunate but seems par for the course. Shame because I enjoyed how in depth their
reporting used to be.
It’s a shame that CIB is dropping down the list of priorities even as it becomes more rampant. At least Meta still covers it though.
The amount of obvious disinformation campaigns and propaganda on Reddit has been overwhelming this month. Unsurprisingly, it strongly matches the MO of what I saw after October 7th.
Reddit doesn’t even cover the topic in their security report. I wish there was more research covering that platform. Anyway, thanks for sharing.