El narcocorrido de Handala
Welcome to Memetic Warfare.
We’ll take a look this week at the DOJ’s seizure of four domains related to MOIS operations such as Handala and Homeland Justice, available here.
Let’s take a look at the affidavit. We’ll skip the boring introduction. Getting past the background, at section 8 we see a reference to a “hack targeting REDACTED” in March 2026. Wow, wonder who it could be! I’m fine with most redactions, but if it’s an international headline, you probably don’t need to redact the name.
The redaction here gets to be kind of ludicrous. For example, footnotes 3, 4 and 5 are redacted (for some reason unclear to me, but whatever). The weirdest part is that the example referred to that identified the three as being run by the same actors is redacted, but clearly shows who posted it in the footnote. What is the point here?
Have to give the FBI credit here for coming up with a new term no one has ever used, “faketivist”:
We get a bit of insight into the Handala operation targeting what I presume is Iran International, showing that they were probably phished via Telegram:
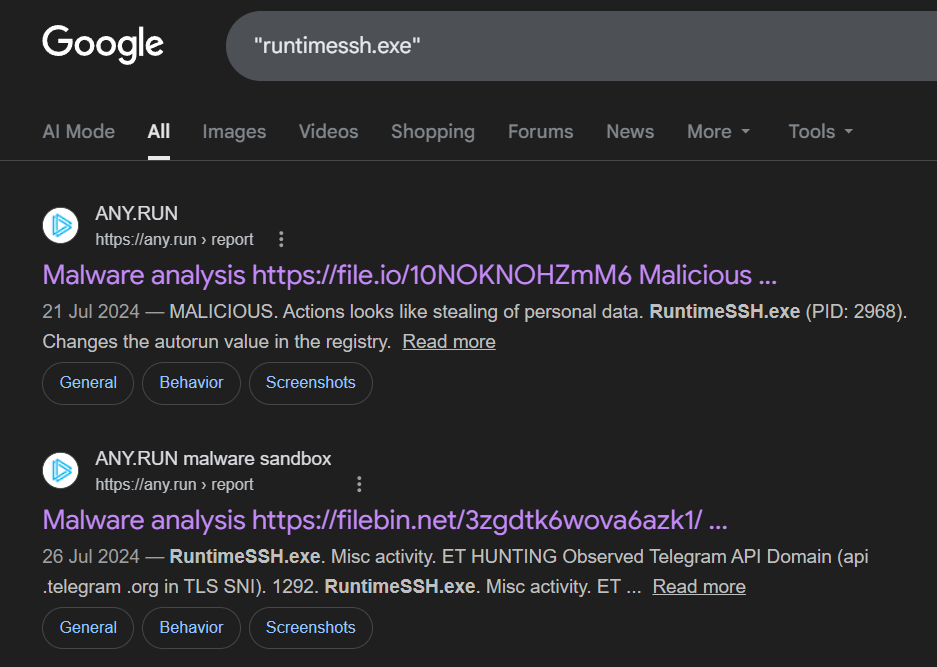
For those curious, if you google “runtimessh.exe”, you’ll find results from AnyRun (similar to VirusTotal):
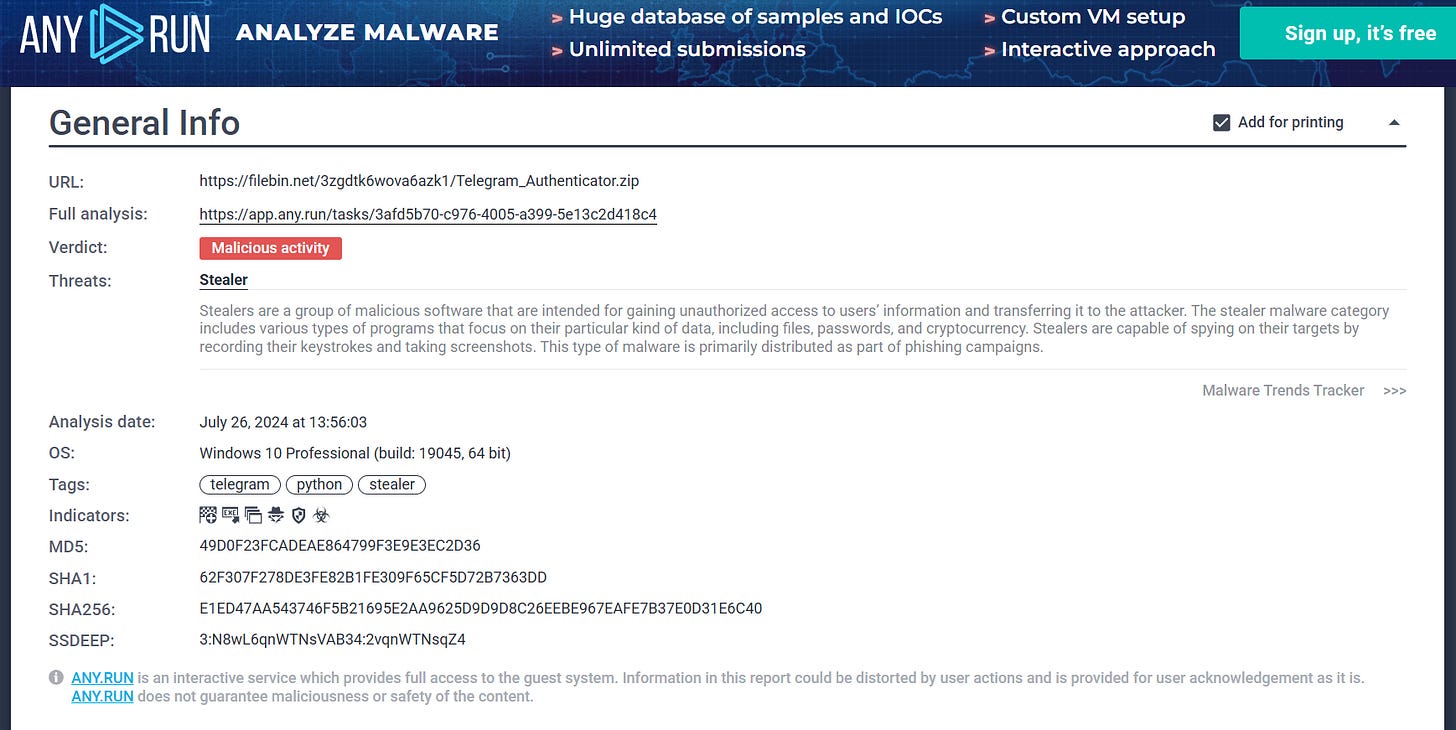
The first one is kind of boring, but the second hit for a past submission shows that the executable appeared in a zip file called “Telegram Authenticator”:
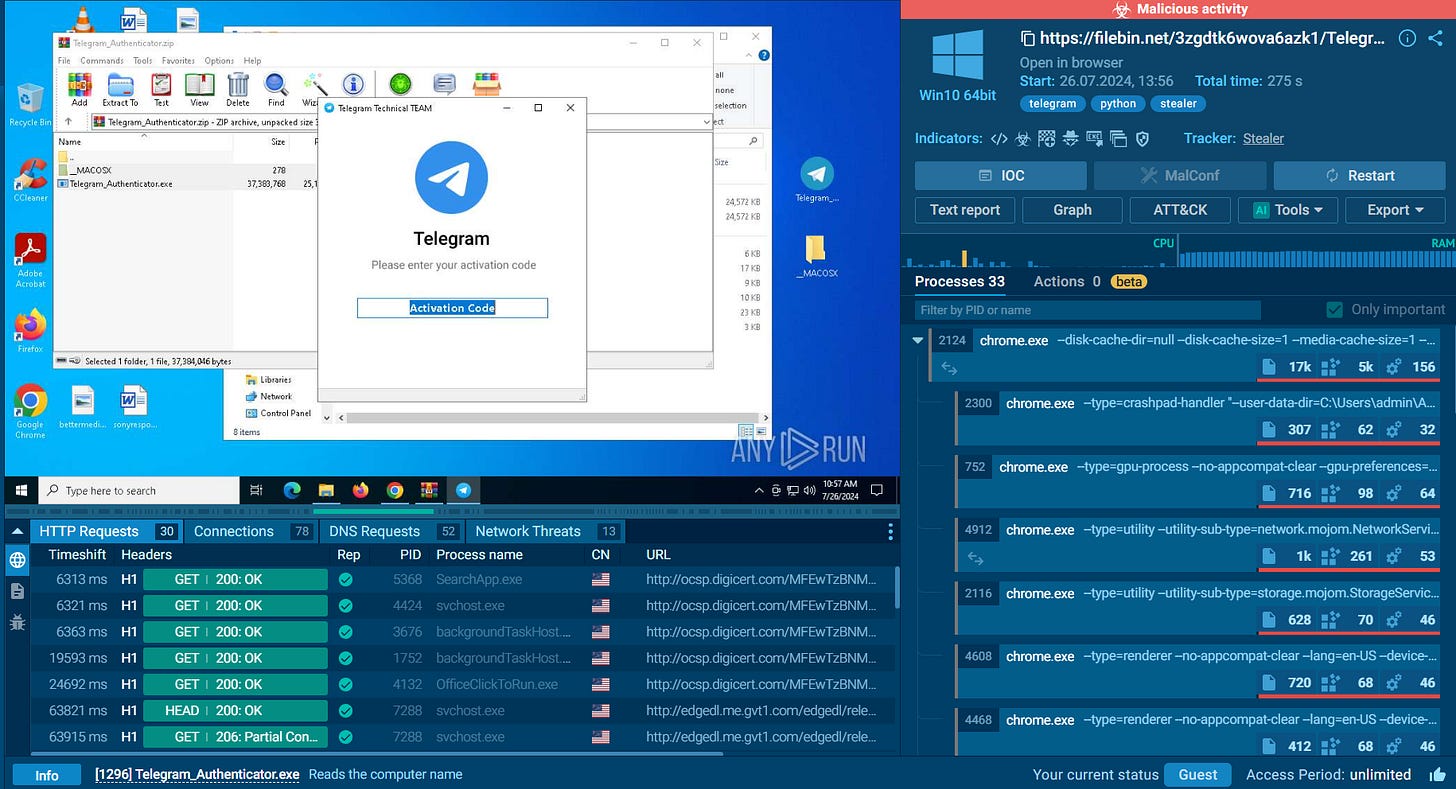
We can then jump to the very cool analysis feature on AnyRun and see them run the file, showing us that it is indeed a Telegram phishing app, masquerading as the “Telegram Technical TEAM” and having people input their activation code:
Shows just how simple a lot of this work can be, even when done to journalists who are constantly targeted.
The next interesting point is the use of crypto to purchase the domain.
I don’t particularly care which exchange it is, but it’s a great usecase for ChatGPT as it provides its own thesis. Interestingly we do see here how they were able to trace it back to an Iranian exchange.
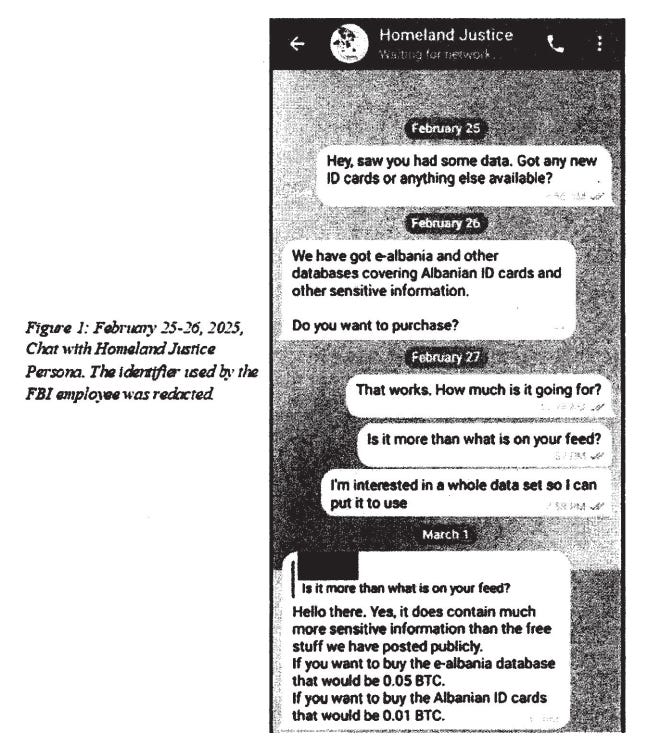
We also get a look at how the FBI runs its own virtual HUMINT operations:
The absolute funniest part of this IMO appears in the message chain:
Just look at how the FBI agent writes. Full sentences, no contractions, absolutely glows in the dark IMO.
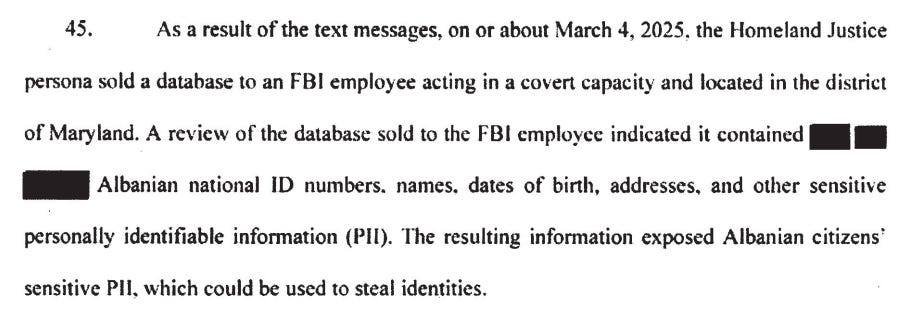
S/he did in fact successfully purchase the data, not hard considering that the goal of this operation is to amplify the hack and leak and get the data out to as many people as possible:
The “Heavygram-Keepass” Malware section seems super interesting but is mostly redacted:
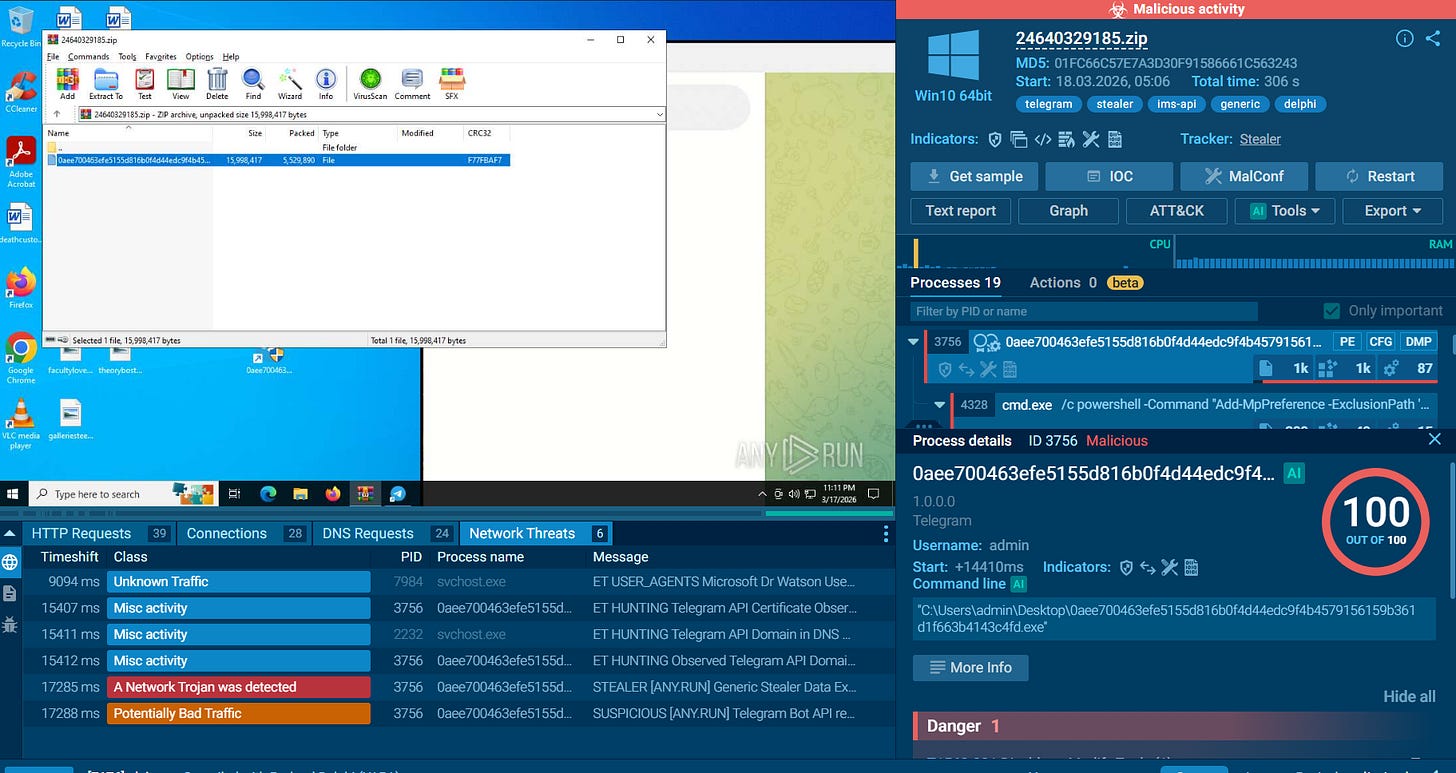
We get a bit in the next page, showing a US victim and again use of the RunTime file as well as an executable called winappx. AnyRun also has this and it too is a stealer, using Telegram to exfiltrate data:
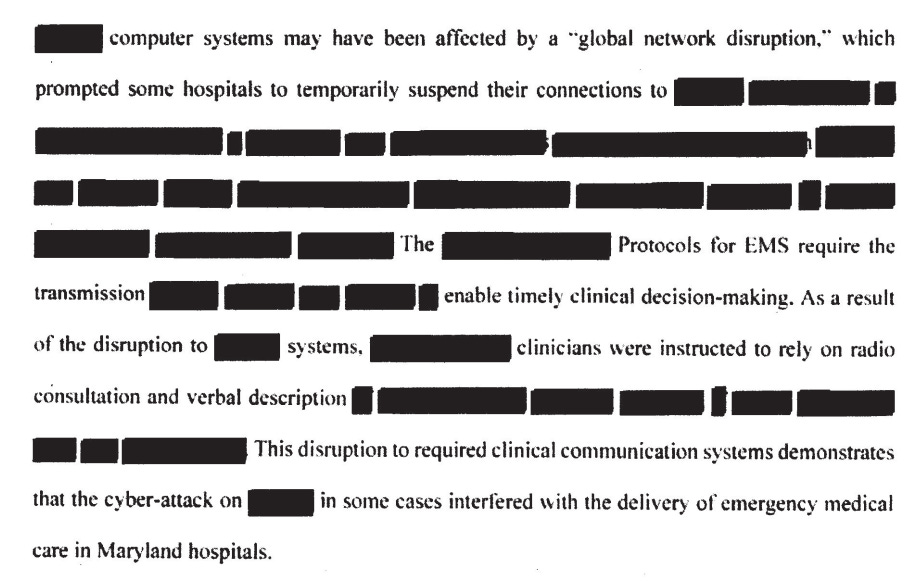
We also get some insight into how the Stryker hack impacted medical services:
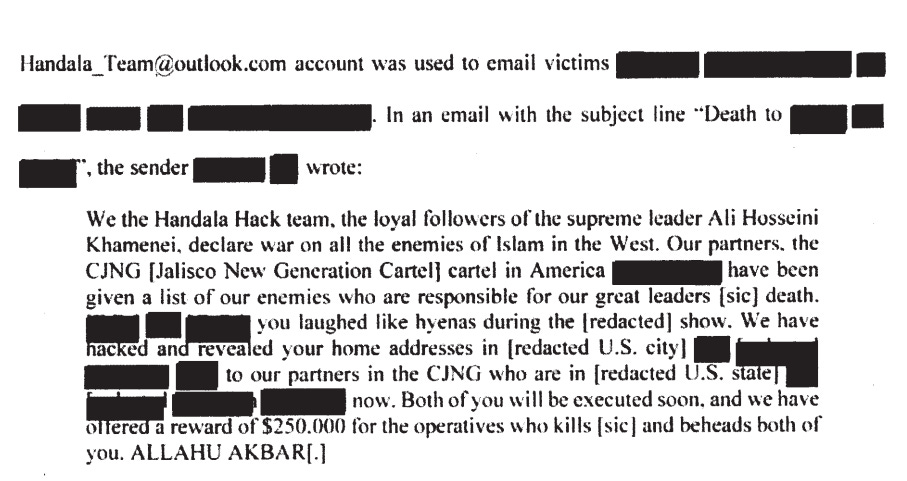
We even get an intimidation email sent by Handala referring to their “partners”, the Mexican Cartel Jalisco Nueve Generacion (CJNG) to indimiate Americans.
We’ll conclude with a final look at a new Iranian recruitment operation, in this case running ads on Israeli news websites:
The post here, titled “Top Secret” and “encrypted”, says that the Islamic Republic of Iran is looking for an “intelligence partner” in Israel, offering 3,500 USD in crypto, which it claims “cannot be discovered”, and also offering “life and location of your choice”, presumably after clicking the ad.
Interesting that they can somehow consistently run these ads on Israeli sites via whichever ad partners they exploit, and it’s an interesting development to see them go right to a news site and not say just on Twitter as in the past.
That’s it for this week, thanks for reading.





UK-based Farsi language services could also be BBC Persian. Who we know they love to target.