Eekad!
Welcome to Memetic Warfare.
We’re taking a special and belated look at my latest long-form publication, focusing on a probably Qatar-linked operation. The report is available here.
The report is quite exhaustive, and there’s much more there so give it a read. I’ll go over some highlights, tips and tricks from the report below.
The operation we’re looking at is named “Eekad”. Eekad, a play on the Arabic root for truth. Eekad has been active since 2020 and positions itself, quite succesfully, as the “Arab region’s first open-source intelligence platform”. They’re on Twitter, YouTube, Facebook, Instagram and a semi-active domain.
What makes them interesting is that they pose as an investigative outfit, and use OSINT in a few key verticals:
Covering influence operations
Debunking viral content
Geolocating content
Social media and other analysis
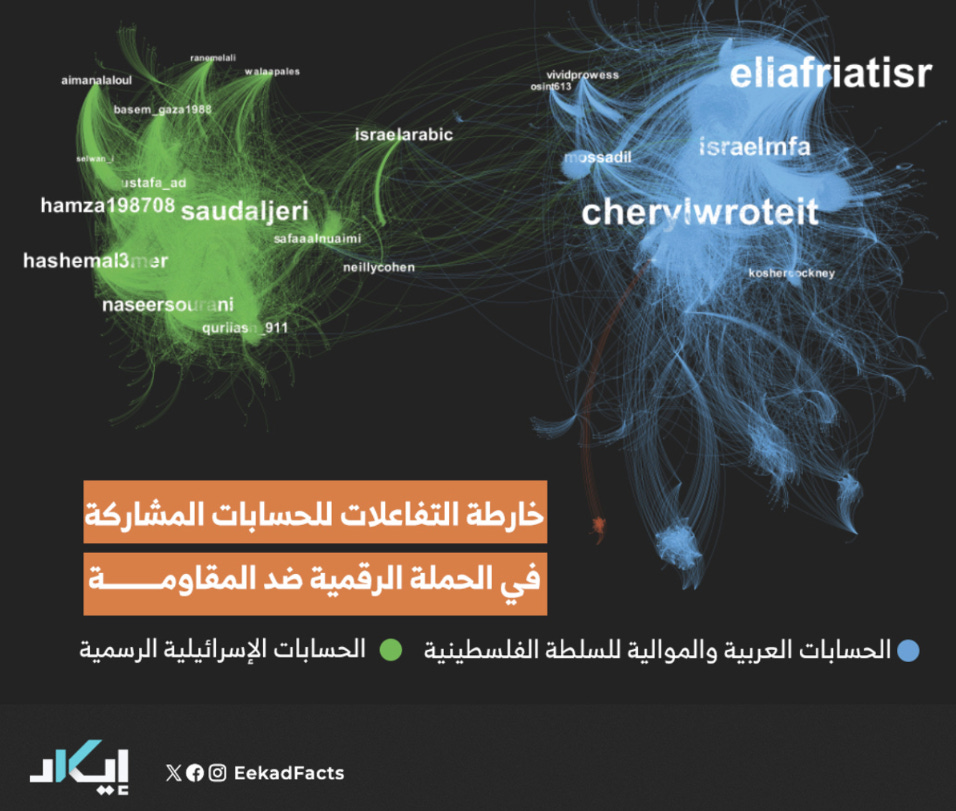
The genius of this operation is that not only is the Arab world is apparently thirsty for this type of content, it provides a visage of legitimacy and accuracy. The average person can’t really tell whether or not satellite imagery is misrepresented, or if the way that Eekad presents impressive Gephi graphs as proof of an influence operation is in fact accurate.
Eekad has been caught promoting unsupported, misleading, inaccurate or overtly false claims on a number of topics - promoting and defending Qatar, denigrating Israel, Saudi Arabia, the UAE and even the Druze, and promoting the current Syrian government. All of these align with Qatari geopolitical interests.
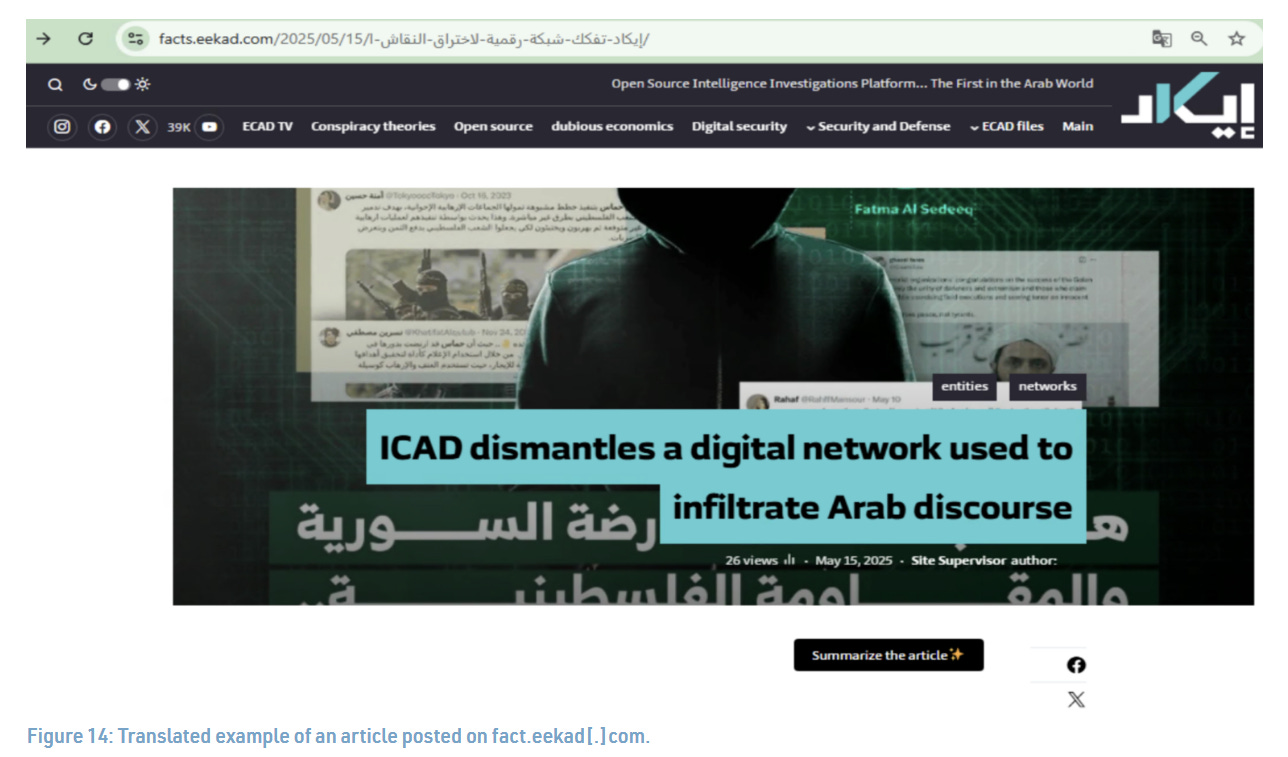
To get a taste for their type of content - check out below some content claiming to expose networks:
On many cases they visualize different networks than the one above with Gephi to make a point that is otherwise unsupported:
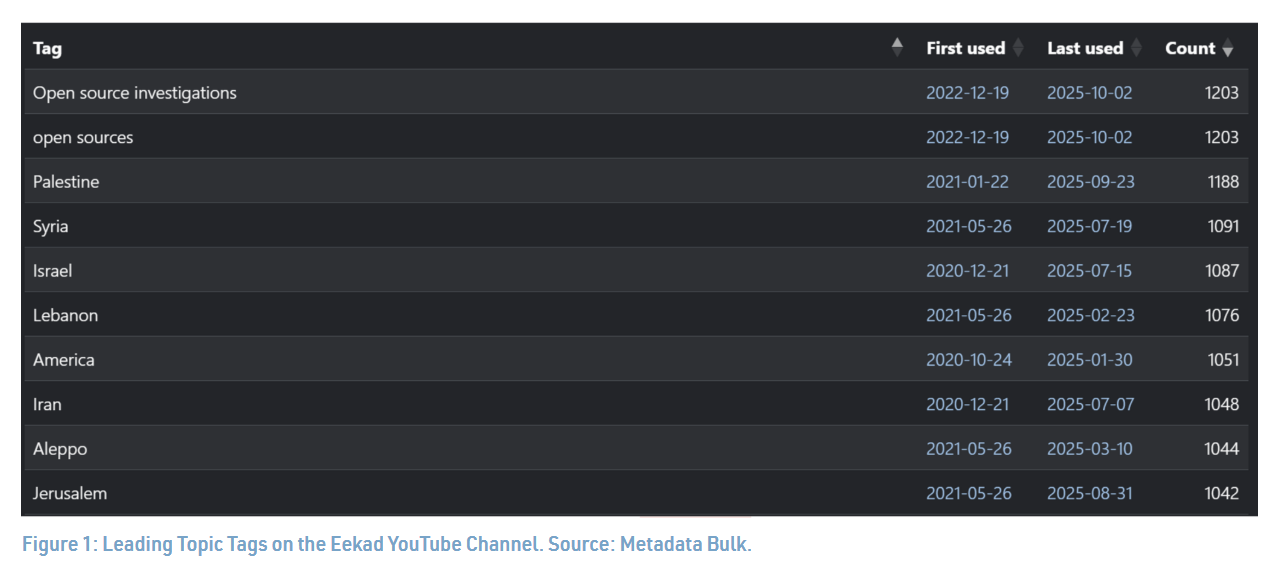
Their emphasis on OSINT is apparent also in their YouTube channel. Open source investigation is their number one videotag. To do this type of analysis yourself, just check out Matt W’s YouTube Metadata bulk here.
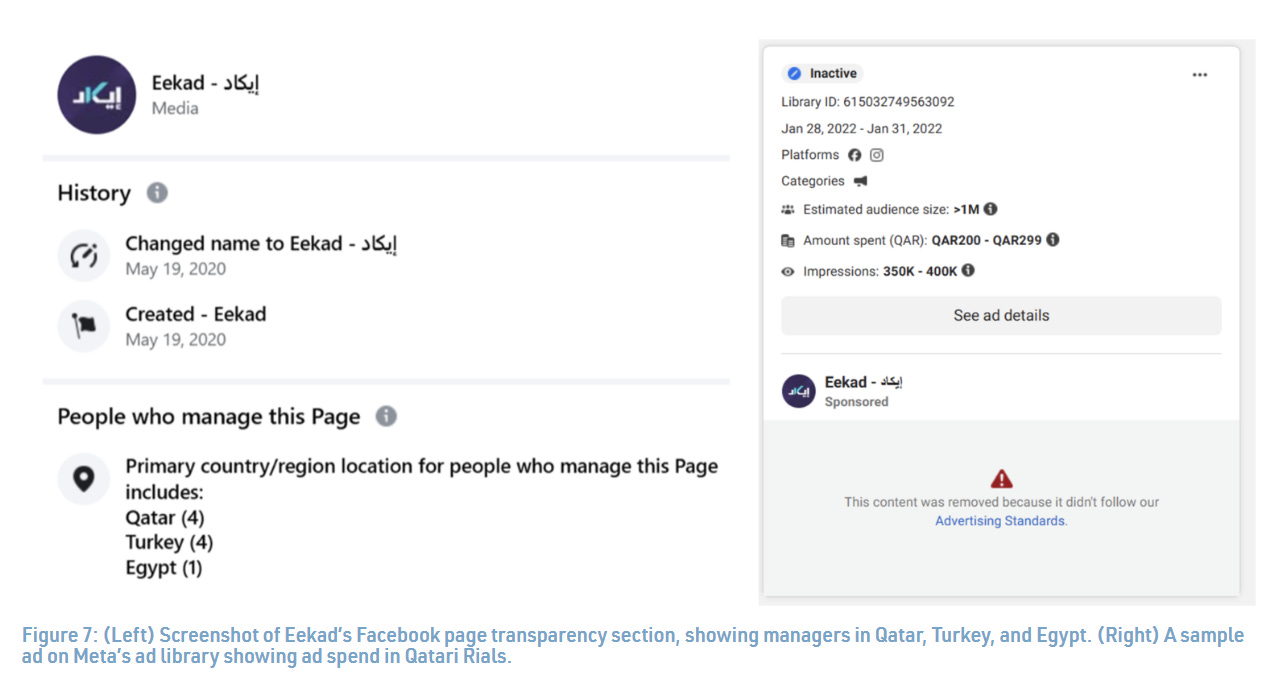
Their Facebook page’s transparency section also includes references to Qatar, as well as Turkey (some employees are based there). Most of their ads were paid for in riyals and taken down due to violating Facebook’s political advertising rules. This is a general investigation tip as well - the FB ad library is amazing.
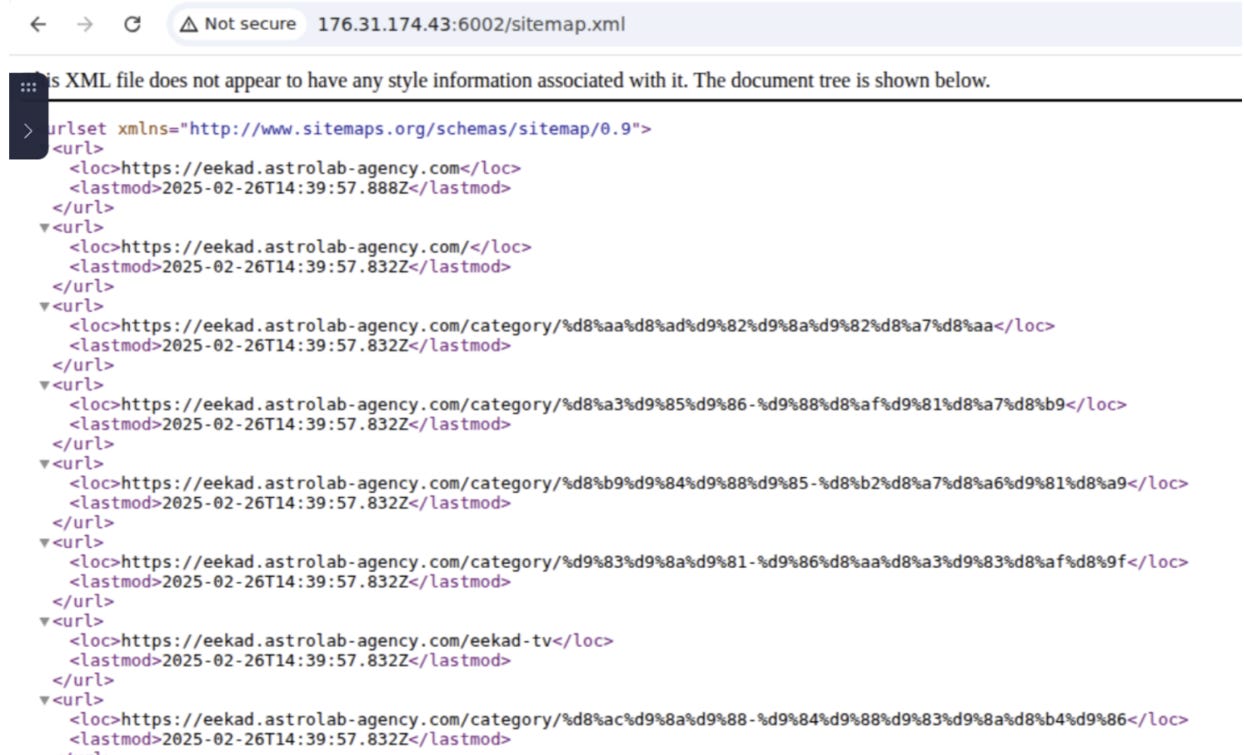
They have an inactive domain at eekad[.]com. However, if you enumerate its subdomains (available with all types of tools), you’ll find a subdomain at facts.eekad[.]com which was inactive for quite a while but at least exposes the original website.
Searching for the domain on Censys exposes one host with Eekad appearing in its HTTP response. This domain belongs to a PR firm, which is hosting a subdomain for Eekad on their own website which hosts an old version of the Eekad domain, showing that they’re tied. So Eekad has some money to throw around for PR firms, which most journalistic outfits of this size don’t.
We’ll conclude with two noteworthy events as well. The first is that Handala set up a domain to solicit information securely from visitors but didn’t bother encrypting the traffic by setting up an SSL cert, which is very funny:
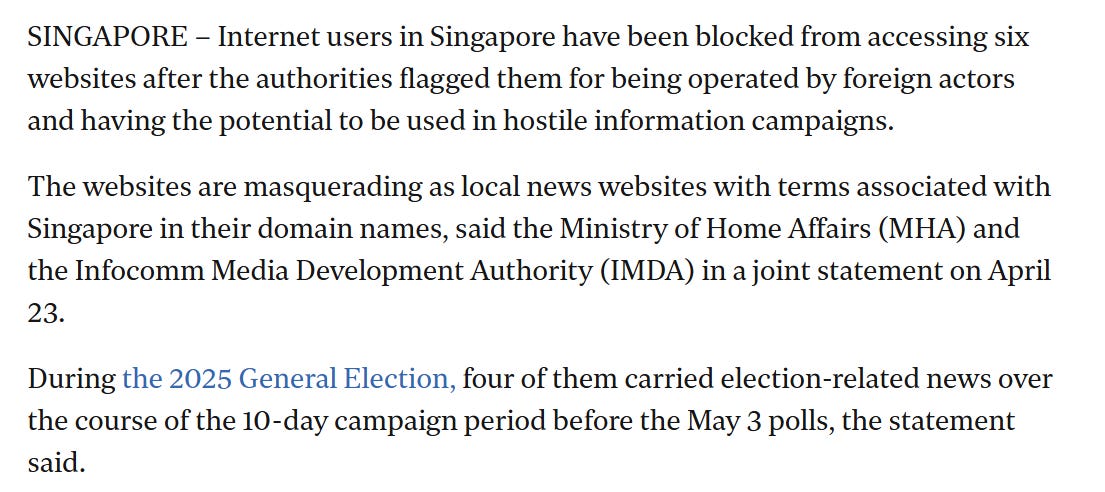
The final thing I’ll point out is Singapore’s takedown of 6 domains seemingly targeting Singapore during its previous election period.
We get some detail below:
The domains are tied to known operations:
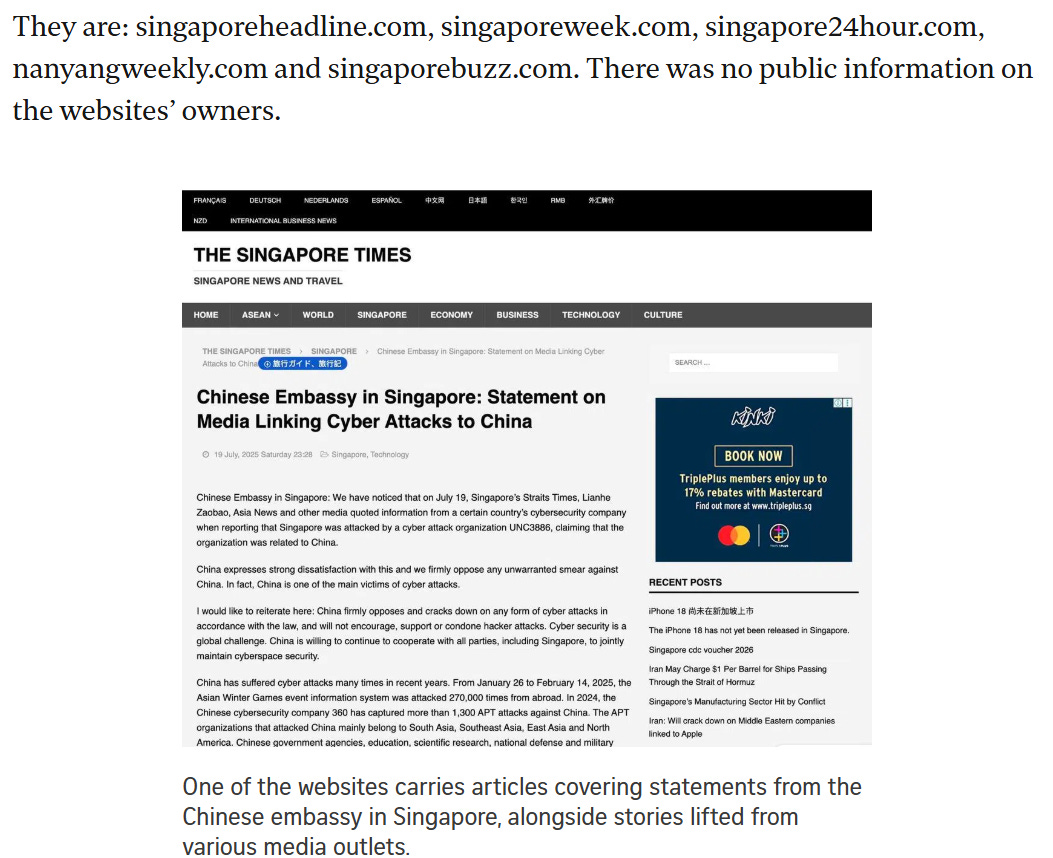
See the domains below:
Interesting to see how Singapore handles foreign influence and interference, managing to take down domains without raising the ire of those seemingly responsible.
That’s it for now, thanks for reading.