Artisanal Wiping
Welcome to Memetic Warfare. This week we’ll take a quick look at Iran’s underwhelming cyber war against Israel.
What caught my eye was an article from the Wall Street Journal covering claims that Iran has wiped at least 60 companies. I hadn’t heard much about a new large-scale wiper campaign, so I decided to take a look.
After checking the usual suspects, I noticed that Anonymous for Justice, known for having popped an email server of the Israeli MOJ in one of Iran’s more successful intrusion ops, was responsible for the lion’s share of these intrusions.
As a side note, I’ve always wanted to publish more on Anonymous for Justice but there’s an Israeli gag order on it, so I’ve held off. Perhaps one day I’ll be able to get something out on them.
I was ready to be impressed with perhaps some new malware or tooling, or some impressive targets. Instead, they’ve been hitting quite literally whatever they can, including Israel’s most reputable and well-known food powder companies:
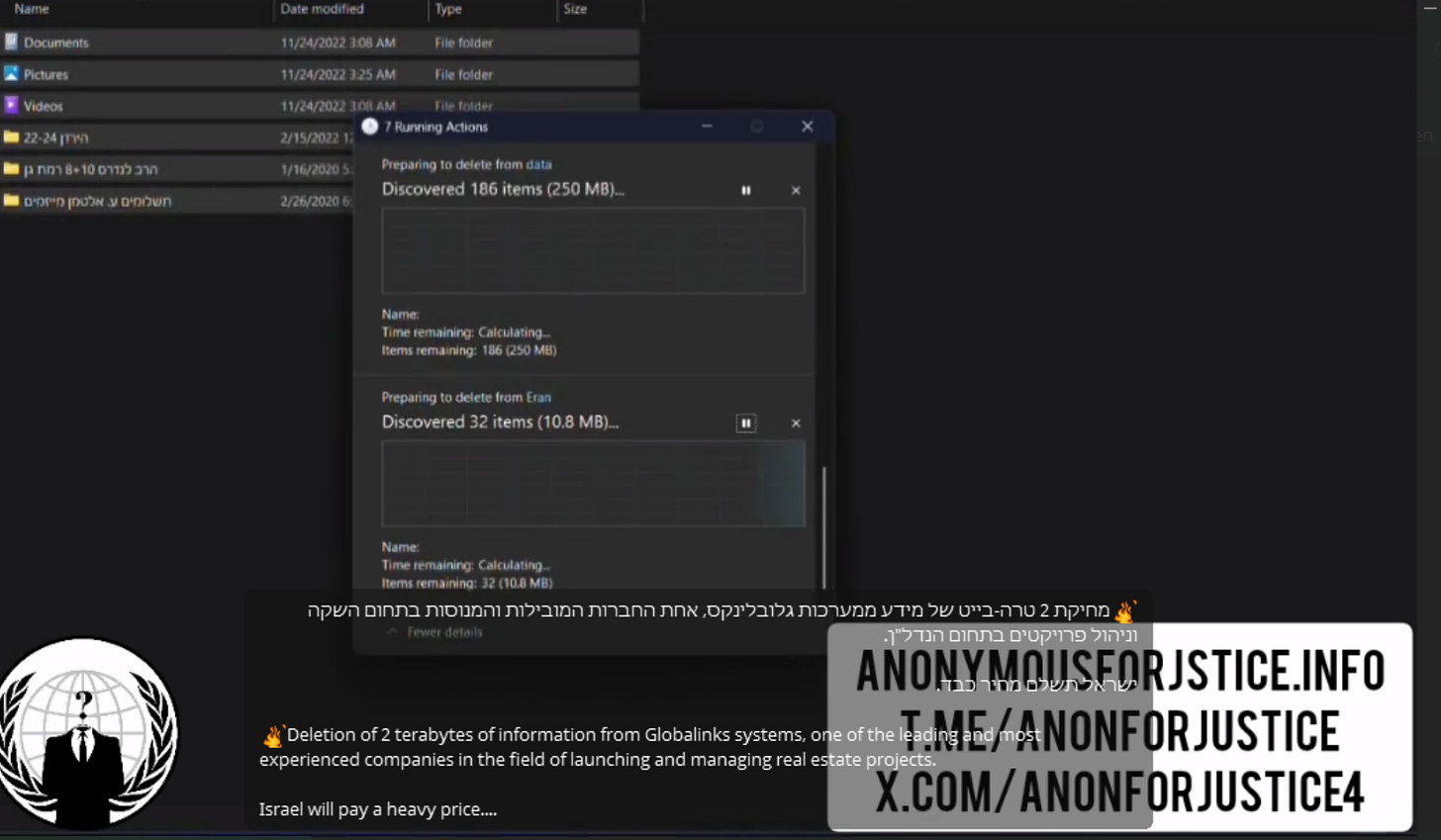
The best part though is seeing them delete the data. In the few dozen videos they’ve uploaded, you can see videos at 2-3x speed of them manually deleting files. They were in such a hurry to do this that they couldn’t automate it or use previous wiper toolkits, which is interesting in of itself.
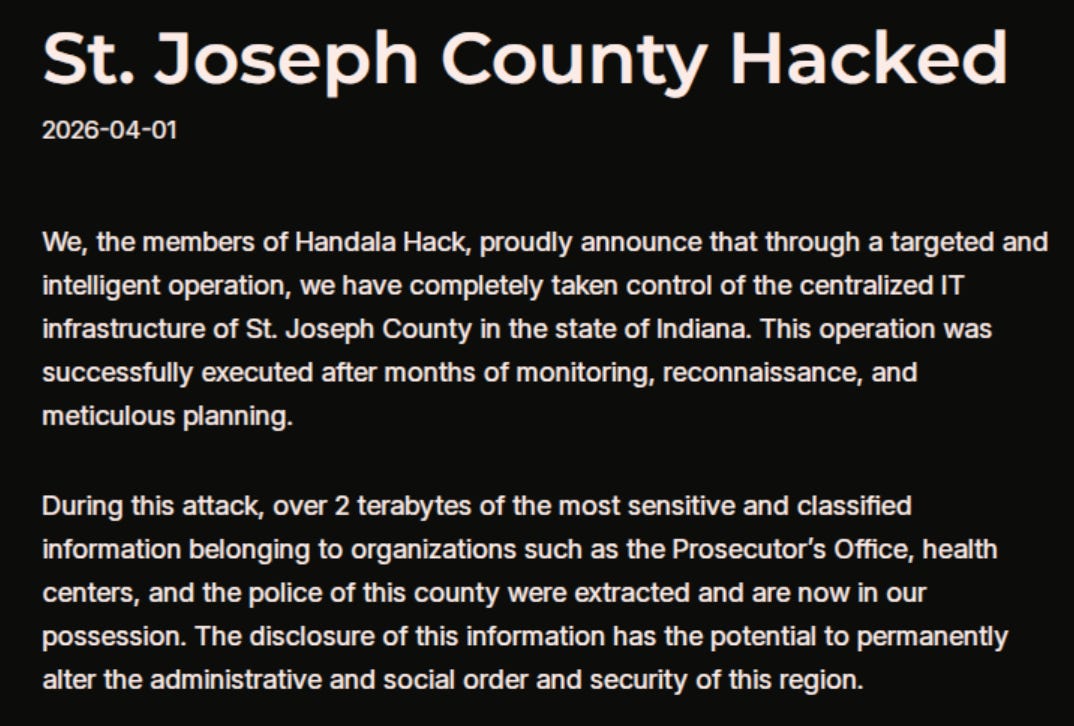
I hate to discuss Handala ad nauseum as well, but they’ve also been engaging in similar shenanigans. They also recently targeted St Joseph county in the US in a similar fashion to past breaches, which is getting them up there with past IRGC intrusions into US infrastructure.
They seem to have nothing of actual value, despite having taken the “most sensitive and classified information” of the good people of St. Joseph’s county, sharing photos of misdemeanor complaints, medical test results, and some lines in a database. The final sentence got me, claiming that the information “has the potential to permanently alter the administrative and social order and security of this region”.
Not to rehash endlessly everything that they do, but Handala has been targeting and deleting data from a number of Israeli companies. Similarly to Anonymous for Justice, they’re also manually deleting files:
As mentioned on MW in the past, they’re also very interested in continuing to recruit Israelis and show no signs of stopping. I’ve seen them use TOX in the past but this may be one of the first times they’ve used Session:
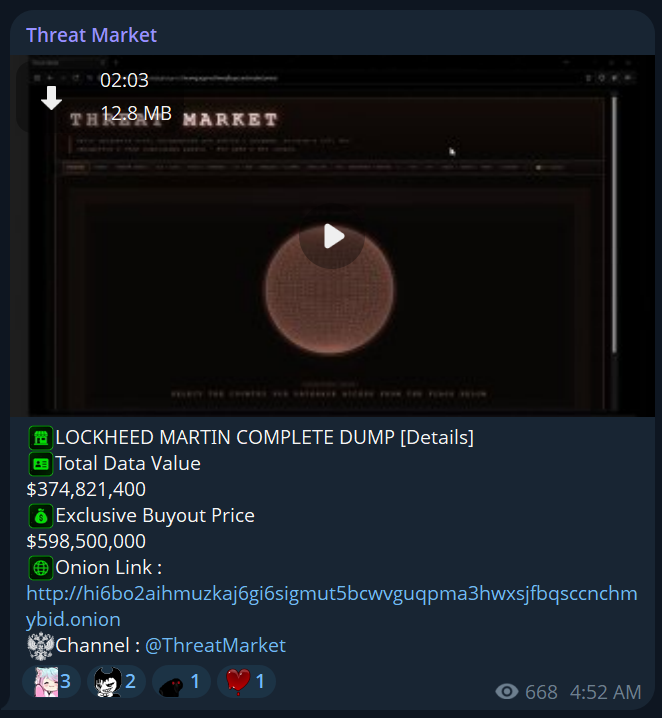
The last thing we’ll discuss is APT Iran’s claim to have exftiltrated 308108 petabytes of data from Lockheed Martin. In reality they only claimed to have stolen a few hundred terabytes, which is equally as unlikely.
I’ve seen some coverage of people saying this is financially motivated, and I am begging you: it is absolutely not. Charging some exorbitant price is all about making it a more appealing news item.
Those of you interested in APT Iran, a fascinating front tied to the IRGC and cyb3rav3ngers, see below:
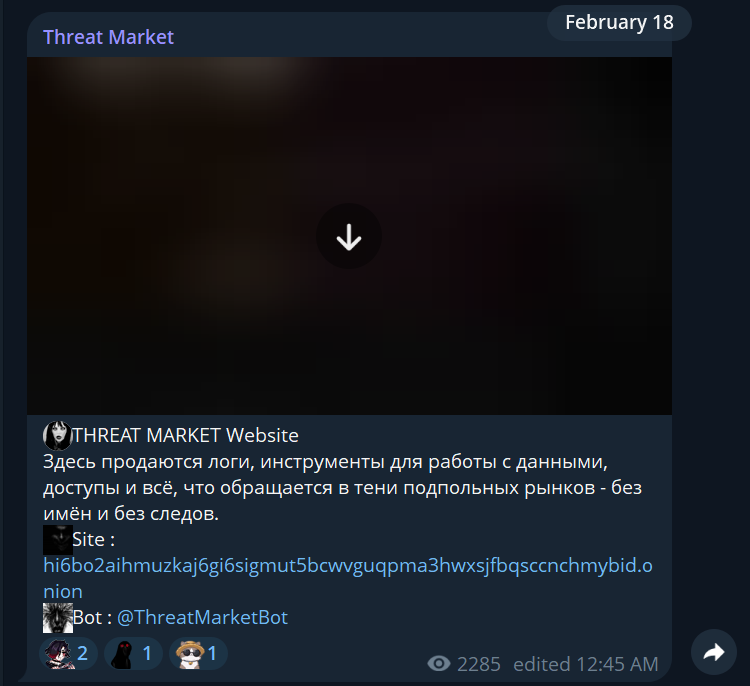
The interesting part here is the creation of ThreatMarket. ThreatMarket is a Russian language channel and Onion site:
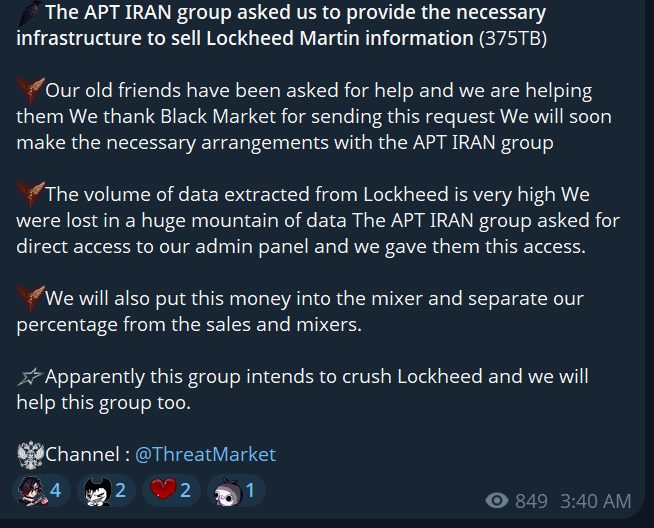
They post in English as well, and claim that APT Iran asked them to sell the data from Lockheed Martin:
They offer the data for sale at a very reasonable 600 million USD ish:
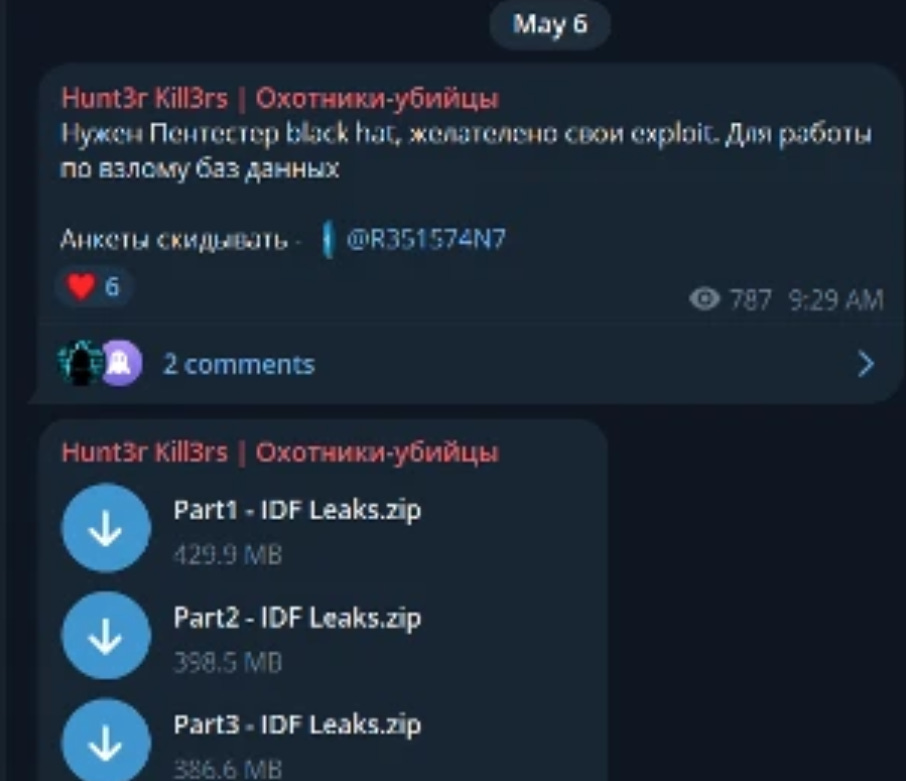
This is absolutely ANOTHER case of Iran impersonating Russian actors for their hacktivist fronts. The MOIS did a very similar thing back in the day with Hunt3r Kill3rs in the IDF Leaks operation:
In fact, it isn’t even the first time that they’ve offered data for sale as part of their IO efforts - see below:
Speaking of Cyber Isnaad Front, some of their previously hacked material is also making headlines now, with some of their old hacked material being now used by Iranian IO efforts apparently (or perhaps grassroots Iranian activity) to allege that an Israeli woman was somehow involved with the US operation in Iran. Funny how these things work out.
That’ll be it for this week, thanks for reading.